AgentOS: From Application Silos to a Natural Language-Driven Data Ecosystem
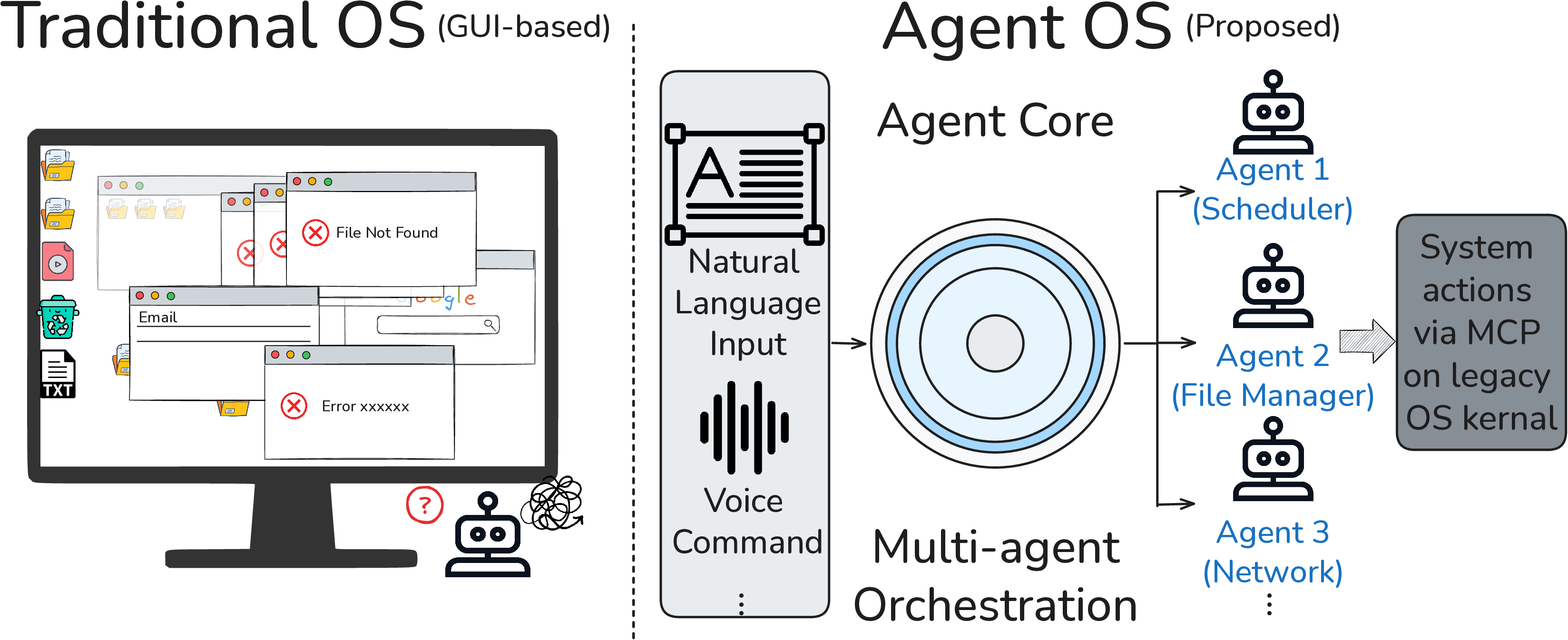
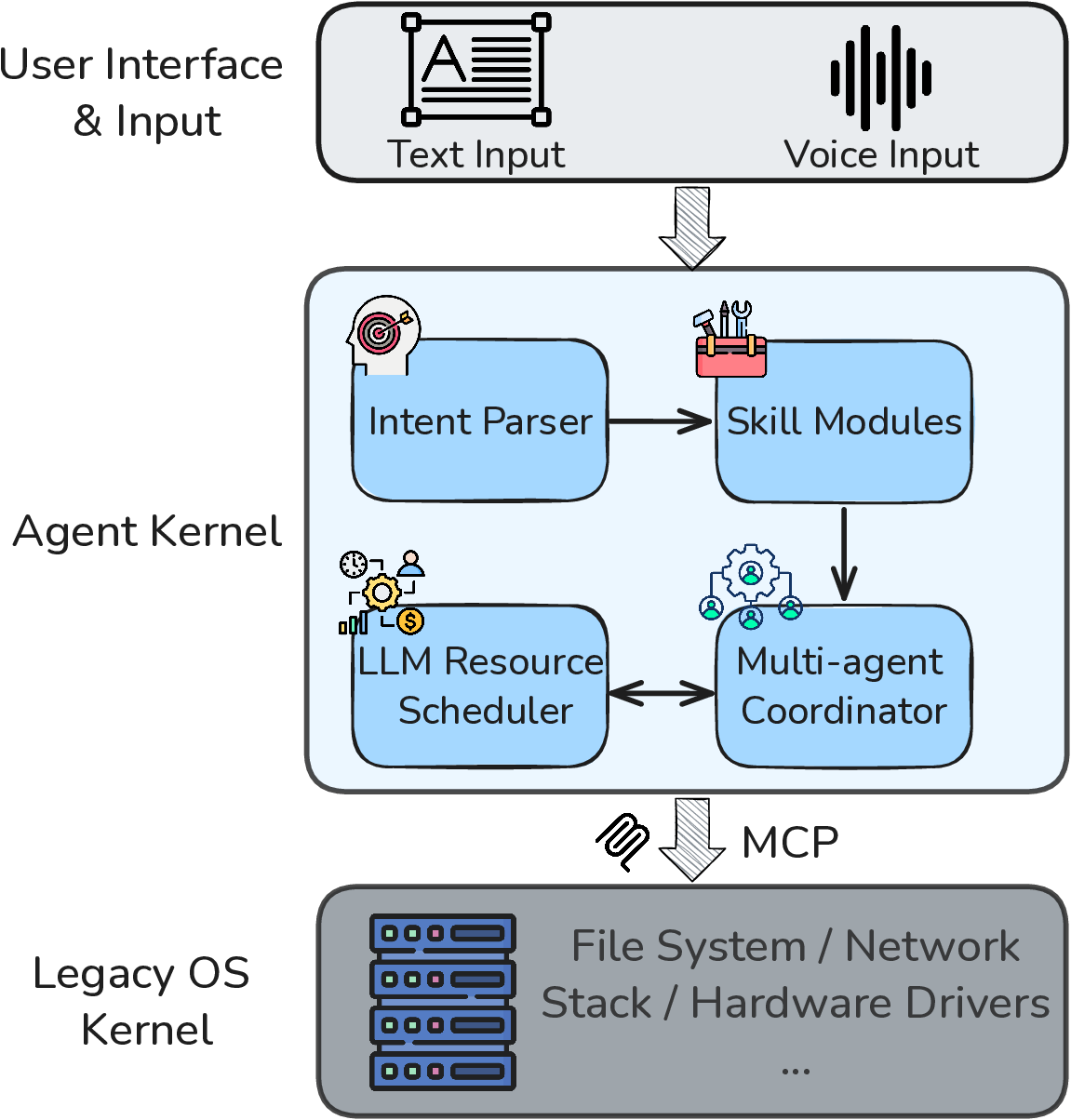
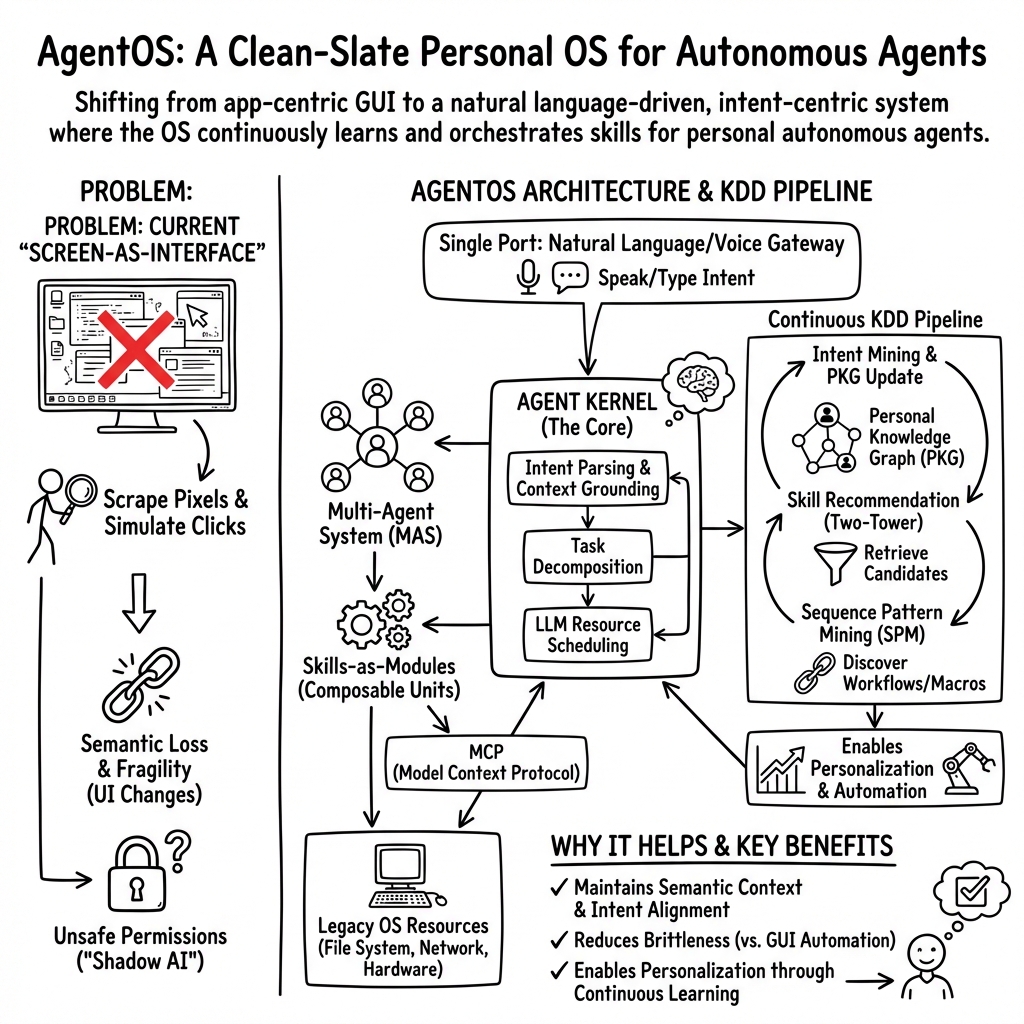
Abstract: The rapid emergence of open-source, locally hosted intelligent agents marks a critical inflection point in human-computer interaction. Systems such as OpenClaw demonstrate that LLM-based agents can autonomously operate local computing environments, orchestrate workflows, and integrate external tools. However, within the current paradigm, these agents remain conventional applications running on legacy operating systems originally designed for Graphical User Interfaces (GUIs) or Command Line Interfaces (CLIs). This architectural mismatch leads to fragmented interaction models, poorly structured permission management (often described as "Shadow AI"), and severe context fragmentation. This paper proposes a new paradigm: a Personal Agent Operating System (AgentOS). In AgentOS, traditional GUI desktops are replaced by a Natural User Interface (NUI) centered on a unified natural language or voice portal. The system core becomes an Agent Kernel that interprets user intent, decomposes tasks, and coordinates multiple agents, while traditional applications evolve into modular Skills-as-Modules enabling users to compose software through natural language rules. We argue that realizing AgentOS fundamentally becomes a Knowledge Discovery and Data Mining (KDD) problem. The Agent Kernel must operate as a real-time engine for intent mining and knowledge discovery. Viewed through this lens, the operating system becomes a continuous data mining pipeline involving sequential pattern mining for workflow automation, recommender systems for skill retrieval, and dynamically evolving personal knowledge graphs. These challenges define a new research agenda for the KDD community in building the next generation of intelligent computing systems.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Explain it Like I'm 14
What is this paper about?
