- The paper presents a deterministic seven-stage closed-loop pipeline that orchestrates the software lifecycle, ensuring precise state management and strict safety constraints.
- It integrates dual authoritative views with a Jira status contract to manage transitions and prevent concurrency errors while maintaining comprehensive audit trails.
- Empirical results show 100% terminal-state success over 152 runs and a significant reduction in code complexity through consolidated control mechanisms.
Deterministic Closed-Loop Automation for Safe Autonomous Software Lifecycle Orchestration
Introduction and Context
This paper, "Closed-Loop Autonomous Software Development via Jira-Integrated Backlog Orchestration: A Case Study in Deterministic Control and Safety-Constrained Automation" (2604.05000), studies software lifecycle automation from a control-theoretic perspective. The architecture implements a deterministic seven-stage closed-loop control pipeline governing backlog orchestration, integrating structured intake, execution, verification, and publication, framed explicitly as a state-machine with external auditability and formalized safety constraints. AI participation is strictly bounded, providing only supervisory input within explicit policy rails, and every autonomous action is revalidated and auditable.
The context of this work departs from open-ended code generation, focusing on orchestrating multi-surface software lifecycle data (e.g., Jira tickets, design documents, regulatory items) to maintain traceable, reliable system-state evolution under quantifiable safety constraints. The approach is motivated by backlog fragmentation, compliance risk, distributed requirement surfaces, and the absence of systematic closed-loop processes in typical software development automation.
Architectural Design and Control-Theoretic Approach
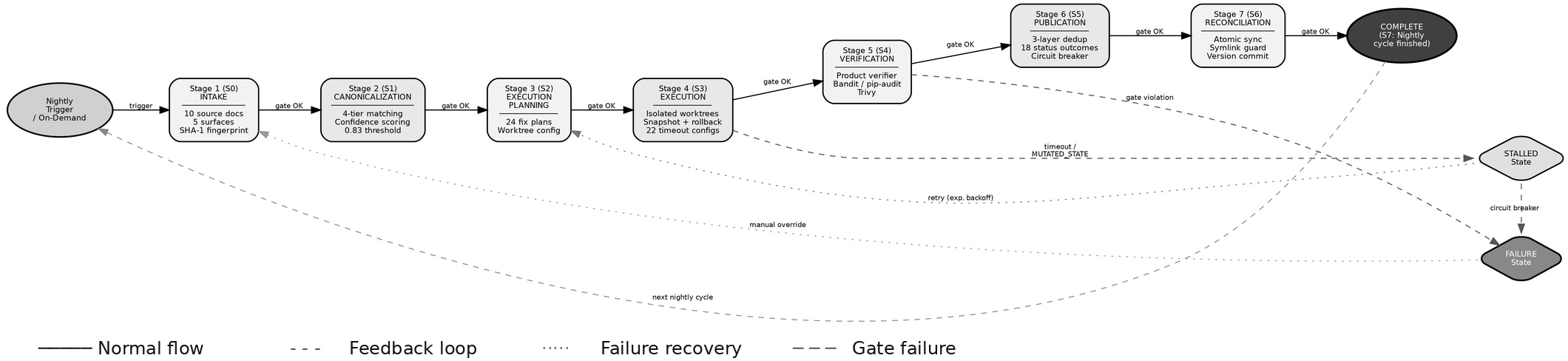
The core system instantiates a formal, seven-stage deterministic pipeline, each stage representing a distinct control state with observable artifacts and explicit advancement criteria. Progression is strictly gated; any failure triggers a deterministic recovery cascade, and each lane operates on a scheduled cadence to maximize process liveness.
