Security Analysis of Agentic AI Communication Protocols: A Comparative Evaluation
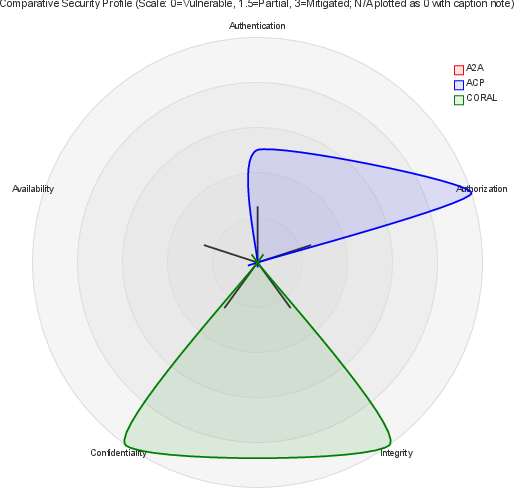
Abstract: Multi-agent systems (MAS) powered by AI are increasingly foundational to complex, distributed workflows. Yet, the security of their underlying communication protocols remains critically under-examined. This paper presents the first empirical, comparative security analysis of the official CORAL implementation and a high-fidelity, SDK-based ACP implementation, benchmarked against a literature-based evaluation of A2A. Using a 14 point vulnerability taxonomy, we systematically assess their defenses across authentication, authorization, integrity, confidentiality, and availability. Our results reveal a pronounced security dichotomy: CORAL exhibits a robust architectural design, particularly in its transport-layer message validation and session isolation, but suffers from critical implementation-level vulnerabilities, including authentication and authorization failures at its SSE gateway. Conversely, ACP's architectural flexibility, most notably its optional JWS enforcement, translates into high-impact integrity and confidentiality flaws. We contextualize these findings within current industry trends, highlighting that existing protocols remain insufficiently secure. As a path forward, we recommend a hybrid approach that combines CORAL's integrated architecture with ACP's mandatory per-message integrity guarantees, laying the groundwork for resilient, next-generation agent communications.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Explain it Like I'm 14
Overview
This paper looks at how AI “agents” talk to each other and how safe those conversations are. Think of AI agents like digital teammates that pass messages, share tasks, and sometimes handle money or personal info. The authors compare three popular ways (called “protocols”) for agents to communicate—A2A, CORAL, and ACP—to see where they’re strong and where they’re weak.
Goals in simple terms
The researchers wanted to answer a few straightforward questions:
- Which agent-to-agent communication protocols are actually secure in real life?
- What kinds of security problems show up most often?
- How do design decisions (the blueprint) compare with real-world code (the actual build)?
- What can be done to make these systems safer, especially when agents share sensitive data or payments?
Methods and approach
The authors used a 14-point checklist of common security risks to test the protocols. You can think of this like inspecting a house by checking doors, windows, locks, alarms, and fire exits.
They focused on five big areas of security:
- Authentication: Proving who you are (like showing an ID).
- Authorization: What you’re allowed to do (like which rooms your key opens).
- Integrity: Making sure messages aren’t changed on the way (like sealed envelopes).
- Confidentiality: Keeping secrets safe (like curtains and safes).
- Availability: Making sure the system stays up and usable (like backup power).
What they did:
- They tested CORAL’s official implementation (the real software people can use).
- They built and tested a high-quality version of ACP using official tools (SDKs).
- They evaluated A2A based on published information and prior studies (instead of testing a live system).
- They checked how tokens, signatures, encryption, and streaming updates worked, and tried to break them in realistic ways (for example, replaying old messages or impersonating a trusted agent).
They also looked at the difference between:
- Architecture: The design choices and rules on paper.
- Implementation: The actual code and configuration people run.
Main results
CORAL
- Big picture: CORAL’s design is strong. It does a good job with message checking and keeping sessions separate, and it integrates blockchain for payments.
- Problem: The public CORAL setup had serious weaknesses at its “SSE gateway” (a streaming connection used for live updates), including failures in authentication and authorization. In plain terms, some doors were locked by design, but the installed locks weren’t working right.
ACP
- Big picture: ACP is flexible and easy to use in many setups.
- Problem: Some important safety features (like message signatures called JWS) are optional. If people don’t turn these on strictly, attackers can tamper with messages or snoop on data. Flexibility is great—unless it lets people skip locks they really need.
A2A
- Big picture: A2A follows common web standards and is good for agent discovery and task delegation.
- Problem: Prior work suggests gaps in handling sensitive data, weak control over how long tokens stay valid, and not enough fine-grained permissions. That means agents might keep using “passes” for too long or get broader access than they actually need.
Why these results matter
- The study found a clear pattern: Good designs don’t always lead to good, secure installations. And making security features optional makes it easy to set things up in an unsafe way.
- Today’s agent protocols still aren’t secure enough for tasks involving personal data, identity documents, or payments without careful configuration and testing.
Implications and impact
The authors recommend a hybrid approach:
- Use CORAL’s strong, integrated architecture (which handles payments and session separation well).
- Combine it with ACP’s per-message integrity guarantees (make signatures and checks mandatory every time a message is sent).
What this means for the future:
- Safer AI teamwork: Agents will be better at proving who they are, only doing what they’re allowed to do, and keeping messages secret and intact.
- Fewer costly mistakes: Mandatory checks reduce data leaks, fraud, and replayed actions.