This paper imagines a new kind of computer operating system called AgentOS. Instead of you clicking apps and menus, you mostly talk or type what you want in plain language, and a smart AI “head agent” understands your goals and gets things done by coordinating smaller helper skills. The big idea: your computer should behave more like a helpful teammate you talk to, and less like a pile of separate apps you have to manage yourself.
What questions is the paper trying to answer?
The authors ask:
- How can we replace today’s app-by-app, window-clicking world with one simple, natural language portal you can talk to?
- What would the “brain” of such a system look like so it can understand your intent, break tasks into steps, and pick the right tools?
- How do we keep this safe and reliable when the system is powered by AI, which can make mistakes?
- Which data and AI techniques are needed to make this work in real time for each person?
How does the proposed system work? (Methods and key ideas)
Think of AgentOS as a team with clear roles:
- The Single Port: This is the one main place where you talk to your computer (by voice or text). Instead of hunting for the right app, you just say what you need: “Plan my trip for next week,” or “Summarize that report and email my teacher.”
- The Agent Kernel (the “head agent”): This is the system’s brain. It:
- Understands your request (figures out your intent).
- Breaks big tasks into smaller steps.
- Chooses the right helper skills to run those steps.
- Manages AI resources (like a traffic cop making sure AI tools don’t overload or run out of memory).
- Skills-as-Modules (the “Lego pieces”): Instead of installing huge apps, you build or reuse small skills that do specific things (like “extract totals from invoice PDFs” or “update a budget sheet”). You can even “program” new skills by describing them in plain language, and the system turns that into a reusable rule.
To make all this possible, the paper says the operating system needs to use data science every minute, not just old-fashioned code. Here are the main techniques, explained simply:
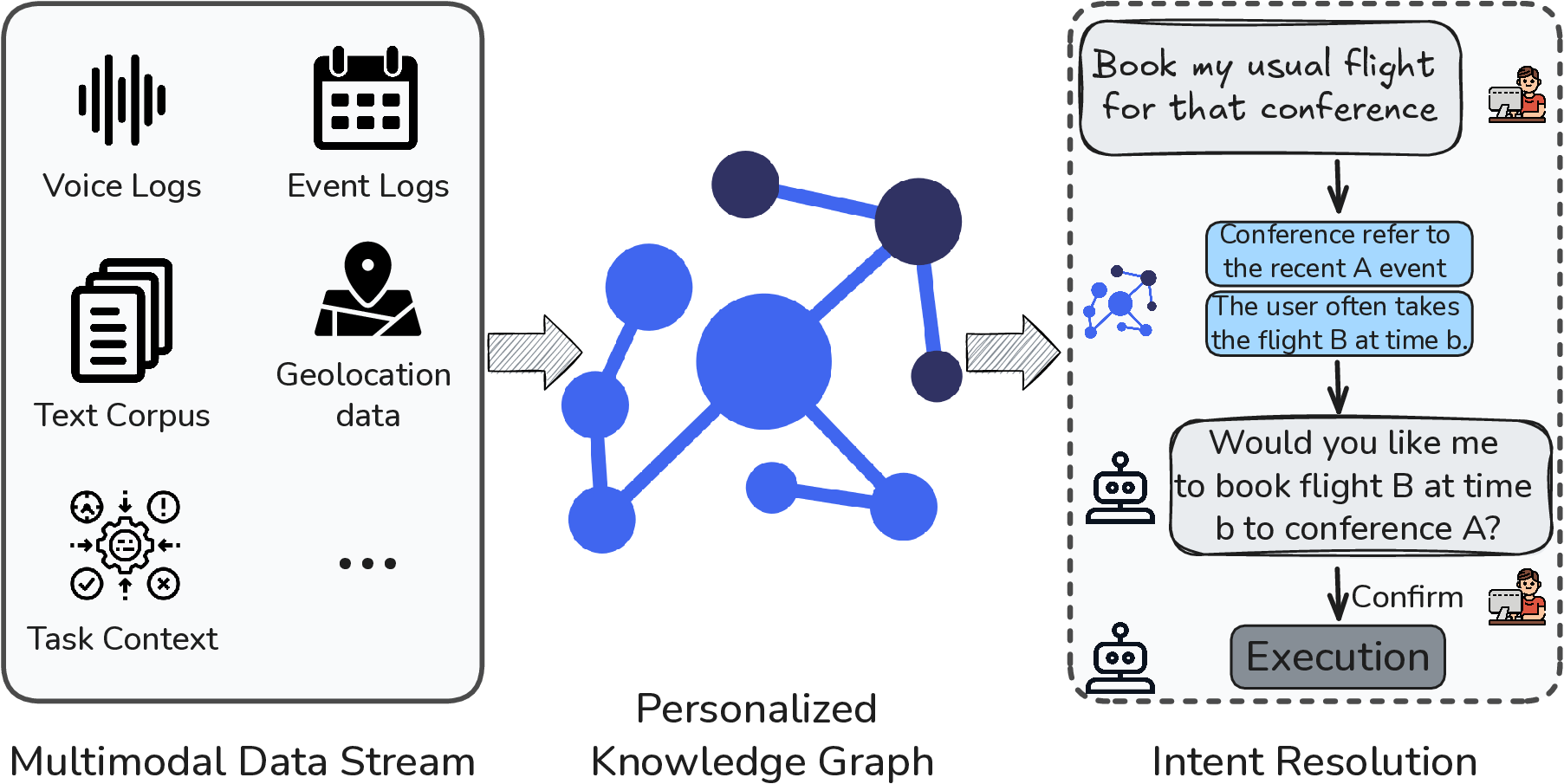
- Intent Mining: Turning messy human requests into clear, step-by-step plans. For example, “Book my usual flight for that conference” means the system looks at your past flights, your calendar, and the conference details to figure out what “usual” means.