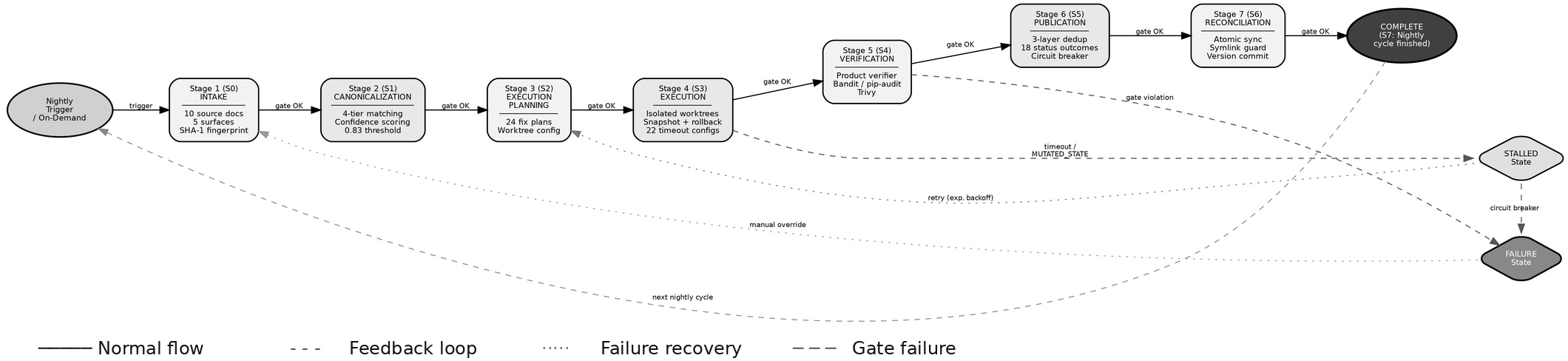
Figure 1: The seven-stage deterministic closed-loop pipeline, with each stage directly tied to success/failure criteria and deterministic recovery.
The pipeline maintains dual authoritative views: a local canonical backlog and a Jira-derived remote status surface. Backlog families are distinctly encoded, and each row synchronizes via bi-directional key assignment, preventing silent drift and duplication.
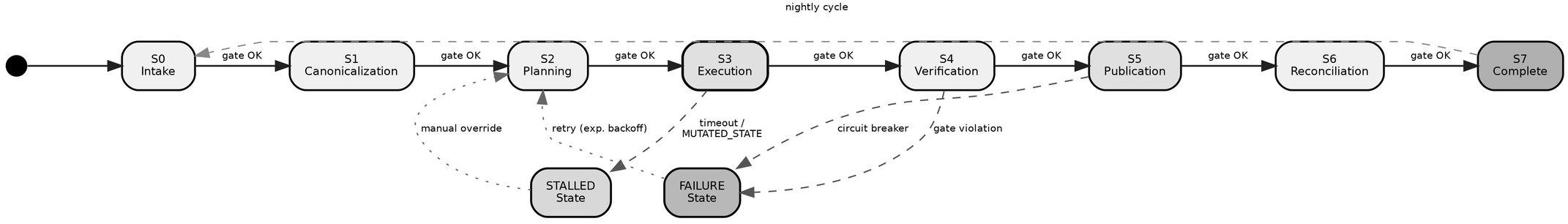
A strict, formal state-machine model underpins the full execution lifecycle. Each state is externally visible, with no hidden transitions or side effects, enabling reliable liveness checks and recovery without reliance on implicit state.
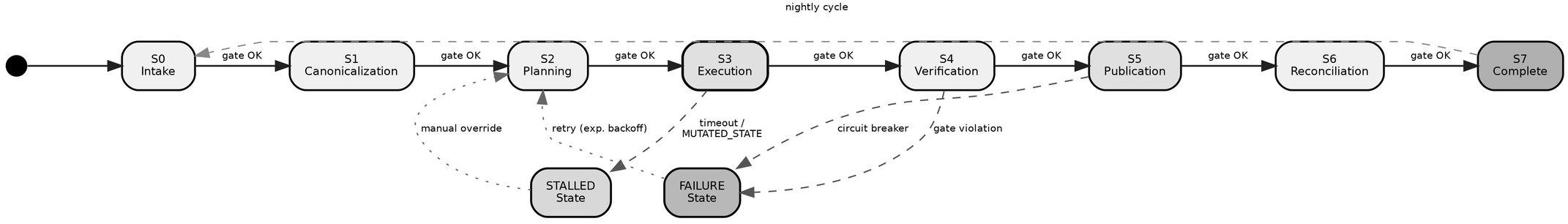
Figure 2: Formal state machine design; S0–S6 correspond to pipeline stages, with deterministic transitions and explicit handling for failures and stalls.
