- The paper introduces a lifecycle-aware framework that validates and governs upgrades for embodied agent capabilities with staged safety checks.
- The methodology employs multi-dimensional compatibility evaluations—covering interface, policy, behavioral, and recovery aspects—to prevent unsafe activations.
- Experimental results demonstrate significantly improved safety and rollback efficiency compared to naïve upgrade methods in simulated embodied environments.
Governed Capability Evolution for Embodied Agents
Introduction and Motivation
Embodied agent systems increasingly require iterative, continuous capability advancement—demanding robust upgrade and evolution mechanisms that do not compromise safety, policy adherence, or recoverability. While modular packaging, capability evolution, and runtime governance have each seen focused research, the admission and deployment of new, potentially incompatible capability module (ECM) versions remain an underaddressed systems problem. "Governed Capability Evolution for Embodied Agents: Safe Upgrade, Compatibility Checking, and Runtime Rollback for Embodied Capability Modules" (2604.08059) formalizes this as a first-class governance challenge in embodied AI, arguing for a lifecycle-aware upgrade framework that manages capability evolution from candidate validation through to deployment and rollback, with explicit attention to policy constraints, interface fidelity, behavioral drift, and system recoverability.
Lifecycle-Aware Governed Upgrade Architecture
The framework presented systematizes ECM evolution as a staged pipeline. Each new candidate version is not immediately promoted to the active set, but is subject to:
- Candidate Registration: Admission into a managed registry, decoupled from direct execution.
- Compatibility Validation: Four dimensions—interface (κI), policy (κP), behavioral (κB), recovery (κR)—are checked. Each dimension is independently composable and admits only fully compliant candidates.
- Sandbox Evaluation: Isolated, canonical task execution with perturbations, to capture basic safety and failure modes.
- Shadow Deployment: Parallel execution in live contexts; candidates receive inputs but do not control actuators, facilitating detection of regressions that sandboxing cannot reveal.
- Gated Activation: Conditional system integration, profile- and authority-sensitive.
- Online Monitoring: Continuous trace-based anomaly, violation, and performance drift detection post-activation.
- Rollback and Demotion: Automated restoration of prior ECM versions on policy or behavioral violation, with full auditability.
This lifecycle is operationalized via a finite-state machine, with explicit candidate transitions between registry, evaluation, deployment, monitoring, deferral, and recovery states—ensuring no candidate bypasses mandated governance boundaries.
Compatibility Model and Deployment Safety
The authors present a precise, multi-dimensional compatibility function for each ECM upgrade. Rather than a monolithic acceptance gate, the model is explicitly partitioned:
- Interface Compatibility (κI): Signature, invocation schema, pre/post-conditions, and external dependencies are statically verified. Incompatibility leads to immediate rejection.
- Policy Compatibility (κP): The module's complete permission profile is validated against active execution policies and the deployment context (Γt). Insufficient coverage or policy-escape risk flags conditional or review-bound progression.
- Behavioral Compatibility (κB): Empirical behavioral signatures comprised of success, retry, anomaly, and recovery statistics are compared against the previous version’s envelope, with drift or volatility demoting the candidate.
- Recovery Compatibility (κR): Rollback/fallback functions, safe-abort hooks, and failure-mode detectability are individually checked to preserve recoverability guarantees.
Candidates must satisfy all four dimensions for activation. The pipeline supports conditional progression (sandbox, shadow), allowing observation and profiling before any candidate is granted control authority.
Experimental Outcomes
The framework is evaluated in a PyBullet-based manipulation testbed (with ROS2 middleware):
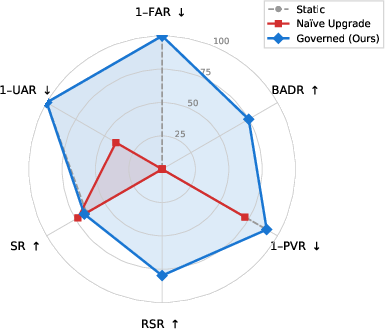
- Naïve Upgrade (direct replacement) achieves 72.9% final task success, but unsafe activation escalates to 60% and eventually 100% in late rounds—a demonstrable breakdown in policy adherence, trace stability, and recoverability.