- Personal Knowledge Graph: A private, evolving “map” of your world—your contacts, preferences, files, past actions, and habits. This helps the system guess what you mean without asking you 10 follow-up questions every time.
- Skill Recommendation: Like Netflix recommending shows, but for tools. The system picks the best skills (and the right sequence of them) to solve your task based on your request and your history.
- Pattern Mining: The system watches which steps you repeat and learns to automate them. If you always rename and file documents the same way, it can turn that routine into a one-click or no-click background service.
- New Evaluation Metrics: Instead of measuring “CPU usage” or “frames per second,” the system measures whether it did what you actually wanted (“intent alignment”), how often it needed to ask for clarification, and how accurate its tool choices were.
What are the main findings or proposals, and why are they important?
This is a vision paper—more of a blueprint than a report of experiments. Its big proposals are:
- Replace the desktop full of windows with a “single conversation” interface: talking to your computer becomes the main way to use it. This could make everyday computing much simpler and faster.
- Build an Agent Kernel that treats understanding people as its main job: Instead of just managing programs, the OS manages your goals and coordinates helper agents to achieve them.
- Turn apps into skills: Small, composable building blocks you can combine like Lego. You can make skills by describing rules in natural language.
- Treat the entire OS as a live data-mining system: Constantly learning from your behavior to understand intent, recommend the right skills, and automate routines safely.
- Redefine safety: Add a “Semantic Firewall” that checks not just who is asking for data, but why. This helps block sneaky attacks hidden in emails or web pages that try to trick the agent (like “indirect prompt injections”).
- Control mistakes and recover fast: Because AI can “hallucinate” (make things up), the system needs sandboxes (safe playpens) and a “time machine” (fast rollback) to undo bad actions in seconds.
These ideas matter because today’s AI assistants are squeezed into old operating systems that were built for mouse clicks and screens, not for autonomous agents. That causes fragile behavior (like reading pixels instead of real data), messy permissions (“Shadow AI” that can access too much), and lots of context loss. AgentOS is a clean redesign for the AI era.
What could this change in the real world?
If built well, AgentOS could:
- Make computers far easier to use: You explain what you want; the system handles the rest across files, web, email, and tools without you juggling apps.
- Save time by learning your routines: Repeated workflows turn into reliable automations.
- Create a safer AI-powered environment: The Semantic Firewall and quick rollback reduce risks from mistakes and attacks.
- Open new research and jobs: It sets a research agenda for data mining and AI—like better ways to model personal context, recommend toolchains, evaluate “intent alignment,” and secure agent systems.
In short, the paper’s message is: the future operating system should understand you. To do that, it must be built around natural language, a smart agent brain, and always-on learning from your data (with strong safety). This could turn computers into truly helpful partners instead of a maze of apps and settings.
Knowledge Gaps
Knowledge gaps, limitations, and open questions
The paper proposes an ambitious vision for AgentOS but leaves many technical, empirical, and governance aspects unspecified. The following concrete gaps highlight actionable directions for future research:
- Lack of an end-to-end prototype and empirical validation of AgentOS; no measurements of latency, accuracy, reliability, or user productivity vs. legacy GUIs.
- Unspecified formal “intent schema” for the Northbound interface (typing, versioning, compositional structure, uncertainty representation) and how intents map to executable plans.
- No algorithmic design for LLM resource scheduling (fairness, priority, preemption, QoS isolation, admission control) under token budgets and API rate limits.
- Missing policies for model selection and placement (on-device vs. cloud) balancing latency, cost, privacy, and energy; no adaptive switching criteria.
- Discoverability and learnability of a “Single Port” NUI are unaddressed; lack of fallback/parallel GUIs for tasks requiring multi-window work or precise spatial manipulation.
- Multimodal disambiguation remains unspecified (e.g., integrating voice, gaze, environment state); when/how to query for clarification vs. act autonomously.
- No formal data model for Personal Knowledge Graphs (PKGs): entity/relationship schemas, temporal dynamics, uncertainty, provenance, and versioning.
- PKG lifecycle and governance are unclear: data ingestion pipelines, user consent, redaction/“right to be forgotten,” cross-device sync, and portability across vendors.
- Cold-start personalization is not operationalized: how to rapidly bootstrap Z2H2 personalization with minimal user burden and robust privacy guarantees.
- Absence of bias, fairness, and representational harm analysis in intent mining and personalization across languages, cultures, and accents.