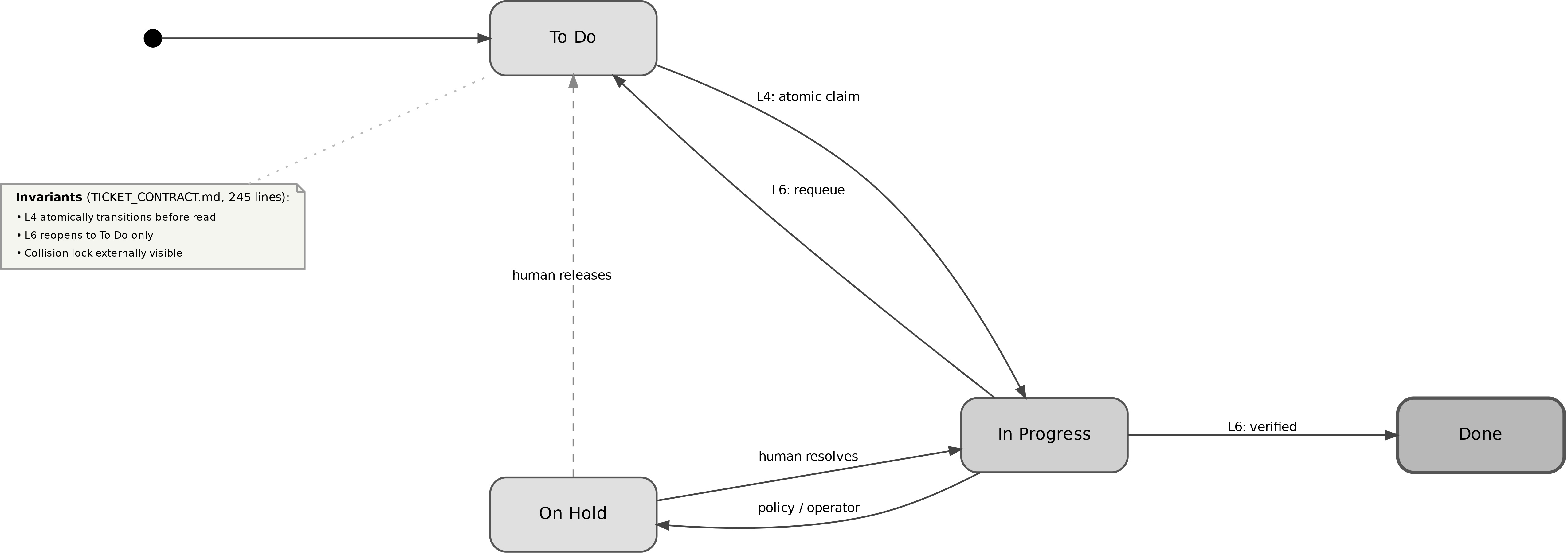
A critical innovation is the Jira Status Contract, specifying four explicit lifecycle states (To Do, In Progress, On Hold, Done) with atomic transitions serving as mutual exclusion locks for concurrent agent control. Lane 4 (execution) acquires exclusive work claims via atomic Jira transitions, and Lane 6 reopens failed tickets only to the intake pipeline, ensuring correct lineage and preventing lock leaks or execution shortcuts.
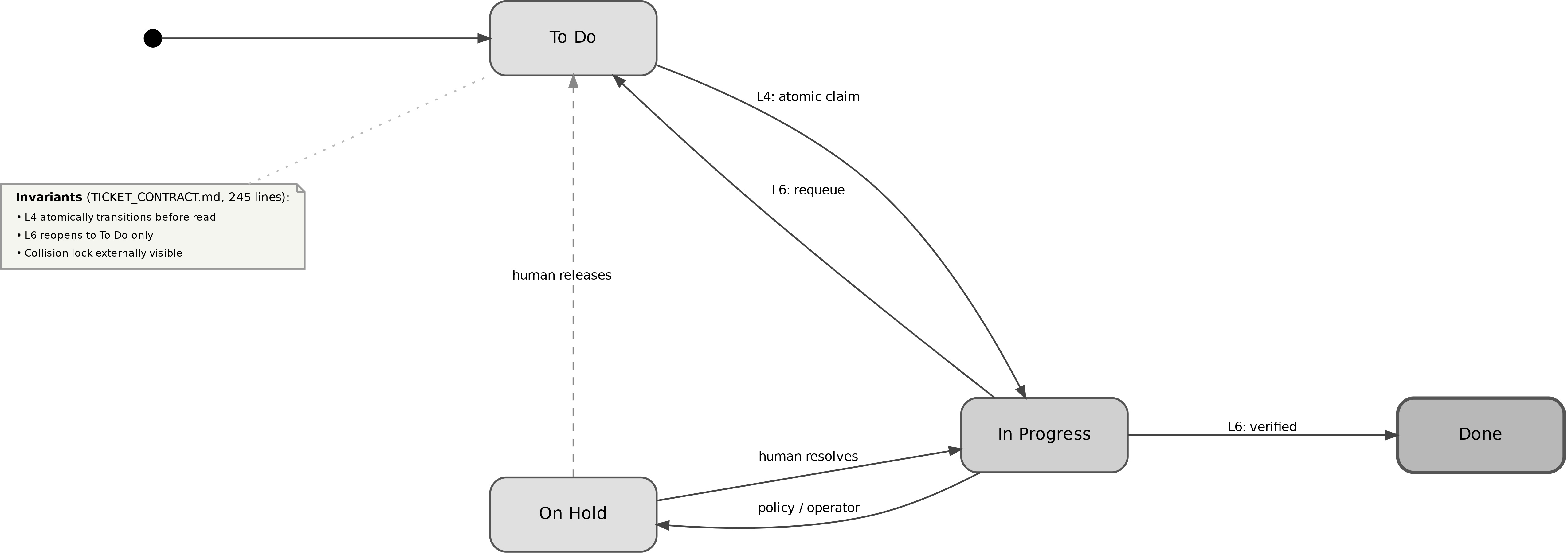
Figure 3: State machine for Jira ticket management; explicit transitions prevent concurrency errors and enforce safety invariants.