- Governed Upgrade maintains a comparable final success rate (67.4%) but eradicates unsafe activations, with zero instances observed across 15 seeds and 6 rounds. Statistical tests show safety improvements are significant at p=0.003 for unsafe activation, with only a small non-significant performance reduction (κP0).
- Shadow Deployment surfaces 40% of regressions not visible in isolated sandboxing, intercepting retry instabilities, policy-drift, and timeouts under live input conditions.
- Rollback is effective in 79.8% of post-activation drift scenarios, critical for maintaining operational safety in the presence of unpredictable runtime behavior.
These results are robust across three deployment profiles (simulation, strict runtime, human-shared), each with profile-specific gating and authority requirements.
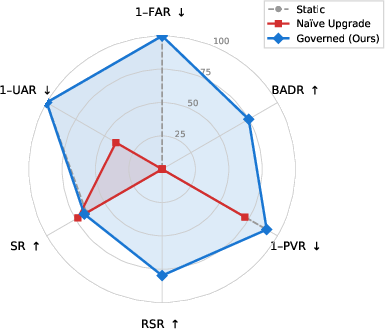
Figure 1: Governance profile comparison shows only Governed Upgrade (blue) provides simultaneous coverage of safety, screening, false-accept control, and rollback; Naïve Upgrade (red) collapses to unsafe activation; Static deployment (gray, dashed) is trivially safe but cannot evolve capabilities.
Ablation and Failure Mode Analysis
Comprehensive ablations demonstrate that the efficacy of governed upgrade emerges from the composition of its modular controls:
- Removing shadow deployment allows 6% unsafe activation and fails to intercept live-context regressions.
- Disabling recovery compatibility significantly degrades rollback effectiveness (RSR drops to 58.3% from 79.6%).
- Eliminating online monitoring results in persistent exposure to post-activation drift and delayed intervention.
- Bypassing sandboxing increases both false acceptance and unsafe activation.
- Static compatibility alone is inadequate for upgrade safety—behavioral and recovery checks are irreplaceable.
Further, governance-layer failures (incomplete assessment, monitor blind spots, distributional shifts, or rollback unavailability) are identified as explicit research and operational risks, warranting second-order governance of the governance layer itself.
Theoretical and Practical Implications
Modularity and System OS Principles
The work generalizes beyond modular embodied agents: The framework is applicable to both modular ECM deployments and monolithic checkpoint/model upgrades (e.g., RT-2, RT-X), provided executables remain distinctly versioned and admit behavioral signature analysis. Its design philosophy aligns with OS principles: version registries, shadowing, explicit profiling, and rollback are treated as core system lifecycle constructs, not safety addenda.
DevOps and MLOps Boundary
While the pipeline draws on established principles (staged rollout, canary, audit logging), the embodied regime demands semantic, trace-driven compatibility, physical safety constraints, and authority/recovery modeling unavailable in DevOps/MLOps. Governance here is more than container orchestration—it is behavioral and systems-level admission control inherently tied to the execution substrate.
Human Oversight and Multi-Profile Adaptation
The governance pipeline supports context-sensitive deployment, including human oversight, approval channels, and environment-specific activation policies, all of which are essential in both safety-critical robotics and mixed-initiative deployment settings.
Limitations and Future Directions
Evaluation in PyBullet simulation limits exposure to hardware-specific timing, drift, or recovery faults; the transition to real hardware would sharpen both the thresholds and the practical forms of compatibility/recovery checks. Current scope is single-system, three-family, and modest candidate pool; scaling to fleet-level, high-throughput, and large-capability systems will require further architectural innovations, including distributed upgrade coordination and richer capability type systems. Behavioral and recovery compatibility methods rely on empirical thresholding; formalized verification and model-based synthesis are open research questions. Human authority modeling and complex profile orchestration are currently simplified.
Conclusion
This work advances governed capability evolution as a rigorous, lifecycle-aware deployment discipline for embodied agent systems. By structuring capability admission as a series of explicit, composable gates covering interface, policy, behavioral, and recovery dimensions—and supporting provisional, monitored, and revertible activation—it achieves the dual objective of enabling continuous embodied skill improvement without sacrificing deploy-time safety, policy compliance, or recoverability. These principles and mechanisms, implemented and empirically validated, mark governed capability evolution as a central systems problem for future embodied intelligence, relevant not only to robotics but to any domain where modular, upgradable, and safety-critical agent capabilities must be evolved under bounded control.