- Skill-as-Module lifecycle is undefined: packaging, dependency management, versioning, updates, and deprecation policies.
- Trust and provenance of skills are unaddressed: signing, attestation, supply-chain security, and curated vs. open ecosystems.
- Missing capability-based permission model for skills and agents (least privilege, scope, duration), and a runtime policy engine for dynamic intent-aware enforcement.
- No formal verification or static analysis framework to prove safety properties of skills and multi-agent plans before execution.
- Skill composition semantics are unspecified: state sharing, data schema interoperability, conflict resolution, and transactional guarantees across composed skills.
- Observability and debugging tools are absent: standardized traces of agent reasoning and actions, step-by-step replay, explainability to users, and privacy-preserving logs.
- Criteria for promoting mined action sequences into automated macros/services are undefined (confidence thresholds, human-in-the-loop approval, rollback plans).
- Handling non-stationarity and concept drift in sequential pattern mining and recommenders is unaddressed; no continuous learning and forgetting mechanisms.
- Datasets and protocols for training and evaluating skill recommenders are missing (feedback signals, exploration-exploitation, off-policy evaluation, counterfactuals).
- Safety-aware recommendation is not specified: how to enforce policy constraints and reject unsafe/ambiguous skill selections at retrieval and planning time.
- Evaluation lacks standardized benchmarks: shared task suites, ground-truth labels for Intent Alignment (IA), multi-turn task complexity, and cross-user comparisons.
- No robust hallucination detection/escalation framework (thresholds, intervention policies, human confirmation for high-risk actions, kill-switch mechanisms).
- Rollback strategy is incomplete: snapshot granularity, performance overhead, and handling of irreversible or external side effects (emails sent, funds transferred) via compensating actions.
- Semantic Firewall design is underspecified: concrete detection models, adversarial robustness, false positive/negative trade-offs, and latency impact under real workloads.
- Integration of the Semantic Firewall with OS-level information flow control is unspecified (labeling, taint propagation, declassification policies, formal security proofs).
- Privacy-preserving telemetry for learning (e.g., federated learning, differential privacy) is not addressed, including consent, retention, and local vs. server-side processing.
- Multi-user and enterprise contexts are unexplored: role-based access control, separation of duties, delegation, policy hierarchies, MDM integration, and auditing/compliance.
- Internationalization and accessibility gaps: multilingual NUI, code-switching, speech impairments, noisy environments, and non-voice modalities for users with disabilities.
- Energy and cost budgets are not quantified for continuous intent mining and agent orchestration on resource-constrained devices; no green-computing strategies.
- Interoperability/standards are unformed: precise specifications of MCP and “Semantic APIs,” schema registries, and vendor-neutral protocols for cross-ecosystem portability.
- Resilience to external dependency drift (web/app updates, API changes) is not designed beyond abandoning “screen-as-interface”; need DOM- and API-robust planning and fallbacks.
- Offline and degraded modes are unspecified: capabilities without network access, local model fallbacks, and graceful degradation policies.
- Real-time and safety-critical use cases lack guarantees: bounded-latency scheduling, priority inversion avoidance, and certifiable behaviors for time-sensitive tasks.
- Governance and ethical boundaries of proactivity are undefined: preventing manipulation/persuasion, attention hijacking, and setting/monitoring autonomy limits with user control.
- Liability and compliance questions remain open: action provenance, audit trails for regulatory regimes (e.g., GDPR, HIPAA), and assignation of responsibility for agent-caused harm.
- Migration path is unclear: incremental deployment on legacy OSes, hybrid GUI+NUI models, developer SDKs/tooling, and strategies for user adoption at scale.
- Human factors are underexplored: mental models for an intent-driven OS, trust calibration, error recovery UX, training/onboarding, and long-term user behavior changes.
Practical Applications
Practical applications of AgentOS: from vision to deployment
Below we translate the paper’s architectural concepts (Single Port NUI, Agent Kernel, Skills-as-Modules, Personal Knowledge Graphs, Sequential Pattern Mining, LLM resource scheduling, Semantic Firewall, and rollback) into concrete, real-world use cases. We group them by deployment horizon and note sectors, prospective tools/products/workflows, and key assumptions or dependencies.
Immediate Applications
These can be piloted or deployed today by composing existing local agents (e.g., OpenClaw), MCP connectors, RAG, DLP, container sandboxes, and OS snapshotting.
- Personal and SMB workflow automation (email, calendar, files)
- Sectors: software, SMB finance, education, general consumers
- What: Natural-language skill rules like “When an invoice PDF arrives, extract total, check the spreadsheet, draft a payment authorization.”