Safety, Bounded Autonomy, and Failure Recovery
Safety is implemented using the MANDATE, LATTICE, and TRACE frameworks: all autonomous actions are pre-authorized by an explicit task taxonomy, gated by a continuous confidence score (default autonomous threshold s≥0.83), and all outputs are dual-verified. Execution and verification are strictly separated ("the executor cannot be the auditor" rule). The adversarial code review and formal FMEA processes identified and remediated 51 vulnerabilities, including race conditions, symlink traversal, stale lock risks, and clock skew. The final deployment centralized locks (12 mechanisms, 4 core code paths, 8 reusable patterns) and consolidated lanes, yielding a significant reduction in code and configuration complexity.
Timeouts and checkpoint-based budgets provide liveness guarantees. Degraded-mode protocols ensure recovery from Jira outages, with all pending work and publication intents stored for atomic replay upon restoration of upstream APIs. The fallback system guarantees that degraded operation and recovery are fully auditable, preventing information loss or duplicate actions during disruption windows.
AI is embedded as a non-generative, bounded supervisory layer. Each call is version-controlled, context-packaged, rate-limited, and diff-capped, with explicit handoff to human review for ambiguous or large changes.
Quantitative Results and Evaluation
The initial evaluation window comprised 152 runs, achieving 100% terminal-state success (95% CI: [97.6%, 100%]). Subsequently, the system transitioned to continuous operation, accumulating over 795 run artifacts. Nightly DEGRADED status (79.3% runs) primarily reflected dependency-audit informational alerts, not functional failures; all runs completed with correct terminal state.