- Clearer standards: Moving from “optional security” to “required security” helps everyone build safer systems by default.
In short, if we treat agent messages like valuable packages—always sealed, always signed, and only deliverable to the right person—AI systems can collaborate more safely and reliably.
Knowledge Gaps
Knowledge Gaps, Limitations, and Open Questions
Below is a single, actionable list of what remains missing, uncertain, or unexplored in the paper’s analysis and proposals.
- Empirical evaluation of A2A is literature-based only; no hands-on testing of an A2A implementation under the unified threat model.
- Configuration coverage for ACP is limited to non-strict setups; systematic testing with mandatory JWS, mTLS, different SDKs, and hardened server configurations is missing.
- Generalizability of CORAL findings is unclear; only one public CORAL implementation and version were tested, with no cross-release or multi-deployment replication.
- No quantitative assessment of security–performance trade-offs (latency, throughput, resource overhead), especially for CORAL’s blockchain interactions and ACP’s per-message JWS.
- The proposed hybrid approach lacks a formal specification, reference design, and security proof; no prototype or empirical validation of the hybrid’s end-to-end security.
- Interactions of multiple concurrent threats (e.g., prompt injection + replay + privilege escalation) were not empirically benchmarked under combined scenarios.
- Consent and transparency mechanisms are discussed but not operationalized or measured; no user-centered evaluation of consent fatigue, auditing efficacy, or data minimization outcomes.
- Token lifetime, rotation, and revocation enforcement remain unspecified across protocols; a standardized, cross-protocol anti-replay scheme (timestamps, nonces, distributed revocation) is absent.
- CORAL SSE gateway authentication/authorization failures are reported without root-cause analysis, reproducible exploit details, patch verification, or regression testing plans.
- Off-chain CORAL session membership validation is not formally specified or empirically validated; access control to threads, streams, and artifacts remains ambiguous.
- ACP multipart MIME canonicalization and signature coverage are not detailed; risk of signature bypass due to inconsistent canonicalization across compound messages remains unaddressed.
- Key management practices (rotation cadences, compromise recovery, inter-agent trust anchors) are not standardized; integration paths for KMS, DID–OAuth bridging, and hardware-backed keys are unexplored.
- Practical MITM resilience under misconfigured TLS/mTLS (pinning, mutual auth, downgrade resistance) was not tested; real-world misconfiguration scenarios remain open.
- Availability and DoS resilience are not measured; rate limiting, backpressure (SSE/WebSocket), circuit breakers, and blockchain outage handling need benchmarking.
- ACP offline/edge operation security is not analyzed; conflict resolution, delayed revocation propagation, clock skew, and eventual consistency impacts are unknown.
- Protocol-level side-channel/model-output leakage was not empirically assessed; end-to-end leakage testing in multi-agent exchanges is missing.
- Reproducibility artifacts (code, configs, test harnesses, datasets/attack scripts) are not provided; independent validation and extension by other researchers are impeded.
- The threat model excludes stronger adversaries (LLM compromise, supply-chain tampering, insider threats); sensitivity of findings to expanded adversarial capabilities is untested.
- Spoofing in discovery/registry mechanisms (CWE-290) is introduced but not empirically evaluated; risks of agent registry poisoning, manifest forgery, and endpoint impersonation remain open.
- Compliance mapping (GDPR/PSD2) is not formalized; concrete protocol controls for consent logging, purpose limitation, audit trails, and deletion/erasure guarantees are undefined.
- SCA for high-risk operations (payments, identity sharing) is not designed or tested across A2A and ACP; viable MFA/ZKP integration paths and enforcement policies are absent.
- Governance for the hybrid approach is not addressed; standardization roadmap, conformance test suites, migration guidance, and interop criteria are needed.
- Prompt-injection defenses at the protocol layer (content signing, provenance, policy filters) are not specified or evaluated; canonical mitigations and test cases are lacking.
- Replay detection in streaming (SSE) is not detailed; per-event IDs, timestamps, windowing strategies, and replay cache effectiveness are unmeasured.
- Evaluation scale and statistical rigor are unclear; number of scenarios, attack runs, success rates, and confidence intervals are not reported.
Glossary
- A2A: Google’s agent-to-agent protocol enabling secure, interoperable communication and task delegation among autonomous agents. "The Agent-to-Agent (A2A) protocol, introduced by Google, defines an identity-aware framework for secure, interoperable communication among autonomous AI agents."