- Tools/products/workflows:
- Skill builder UI (NL → skill JSON/code), skill library, MCP connectors for Gmail/Outlook, Sheets/Excel, Drive/SharePoint
- Background agent scheduling with logs and human-in-the-loop approvals
- Assumptions/dependencies: Provider APIs (vs. GUI-only), permissioned service accounts, reliable OCR/structured extraction, DLP in place
- Enterprise “Single Port” assistant overlay (chat/voice-first portal over existing apps)
- Sectors: enterprise software, contact centers, sales/CRM
- What: Natural language portal to invoke skills across CRM/ERP/IT without screen scraping, surfacing visual UI only when needed
- Tools/products/workflows:
- Teams/Slack app or desktop tray app with NUI, MCP bridges to Salesforce, ServiceNow, SAP; embedding-based skill retrieval
- Assumptions/dependencies: Stable APIs, access controls per role, telemetry/observability for audit
- Accounts payable/receivable copilot with DLP
- Sectors: finance, accounting
- What: Invoice ingestion, ledger matching, approval drafting, with outbound-leak checks
- Tools/products/workflows:
- Invoice parser skill, ERP connectors (NetSuite, SAP), “Semantic Firewall” middleware for prompt/action vetting
- Assumptions/dependencies: ERP API availability, PII redaction, anomaly workflows for exceptions
- IT/DevOps agent orchestrator with rollback
- Sectors: software, cloud/DevOps
- What: NL-driven runbooks (deploy, rollback, rotate keys), enforced sandboxes and OS snapshots
- Tools/products/workflows:
- Agent Kernel-like controller calling Terraform/Kubernetes/CI via MCP; APFS/Btrfs/ZFS snapshots; change logs and approvals
- Assumptions/dependencies: Infrastructure-as-code adoption, snapshot performance/coverage, policy gates
- Contact center and back-office copilots
- Sectors: telecom, retail, logistics
- What: Case triage, knowledge lookup, form-filling via APIs (not pixel automation), orchestrated skill chains
- Tools/products/workflows:
- Two-tower retrieval for skill selection; clarifying prompts; agentic evaluation checklist (e.g., ABC) before rollout
- Assumptions/dependencies: Quality knowledge base, clear escalation, latency budgets
- PKG-lite personalization for learners and knowledge workers
- Sectors: education, enterprise L&D, research
- What: Preferences/history store to tailor study plans, note extraction, meeting summaries
- Tools/products/workflows:
- Local PKG store (calendar, documents, course data), RAG over personal corpus, privacy consent UI
- Assumptions/dependencies: User consent and data portability; cold-start defaults; on-device or private cloud options
- Sequential Pattern Mining for macro suggestions
- Sectors: RPA/automation, enterprise IT
- What: Mine user/agent action logs to recommend time-saving macros for repeated sequences
- Tools/products/workflows:
- SPM over terminal/app/API traces; suggested “one-click” automations published as new skills
- Assumptions/dependencies: Access to logs with proper anonymization; noise filtering; user approval
- Semantic Firewall and data loss prevention for agent workflows
- Sectors: finance, healthcare admin, legal, government
- What: Real-time prompt/input sanitization, taint tracking, outbound entity leakage prevention
- Tools/products/workflows:
- Middleware between NUI and tools; policy packs per sector; allow/deny with rationale
- Assumptions/dependencies: Named-entity and intent classifiers with low false positives; policy tuning; audit trails
- LLM resource scheduling for multi-agent teams
- Sectors: platform/IT, SaaS, contact centers
- What: Token/latency/rate-limit budgeting across concurrent agent threads
- Tools/products/workflows:
- Scheduler service integrated with Kubernetes/queues; SLM fallback and caching; per-tenant quotas
- Assumptions/dependencies: Multi-model access, offline cache, rate-limit awareness
- Governance for “Shadow AI” in enterprises
- Sectors: policy/compliance, IT governance
- What: Capability-scoped permissions, action logs, user-visible approvals, IA-oriented QA before deployment
- Tools/products/workflows:
- Capability registry (skills, scopes), intent-aligned checklists, tri-agent review in staging
- Assumptions/dependencies: Organizational buy-in; central policy store; change-management processes
- Home/IoT natural-language automations (via Home Assistant or similar)
- Sectors: consumer IoT, robotics (lightweight)
- What: “If rainy tomorrow, delay vacuum and reschedule garden watering;” composable home skills
- Tools/products/workflows:
- MCP connectors to Home Assistant/Matter; schedule executor; consent prompts
- Assumptions/dependencies: Device API compatibility; offline/on-device options for privacy
- Academic tooling and benchmarks
- Sectors: academia (CS/KDD/HCI)
- What: Tri-Agent evaluation, IA metrics, PKG prototypes, SPM datasets on interaction logs
- Tools/products/workflows:
- Open benchmark suites; simulators (AndroidArena); reproducible pipelines
- Assumptions/dependencies: Ethical logging, IRB approvals, standardized metrics
Long-Term Applications
These require deeper OS integration, standardization, improved reliability/safety, or broader ecosystem adoption.