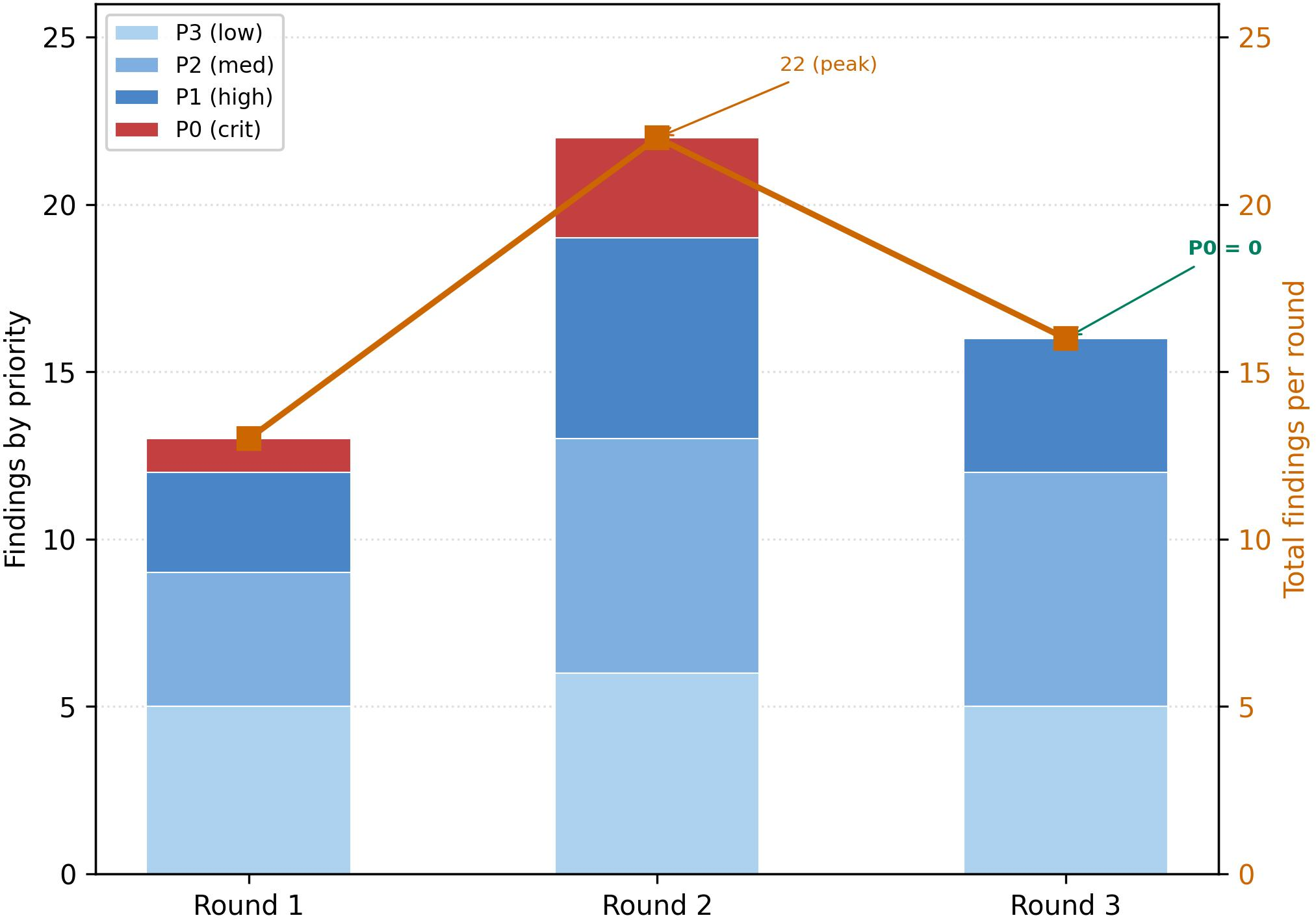
The adversarial code review, based on a STRIDE model, injected 51 findings across three rounds, all of which were closed during the study. Zero false negatives were observed among the author-injected test set. The security ticket family case study saw 6 out of 10 items fully autonomously completed (with autonomous dispatch, monitoring, and verification), 2 requiring human remediation, and 2 closed by policy. The explicit boundary on autonomy was strictly enforced by confidence tiers and task family scope.
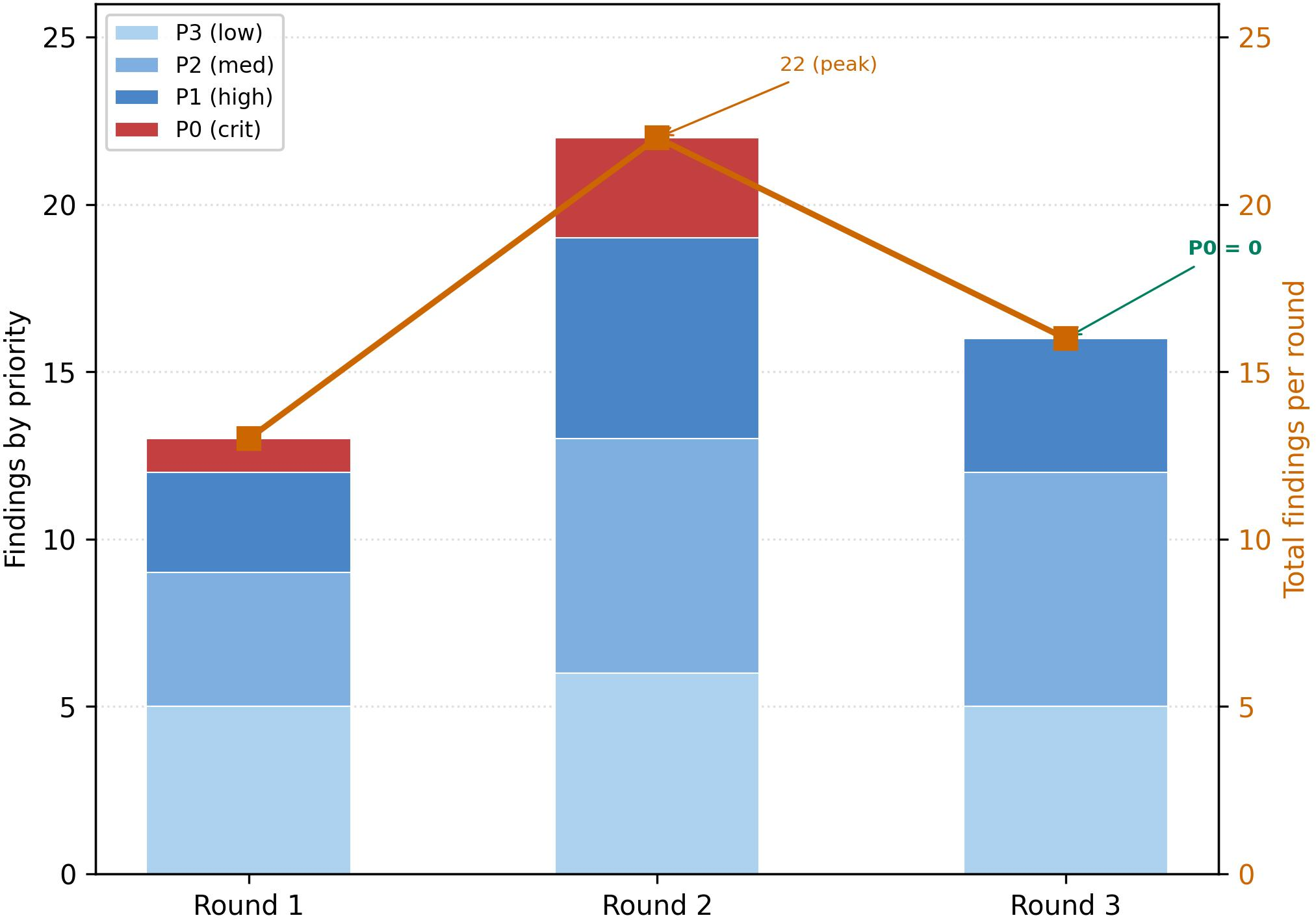
Figure 4: P0-critical adversarial findings peaked in round 2, verifying second-order vulnerability coverage; round 3 achieved zero P0 findings.
Consolidated infrastructure yielded a 45% script-line reduction (from 22,946 to 12,661 LOC), and lock/control complexity dropped correspondingly. Infrastructure density stabilized at 1.52% of the application baseline (1.29M LOC), reflecting concentrated, maintainable control-plane code.
Compliance, Auditability, and Observability
The system enforces complete deterministic audit trails, with receipt-chain logging, hash-linked evidence artifacts, and per-state run identifiers. Jira transitions embed permalinks to evidence logs, supporting direct traceability. Separation of canonical and collaborative surfaces (backlog vs. Jira) enables resilience to external state corruption or manipulation.
Conservative status alignment ensures that automation always fails safe: ambiguous or borderline-confidence results default to human review and never to unsupervised action.
Practical and Theoretical Implications