- ABAC (Attribute-Based Access Control): An access control model where permissions are determined by attributes of users, resources, or context. "including Attribute-Based Access Control (ABAC) and Role-Based Access Control (RBAC)"
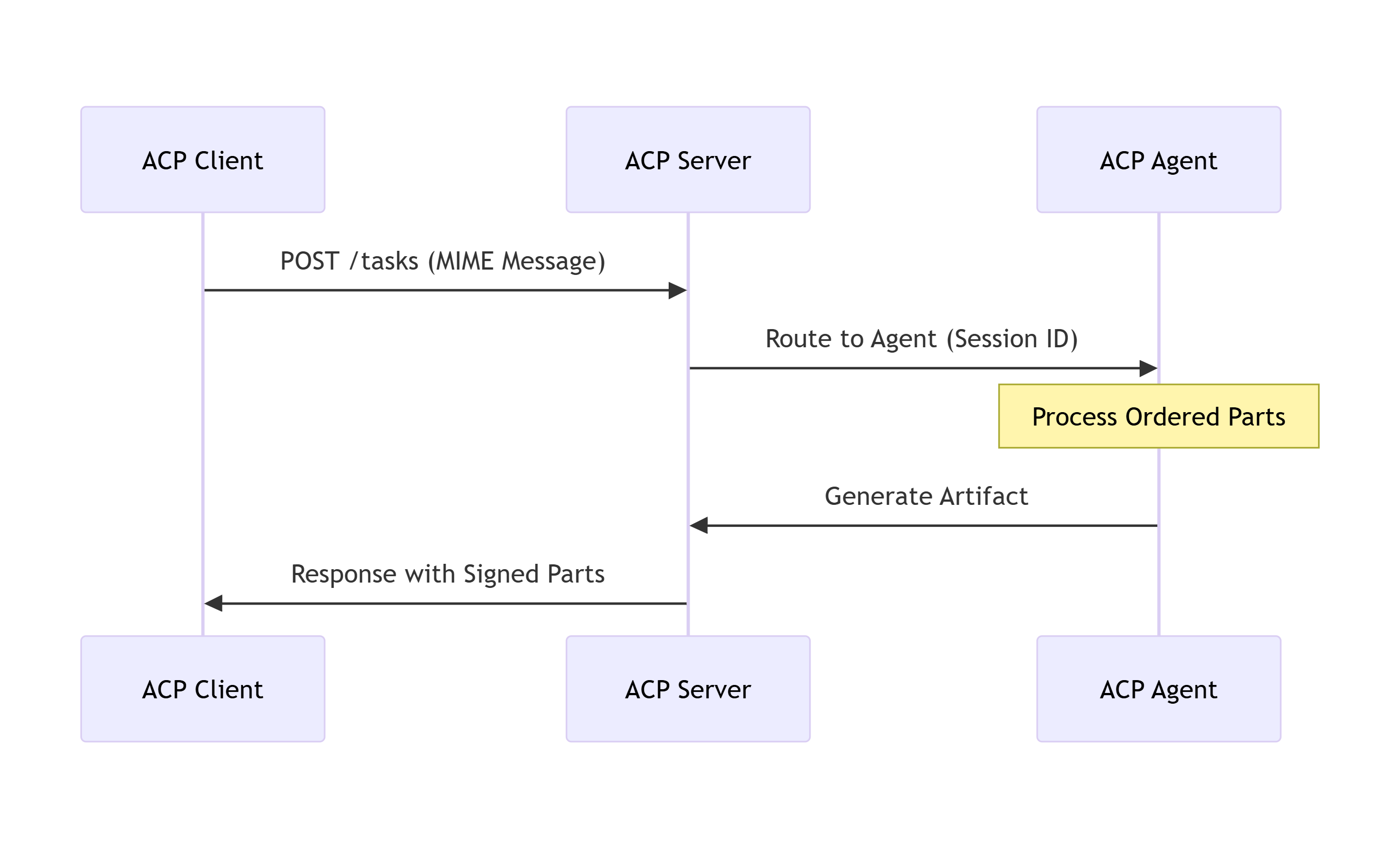
- ACP (Agent Communication Protocol): A Linux Foundation standard for RESTful, multimodal agent communication with optional message signing and mTLS. "The Agent Communication Protocol (ACP) is a lightweight, RESTful standard developed under the Linux Foundation to promote interoperability among AI agents."
- Agent Coraliser: A CORAL adapter that integrates legacy systems into the CORAL ecosystem. "the Agent Coraliser for legacy systems"
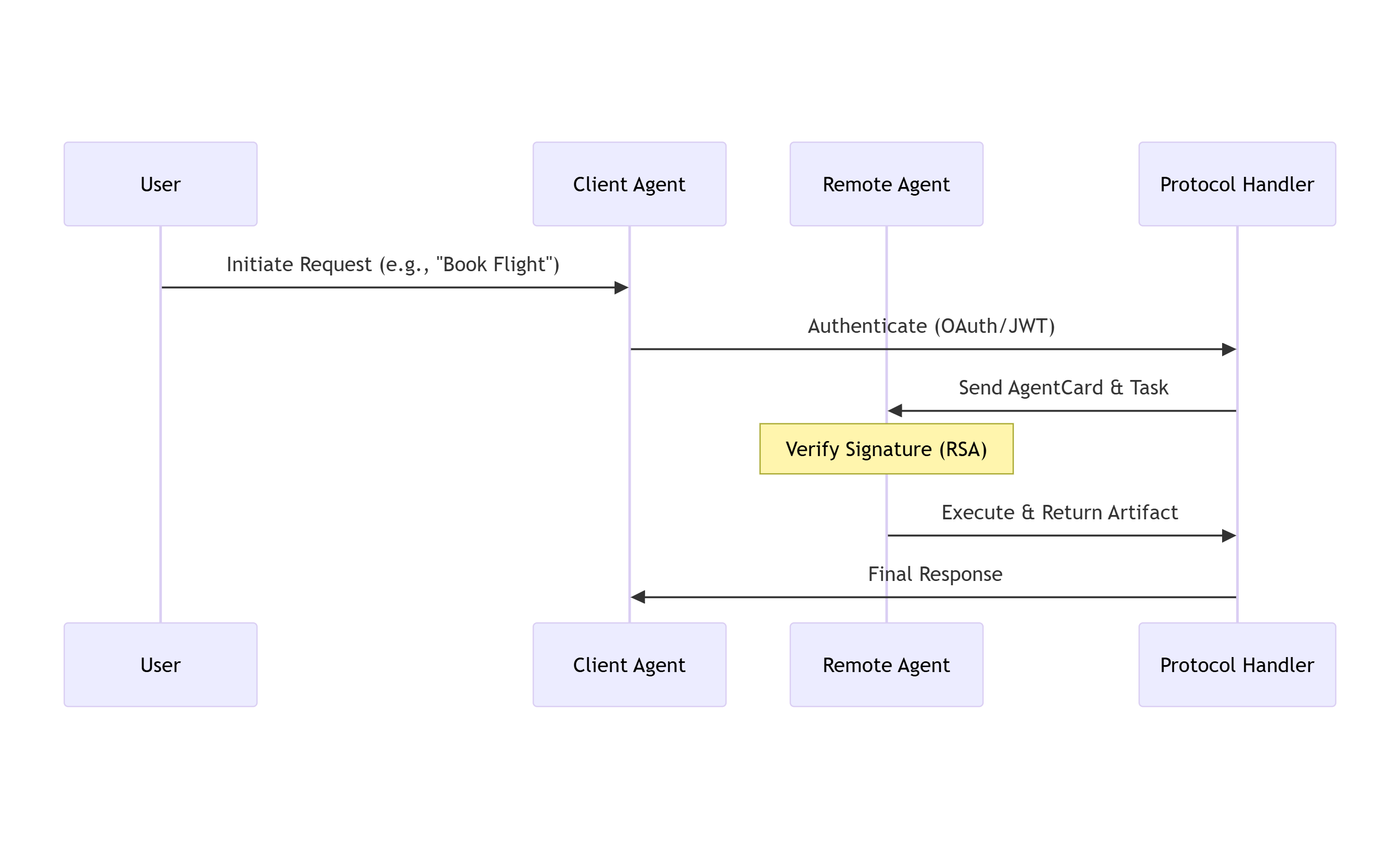
- AgentCard: A machine-readable metadata artifact describing an agent’s identity and capabilities for discovery and delegation. "At the core of A2A is the AgentCard, a machine-readable metadata artifact describing an agent's capabilities, roles, and identities."
- Bearer tokens: Access tokens that confer authorization based solely on their possession and presentation. "using bearer tokens and short-lived JWTs for identity propagation."
- Blockchain-based wallets: Cryptographic key containers tied to a blockchain, used for identity, signing, and transactions. "Authentication and identity are anchored in decentralized identifiers (DIDs) and blockchain-based wallets, which also manage cryptographic keys and transaction signing."
- Brokered client-server model: An architecture where agents communicate via intermediary servers rather than directly peer-to-peer. "ACP adopts a brokered client-server model, with stateless servers designed for Kubernetes-based scalability."
- Capability-based delegation: A delegation model granting narrowly scoped capabilities for specific actions. "capability-based delegation, allowing dynamic tool invocation without tight coupling."