- Full AgentOS desktop replacement (Single Port as default UI)
- Sectors: consumer OS, enterprise endpoints
- What: NUI-first computing with traditional GUI secondary; Agent Kernel mediating intents to skills and system calls
- Tools/products/workflows:
- Agent Kernel SDK, signed skill ecosystem, OS-level MCP/Semantic API, secure enclaves for LLMs
- Assumptions/dependencies: Vendor OS cooperation or new OS; user acceptance of NUI; robust fallbacks and a11y
- Semantics-based authorization (“intent-aware permissions”)
- Sectors: security, compliance, public sector
- What: Replace coarse app permissions with semantic gating of high-privilege actions
- Tools/products/workflows:
- Policy-as-skills; formalized intent schemas; provenance/attestation of skills; risk-scored approvals
- Assumptions/dependencies: Reliable intent inference; formal verification; regulator guidance
- Continuous, privacy-preserving Personal Knowledge Graphs
- Sectors: healthcare, education, enterprise productivity
- What: Real-time, multimodal PKGs powering hyperpersonalization and disambiguation
- Tools/products/workflows:
- Federated/siloed PKG sync; differential privacy; on-device inference; user transparency controls
- Assumptions/dependencies: Data portability standards; consent frameworks; secure graph storage
- Self-evolving skill ecosystems (auto-synthesized skills/services)
- Sectors: software, RPA, IT ops
- What: SPM + RL generate new skills from observed patterns; dynamic optimization of workflows
- Tools/products/workflows:
- Skill provenance and signing; sandbox execution; performance/reliability scoring
- Assumptions/dependencies: Safe code synthesis; human oversight initially; approval markets/marketplaces
- Sector-specific AgentOS distributions
- Healthcare: EHR-integrated agent OS for scheduling, clinical documentation assistance, prior auth
- Dependencies: FDA/HIPAA compliance, audited models, clinician oversight, fine-grained DLP
- Finance: Trading ops, reconciliation, regulatory reporting with semantic firewalls
- Dependencies: Model risk management (SR 11-7 analogs), auditability, secure enclaves
- Education: Campus AgentOS for enrollment, advising, personalized tutoring
- Dependencies: FERPA compliance, LMS APIs, bias monitoring
- Internet of Agents across organizations and devices
- Sectors: energy, logistics, smart cities, manufacturing
- What: Cross-agent collaboration (IoA) with federated PKGs, secure inter-agent contracts
- Tools/products/workflows:
- Interoperability standards, identity and trust frameworks, cross-domain policy enforcement
- Assumptions/dependencies: Open protocols beyond MCP, federated trust, performance SLAs
- Robotics and embodied systems orchestration
- Sectors: home robotics, warehousing, healthcare robotics
- What: Agent Kernel plans across IT + physical tasks, coordinating bots and information systems
- Tools/products/workflows:
- Semantic skill APIs for robots, simulation-in-the-loop, collision-safe planners with NL intents
- Assumptions/dependencies: Reliable perception/planning; safety certifications; real-time constraints
- On-device/mixed-edge LLMs with OS-level scheduling
- Sectors: mobile, embedded, automotive
- What: Energy-aware token budgeting, local SLMs + burst-to-cloud, privacy-preserving inference
- Tools/products/workflows:
- Model distillation/quantization, NPU scheduling, adaptive caching
- Assumptions/dependencies: Hardware NPUs, robust fallback strategies, cost models
- Regulatory and standards frameworks for agentic OS
- Sectors: policy, standards bodies
- What: IA metrics in procurement, certification of skill safety, logging/audit standards for agent actions
- Tools/products/workflows:
- Public benchmarks, incident reporting taxonomies, conformance suites
- Assumptions/dependencies: Multi-stakeholder consensus; mapping to existing regimes (e.g., NIST AI RMF, ISO/IEC)
- Cognitive checkpointing and speculative execution with instant rollback
- Sectors: OS vendors, cloud platforms
- What: OS-level “cognitive snapshots” to unwind erroneous agent trajectories in milliseconds
- Tools/products/workflows:
- Cross-layer snapshots (file system + app state + agent context), speculative task branches
- Assumptions/dependencies: Low-overhead snapshot tech; unified state models; correctness detection
- Marketplace for verified skills with provenance and economic incentives
- Sectors: software platforms, app stores
- What: Signed skills, safety labels, usage metering, revenue share; enterprise-private catalogs
- Tools/products/workflows:
- Skill signing, SBOMs for logic, dynamic trust scores, vulnerability scanning
- Assumptions/dependencies: Developer ecosystem; trust infrastructure; liability frameworks
- Smart grid and industrial control copilots (semantic orchestration)
- Sectors: energy, manufacturing
- What: Intent-driven control suggestions, alarm triage, maintenance scheduling via semantics-aware agents
- Tools/products/workflows:
- Digital twin integration, robust guardrails, human-in-the-loop control rooms
- Assumptions/dependencies: High-assurance safety layers; real-time constraints; certified fail-safes
- City planning and public services orchestration
- Sectors: government, urban planning
- What: Multi-agent planning for permits, route optimization, public feedback synthesis
- Tools/products/workflows:
- Geospatial skills, dependency-aware execution (“city editing”), transparency/audit pipelines
- Assumptions/dependencies: Data-sharing agreements; public accountability; bias/fairness reviews
Cross-cutting assumptions and dependencies
- Reliability and safety of LLMs/agents: Requires hallucination mitigation, robust clarifications, and bounded autonomy with human oversight.
- API-first ecosystems: Feasibility improves dramatically where systems expose stable APIs; GUI-only apps remain brittle.
- Privacy/security: Semantic Firewall effectiveness, DLP, taint tracking, and encrypted storage are prerequisites for sensitive domains.
- Evaluation and governance: Adoption hinges on IA-centered benchmarks, auditability, and organizational change management.
- Compute and cost: Token budgets, caching, on-device inference, and resource scheduling are essential for cost-effective scale.
- Standards and interoperability: Broad value emerges with common protocols for skills, intents, and inter-agent trust.
Glossary
- Access Control Lists (ACLs): A permission mechanism that specifies which principals can access which resources and operations. "Legacy operating systems rely on static permissions and deterministic Access Control Lists (ACLs), where applications either possess access to a resource or they do not."
- Agent Kernel: The intelligent core layer that interprets user intent, decomposes tasks, and orchestrates agents and resources. "The system core becomes an Agent Kernel that interprets user intent, decomposes tasks, and coordinates multiple agents"
- AgentOS: A proposed agent-centric operating system paradigm driven by natural language and multi-agent orchestration. "This paper proposes a new paradigm: a Personal Agent Operating System (AgentOS)."
- Agentic Benchmark Checklist (ABC): A structured evaluation suite for testing agentic AI systems on multi-turn tasks. "Tri-Agent evaluation, AndroidArena simulations, Agentic Benchmark Checklist (ABC)"
- Agentic loop: A self-directed cycle where an agent plans, acts, observes, and updates memory to pursue long-horizon goals. "Through an autonomous agentic loop, it maintains long-term memory and executes long-horizon tasks with minimal supervision"
- AndroidArena: A simulation environment used for benchmarking agent behavior and task performance. "simulation environments (e.g., AndroidArena)"
- Btrfs: A copy-on-write Linux file system supporting snapshots for rapid state restoration. "By leveraging underlying file systems (like ZFS or Btrfs variants), the OS must maintain fine-grained snapshots."