This work empirically demonstrates that robust, bounded autonomous lifecycle orchestration is practical given explicit state modeling, lock-based mutual exclusion, confidence-thresholded autonomy, and defense-in-depth recovery and audit protocols. The bounded-autonomy control model and explicit evidence chain provide practical safety without formal proofs, with empirical closure of all known injection vulnerabilities during the pilot.
The architectural consolidation—from 11 single-purpose automation lanes to 7 multi-capability lanes—demonstrates significant maintainability and auditability gains without sacrificing reliability. The explicit policy, gating, and feedback patterns instantiate a model-agnostic control structure, suggesting generalizability across differing AI toolchains or underlying LLM capabilities.
Future work includes full lock contention validation, degraded-mode field testing under real-world outages, formal verification of the state-machine properties, and extension to cross-repository and multi-agent coordination.
- Figure 1: Seven-stage closed-loop control pipeline
- Figure 3: Jira status contract state machine
- Figure 2: Formal pipeline state machine
- Figure 4: P0 adversarial findings trends
Conclusion
The paper demonstrates—through direct deployment, analysis, and adversarial review—that explicit closed-loop control, stateful gating, bounded AI autonomy, multi-mechanism failure recovery, and tamper-evident audit chains can achieve quantifiably reliable autonomous software lifecycle management. The boundary between what can be safely automated is enforced through data-driven confidence thresholds and explicit policy, not end-to-end code generation. This control-theoretic, safety-constrained approach is directly transferable to other domains requiring deterministic reliability, auditability, and bounded autonomy, and provides a model for integrating AI in critical system workflows without compromising traceability, safety, or human oversight.