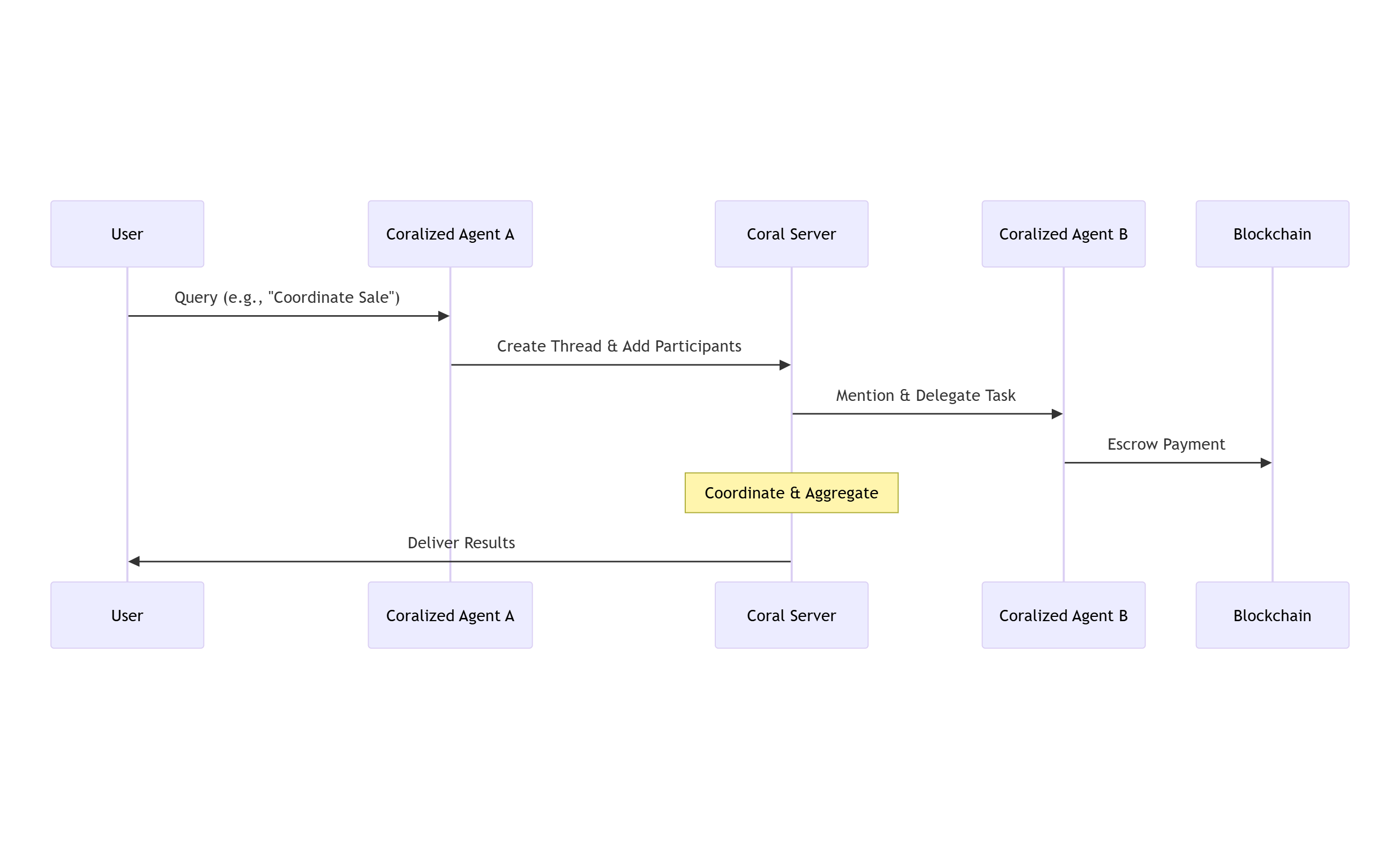
- CORAL: A decentralized agent collaboration protocol integrating threaded messaging with blockchain-based incentives and identity. "The CORAL protocol represents a decentralized infrastructure for AI agent collaboration, emphasizing threaded communication, trust establishment, and economic incentives to foster an ``Internet of Agents.''"
- Coralization: The process and tooling that integrate external agents and systems into CORAL via adapters. "Coralization enables external agents, models, and data sources to integrate through modular adapters such as the MCP Coraliser for APIs and the Agent Coraliser for legacy systems"
- CVE-2025-1198: A publicly cataloged vulnerability referencing token misuse and session hijacking. "CVE-2025-1198 \cite{cve2025-1198}, which documents token misuse and session hijacking."
- CWE-1220: A weakness category for insufficient granularity of access control. "This vulnerability corresponds to CWE-1220 (Insufficient Granularity of Access Control)"
- CWE-200: A weakness category for exposure of sensitive information. "consistent with CWE-200 (Exposure of Sensitive Information)"
- CWE-284: A weakness category for improper access control. "This issue aligns with CWE-284 (Improper Access Control)"
- CWE-290: A weakness category for authentication bypass by spoofing. "This vulnerability is classified under CWE-290 (Authentication Bypass by Spoofing)"
- CWE-306: A weakness category for missing authentication for critical function. "This issue is categorized under CWE-306 (Missing Authentication for Critical Function)"
- CWE-614: A weakness category for sensitive cookies in HTTPS sessions without secure attributes. "codified as CWE-614 (Sensitive Cookie in HTTPS Session Without Secure Attribute)"