- Data exfiltration: Unauthorized transfer of sensitive information out of a system. "(e.g., indirect prompt injection leading to data exfiltration)"
- Data Loss Prevention (DLP): Techniques that monitor and block leakage of sensitive data during outbound actions. "Real-Time Data Loss Prevention (DLP):"
- Graph-augmented reasoning: Using knowledge graph structure to enhance inference and disambiguation. "the Agent Kernel performs graph-augmented reasoning over the PKG"
- Indirect Prompt Injection: A malicious instruction embedded in external content that coaxes an agent to perform harmful actions. "an Indirect Prompt Injection in an email"
- Intent Alignment (IA): A metric assessing how well system actions match a user’s underlying goals. "Intent Alignment (IA), task completion rate, tool invocation accuracy"
- Intent mining: Extracting and structuring user goals from ambiguous, multimodal inputs. "a real-time engine for intent mining and knowledge discovery."
- Knowledge Discovery and Data Mining (KDD): The field focused on extracting insights and patterns from data; positioned as foundational to AgentOS. "We argue that realizing AgentOS fundamentally becomes a Knowledge Discovery and Data Mining (KDD) problem."
- LLM resource scheduling: Allocating limited LLM-related resources (context, tokens, rate limits) across concurrent agent tasks. "Crucially, the Agent Kernel must also perform large-scale LLM resource scheduling."
- LLM-as-a-judge: Using an LLM as an evaluator to assess outputs or interactions. "an evaluator agent (LLM-as-a-judge)"
- Markovian Intrinsic Reward Adjustment (MIRA): A learning-based reward modeling method for evaluating agent behaviors. "Markovian Intrinsic Reward Adjustment (MIRA)"
- Model Context Protocol (MCP): A protocol through which agents access tools, files, and system services in a structured manner. "with the Model Context Protocol (MCP), OpenClaw functions as a persistent background agent"
- Multi-Agent System (MAS): A coordinated collection of agents that decompose and execute subtasks collaboratively. "An internal Multi-Agent System (MAS) decomposes user requests into executable sub-tasks"
- Natural User Interface (NUI): An interaction paradigm centered on natural language, voice, and multimodal inputs instead of GUIs. "a Natural User Interface (NUI) centered on a unified natural language or voice portal."
- Northbound Interface: The Agent Kernel’s user-facing interface that parses and structures intents from multimodal inputs. "Northbound Interface (Intent Translation):"
- Personal Knowledge Graph (PKG): A user-specific, semantically rich graph capturing preferences, history, and relationships for personalization. "AgentOS requires continuous construction and querying of a Personal Knowledge Graph (PKG)"
- Retrieval-Augmented Generation (RAG): Enhancing generation by retrieving relevant external knowledge or documents. "through Retrieval-Augmented Generation and behavioral profiling."
- Screen-as-Interface: A brittle paradigm where agents operate by scraping pixels or simulating GUI actions. "Screen-as-Interface"
- Semantic API: An interface layer exposing meaning-rich operations rather than low-level system calls. "Model Context Protocol (MCP), Semantic API"
- Semantic Firewall: A security layer that vets inputs/outputs for malicious intent and prevents unsafe actions. "AgentOS requires a Semantic Firewall"
- Sequential Pattern Mining (SPM): Discovering frequent subsequences in temporal logs to optimize and automate workflows. "Sequential Pattern Mining (SPM)"
- Single Port: The unified, persistent natural language/voice gateway replacing the traditional desktop. "a unified interaction gateway referred to as the Single Port"
- Skills-as-Modules: Modular, composable user-defined capabilities expressed and installed via natural language. "modular Skills-as-Modules enabling users to compose software through natural language rules."
- Southbound Interface: The Agent Kernel’s infrastructure-facing interface for orchestrating tools and system resources. "Southbound Interface (Multi-Agent Orchestration):"
- State Rollback: A mechanism to reverse erroneous actions by restoring prior system snapshots. "Most critically, the OS requires a robust, system-level \"State Rollback\" mechanism."
- Taint-Aware Memory: A protection model that tracks and restricts the influence of untrusted data on high-privilege operations. "Taint-Aware Memory and Cognitive Integrity:"
- Tool orchestration: Dynamically selecting and composing tools or skills to execute complex workflows. "This process resembles tool orchestration in agentic AI systems, where complex workflows are constructed by dynamically selecting and composing specialized tools or modules."
- Tri-Agent framework: An evaluation setup with clarification, response, and evaluator agents to assess intent alignment and dialog quality. "the Tri-Agent framework introduces a clarification agent, a response agent, and an evaluator agent (LLM-as-a-judge)"
- Two-Tower Recommendation Architecture: A retrieval model with separate user/context and item/skill encoders mapped into a shared space. "A natural solution is a Two-Tower Recommendation Architecture."
- ZFS: A copy-on-write file system supporting snapshots, used for rapid recovery. "By leveraging underlying file systems (like ZFS or Btrfs variants), the OS must maintain fine-grained snapshots."
- Zero-shot-to-head-shot hyperpersonalization (Z2H2): A framework for rapidly adapting systems from no prior data to highly personalized behavior. "The Zero-shot-to-head-shot hyperpersonalization (Z2H2) framework offers one implementation pathway"
Collections
Sign up for free to add this paper to one or more collections.