- CWE-667: A weakness category for improper locking (e.g., race conditions). "aligns with vulnerability classifications such as CWE-667 (Improper Locking)"
- Data exfiltration: Unauthorized extraction or leakage of sensitive data from a system. "leading to predictable integrity failures and data exfiltration in non-strict configurations."
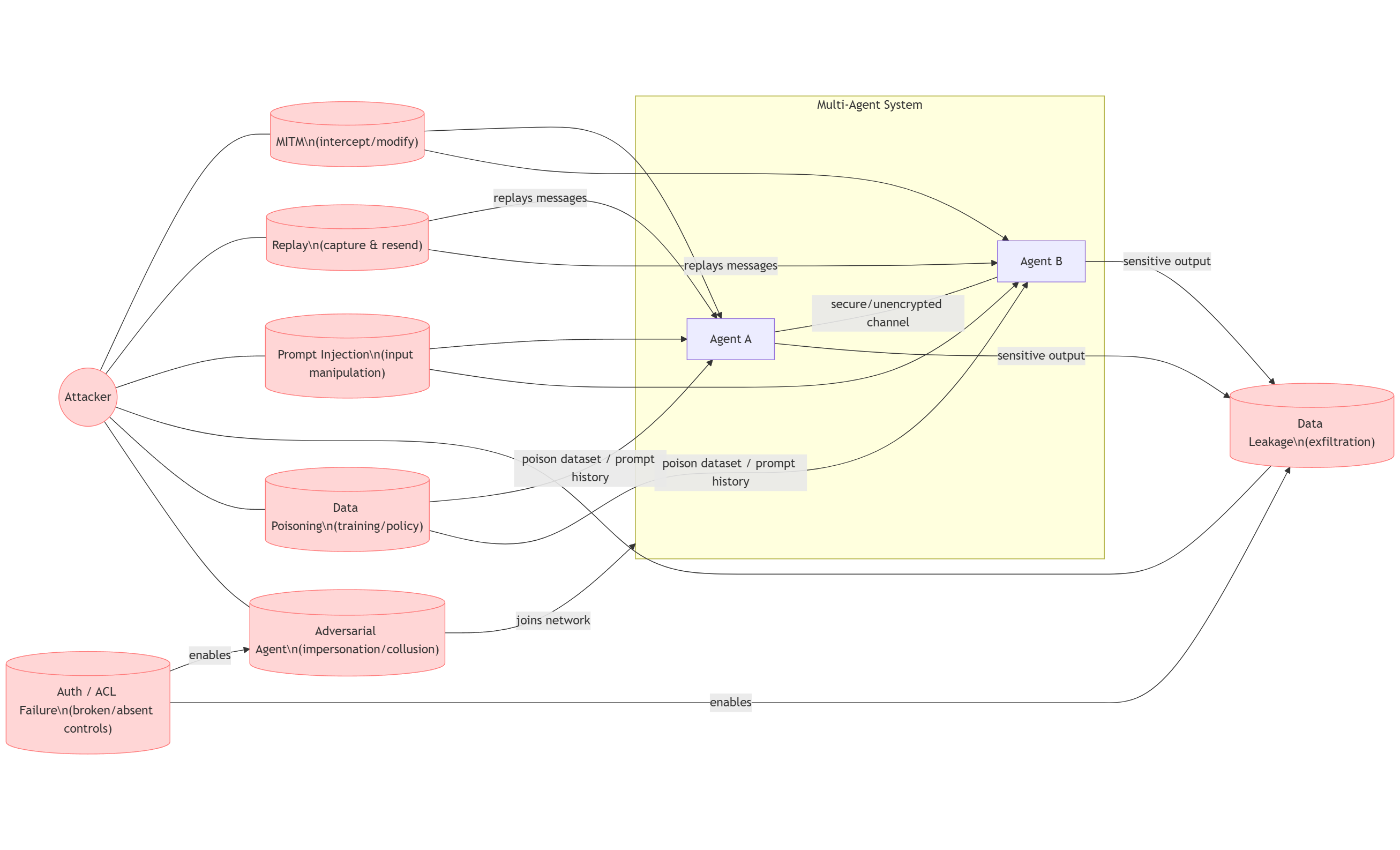
- Data poisoning: Malicious contamination of training or contextual data to manipulate model behavior. "Data Poisoning: Malicious actors can inject corrupted training or contextual data, influencing downstream models to behave incorrectly or embed hidden triggers."
- Decentralized identifiers (DIDs): Cryptographically verifiable identifiers not dependent on centralized registries. "Authentication and identity are anchored in decentralized identifiers (DIDs)"
- ECDSA: An elliptic-curve digital signature algorithm used to ensure message integrity. "with ECDSA signatures ensuring message integrity."
- End-to-end encryption: Encryption that protects data from sender to recipient, preventing intermediaries from reading it. "All communications employ end-to-end encryption across HTTP and WebSocket transports"
- Escrow-based microtransactions: Small automated payments held in escrow until conditions are met. "escrow-based microtransactions implemented on the Solana blockchain to facilitate trustless cooperation."
- JSON-RPC: A stateless remote procedure call protocol encoded in JSON. "JSON-RPC for request-response exchanges."
- JSON Web Signature (JWS): A JSON-based standard for message integrity via digital signatures. "JSON Web Signatures (JWS) on message parts."
- JSON Web Token (JWT): A compact, signed token format carrying claims for identity and authorization. "using bearer tokens and short-lived JWTs for identity propagation."
- Kubernetes: A platform for automating deployment, scaling, and management of containerized applications. "stateless servers designed for Kubernetes-based scalability."
- Man-in-the-Middle (MITM): An attack where an adversary intercepts or alters communications between parties. "Man-in-the-Middle (MITM): Intercepting or modifying agent communication allows attackers to compromise message integrity or confidentiality"
- MARL (multi-agent reinforcement learning): A field studying learning and coordination among multiple agents with potentially adversarial goals. "multi-agent reinforcement learning (MARL) studies reveal that malicious participants can collude to subvert cooperation or distort shared policies."
- MCP (Model Context Protocol): A protocol for maintaining and sharing contextual state with LLMs and tools. "Integration with the Model Context Protocol (MCP) supports contextual continuity with LLMs"
- MCP Coraliser: A CORAL adapter that integrates APIs into CORAL’s ecosystem. "the MCP Coraliser for APIs"
- MIME-typed multipart messages: HTTP message format carrying multiple parts, each with its own MIME type. "ACP employs MIME-typed multipart messages for structured data exchange"
- mTLS (mutual TLS): A TLS setup where both client and server authenticate each other with certificates. "optional mutual TLS (mTLS)"
- Nonce: A number used once to prevent replay attacks and ensure message freshness. "nonce mechanisms in its Model Context Protocol (MCP) implementation."
- OAuth 2.0: An authorization framework enabling token-based delegated access. "Standard security frameworks such as OAuth 2.0 and TLS, while foundational, do not provide sufficient granularity"
- Off-chain: Operations performed outside the blockchain ledger. "off-chain communication."
- On-chain: Operations executed and recorded directly on a blockchain ledger. "on-chain smart contracts for payments"
- OWASP A01:2021: The OWASP Top 10 category highlighting broken access control risks. "consistent with OWASP A01:2021."
- Prompt Injection: Attacks that insert malicious instructions into prompts or messages to subvert agent behavior. "Prompt Injection: An adversary may inject malicious instructions into prompts or message payloads"
- Provenance tracking: Mechanisms that record the origin and history of data or actions for auditability. "embedding provenance tracking, cryptographic signatures, and policy-based filtering"
- RBAC (Role-Based Access Control): An access control model restricting actions based on assigned roles. "role-based access control (RBAC) restricts permissions to defined agent roles."
- Replay Attacks: Reuse of previously valid messages to illicitly repeat actions or alter state. "Replay Attacks: Attackers may capture, delay, or replay previously valid messages"
- RSA key pairs: Asymmetric cryptographic keys used for signing and verification. "Cryptographic signatures using RSA key pairs ensure message integrity"
- Server-Sent Events (SSE): A one-way streaming mechanism over HTTP for real-time updates. "Server-Sent Events (SSE) for asynchronous updates"
- Smart contracts: Self-executing code on a blockchain that enforces agreements. "on-chain smart contracts for payments"
- Solana blockchain: A high-throughput blockchain used for CORAL’s on-chain components. "on the Solana blockchain"
- SSE gateway: A gateway endpoint that serves or mediates SSE streams. "authorization failures at its SSE gateway."
- Stateless servers: Servers that do not store session state between requests, aiding scalability. "stateless servers designed for Kubernetes-based scalability."
- TLS 1.3: The latest version of the Transport Layer Security protocol for encrypted transport. "All communications are encrypted using TLS~1.3"
- Transport-layer message validation: Security checks at the transport layer to verify message integrity and structure. "particularly in its transport-layer message validation and session isolation"
- WebSocket: A full-duplex, persistent communication protocol over a single TCP connection. "WebSocket transports"
- Zero-knowledge proof (ZKP): A cryptographic method to prove a statement without revealing the underlying information. "zero-knowledge proof (ZKP) techniques"
Practical Applications
Immediate Applications
The following applications can be deployed now by leveraging the paper’s vulnerability taxonomy, empirical findings, and configuration guidance. Each bullet notes sectors and key dependencies.
- Industry security audit toolkit based on the 14‑point vulnerability taxonomy
- Sectors: software platforms, healthcare, finance, logistics/supply chain
- What: Create a CI/CD “Agent Protocol Linter” and a GitHub Action that flags issues (e.g., token lifetimes, missing JWS, coarse scopes, missing consent, replay risk). Bundle with threat-model templates and runbooks.
- Dependencies: Access to configuration/code/logs; organizational buy‑in for remediation.
- ACP protocol hardening: make per‑message integrity mandatory
- Sectors: software, education, public sector
- What: Enforce JSON Web Signatures (JWS) on all message parts and require mTLS for ACP deployments via a drop‑in library (e.g., “ACP Secure Adapter” for Python/TypeScript SDKs) and ready‑to‑use configuration templates.
- Dependencies: Control over server/client configs; certificate management; performance budget for signature verification.
- CORAL SSE gateway remediation and off‑chain access control fixes
- Sectors: marketplaces, B2B automation, agent networks
- What: Patch or front the SSE gateway with a reverse proxy (“CORAL Gateway Guard”) that enforces authentication, per‑thread membership checks, fine‑grained scopes, and MFA for off‑chain sensitive actions.
- Dependencies: Deployment access; DID/wallet integrations; alignment with CORAL server updates.
- Token lifetime and rotation policy enforcement across protocols
- Sectors: finance, e‑commerce, telecom, energy
- What: Implement short‑lived JWT/OAuth tokens (minutes), nonces/timestamps, rotation, and revocation (OAuth introspection + cache invalidation). Offer a “Token Rotation Service” microservice for agent platforms.
- Dependencies: Identity provider support; distributed cache control; developer training.
- Replay and version drift monitoring pack
- Sectors: all MAS deployments
- What: SIEM content to detect replay (nonce reuse, timestamp skew), privilege persistence (stale scopes), and MITM (signature mismatch). Include dashboards and alert rules (“Agent Protocol SIEM Pack”).
- Dependencies: Telemetry hooks in agent runtimes; clock synchronization; log retention.
- Consent and transparency enhancements for agent workflows
- Sectors: healthcare, education, government services
- What: Add per‑artifact consent prompts in multipart MIME exchanges, ledger‑backed consent receipts (in CORAL on‑chain), and manifest‑level visibility for ACP (“Consent Receipt Plugin” for MCP/ACP).
- Dependencies: UI changes; schema updates; privacy/legal review.
- Least‑privilege scope design and ABAC/RBAC policy templates
- Sectors: supply chain, travel, finance
- What: Provide ready‑made fine‑grained scope manifests (e.g., read:calendar:availability), ABAC policies (OPA/Rego), and ACP task‑level JWT exemplars.
- Dependencies: Policy engine deployment; coordination with service owners.
- Red‑teaming lab and academic curriculum
- Sectors: academia, enterprise training
- What: Laboratories simulating prompt injection, leakage, replay, and spoofed discovery using the taxonomy; course modules and practical assignments.
- Dependencies: Sandboxed testbed; curated datasets; faculty/mentor support.
- Procurement and compliance checklists for MAS vendors
- Sectors: public sector, large enterprises
- What: RFP addenda mandating per‑message signatures, SCA/MFA for high‑risk actions, granular scopes, consent receipts, and revocation SLAs; internal audit templates aligned to the taxonomy.
- Dependencies: Policy alignment; vendor cooperation.
- Personal AI assistant safety settings
- Sectors: consumer/daily life
- What: App‑level controls to restrict agent scopes, enable explicit consent prompts for data sharing, and display token expiry status; simple “privacy mode” profiles for non‑technical users.
- Dependencies: App developer support; UX updates; mobile OS permissions.
Long-Term Applications
The following applications require further research, development, scaling, or standardization. They build on the paper’s proposed hybrid approach and identified systemic gaps.
- Hybrid protocol standard combining CORAL’s architecture with ACP’s mandatory per‑message integrity
- Sectors: cross‑industry
- What: A standardized “Hybrid Agent Protocol (HAP)” that integrates CORAL’s threaded/session isolation and on‑chain consent/payments with ACP’s JWS‑by‑default and mTLS. Includes reference SDKs and conformance tests.
- Dependencies: Multi‑vendor consortium; performance benchmarking; IETF/LF or ISO standardization efforts.
- Formal verification of agent communication protocols
- Sectors: academia, high‑assurance industries (aerospace, medical devices)
- What: TLA+/Coq models and proofs for authentication, revocation, replay protection, and per‑message integrity; verified implementations and property‑based testing harnesses.
- Dependencies: Tooling expertise; protocol formal models; funding.
- Decentralized identity and consent at scale with privacy‑preserving proofs
- Sectors: healthcare, finance, government
- What: DID‑based identity with ledger‑backed consent receipts and zero‑knowledge proofs for sensitive operations (SCA without revealing secrets).
- Dependencies: Blockchain infrastructure; ZKP libraries; regulatory acceptance.
- Secure discovery registries resilient to spoofing
- Sectors: software ecosystems, public registries
- What: PKI‑backed AgentCard signing, registry notarization, and provenance tracking; a “Trusted Agent Registry” with automated verification and revocation broadcasting.
- Dependencies: PKI governance; cross‑provider trust anchors; operating budgets.
- Confidential computing for session isolation
- Sectors: finance, healthcare, defense
- What: Deploy TEEs (e.g., SGX/TDX/SEV) to isolate agent sessions, key material, and message validation logic; attestation integrated into protocol handshakes.
- Dependencies: Hardware/Cloud TEE support; attestation services; performance overhead.
- Adaptive ABAC with dynamic, context‑aware scopes
- Sectors: enterprise automation
- What: Policy engines that adjust scopes in real time based on risk level, task context, and agent reputation; “Scope Orchestrator” integrating OPA/Rego and protocol manifests.
- Dependencies: Telemetry streams; ML‑based risk scoring; policy lifecycle tooling.
- Signed streaming transport standards
- Sectors: software, media, IoT
- What: Message‑level signing for SSE/WebSocket streams with replay prevention, session binding, and per‑chunk integrity; “Signed Streaming Transport” spec and libraries.
- Dependencies: Standards process; SDK adoption; backward compatibility plans.
- Automated multi‑agent attack simulation platform
- Sectors: cybersecurity, research
- What: “Agent Red Team Simulator” to generate adversarial scenarios (prompt injection, poisoning, MITM, drift) and measure protocol resilience under load and collaboration graphs.
- Dependencies: Scalable testbeds; data generation; metric suites.
- MAS‑Sec certification and regulatory frameworks
- Sectors: policy, compliance
- What: A certification program with levels (e.g., Bronze/Silver/Gold) aligned to the 14‑point taxonomy; regulatory guidance for consent, scope minimization, revocation SLAs, and auditability.
- Dependencies: Standards bodies; regulator engagement; auditor ecosystem.
- Protocol‑level prompt‑injection mitigation and content provenance
- Sectors: content platforms, education, healthcare
- What: Provenance‑signed message envelopes (“PromptGuard Envelope”) with policy filters that block tainted instructions and enforce quarantine flows across agent chains.
- Dependencies: LLM safety tooling; signature infrastructure; cross‑protocol schema support.
- Agent key management via hardware wallets and secure elements
- Sectors: robotics, industrial IoT, finance
- What: Hardware‑backed key custody for agents (FIDO/HSM/secure elements) with DID integrations and audited rotations.
- Dependencies: Device supply chain; SDK integration; operational procedures.
- Cross‑provider revocation and state consistency network
- Sectors: cloud providers, large enterprises
- What: A “Universal Revocation List” and heartbeat protocol to eliminate privilege persistence and version drift across registries and peers; CRL/OCSP‑like services for MAS.
- Dependencies: Inter‑provider agreements; distributed consensus; reliability engineering.
- Energy‑aware and latency‑optimized secure messaging
- Sectors: energy, edge/5G, smart cities
- What: Protocol profiles that balance per‑message signing, encryption, and computation cost for constrained devices while preserving integrity and confidentiality.
- Dependencies: Edge runtimes; adaptive QoS; device telemetry.
Notes on assumptions and dependencies across applications:
- Many immediate fixes assume control over configuration (e.g., ACP servers, CORAL gateways) and access to telemetry.
- Blockchain integrations (as in CORAL) depend on reliable on‑chain infrastructure and key management hygiene.
- Mandatory per‑message signing and mTLS introduce compute and latency overhead; performance tuning is required.
- Consent UX changes require product and legal alignment; per‑artifact prompts may need careful design to avoid user fatigue.
- Cross‑provider trust, revocation, and registry hardening require governance and standards participation.
Collections
Sign up for free to add this paper to one or more collections.