- The paper demonstrates that liquidity exhaustion attacks can severely disrupt intent-based cross-chain bridges, analyzing over 3.5 million intents worth $9.24B.
- It employs empirical analysis and simulation frameworks to quantify attack profitability and protocol vulnerabilities under varying liquidity conditions.
- The study outlines practical defense mechanisms such as liquidity-aware rate limiting, accelerated refunds, and automated solver rebalancing to mitigate these risks.
Liquidity Exhaustion Attacks in Intent-Based Cross-Chain Bridges
Introduction
The analyzed paper, "Exploiting Liquidity Exhaustion Attacks in Intent-Based Cross-Chain Bridges" (2602.17805), presents an extensive empirical and simulation-based investigation into the security and economic risks introduced by intent-based bridging protocols. By analyzing more than 3.5 million cross-chain intents accounting for over 9.24B in volume, the authors provide a rigorous study of liquidity exhaustion as a new class of attack threatening protocol liveness and economic integrity in recent cross-chain architectures.
Intent-based cross-chain bridges—such as Across, Mayan Swift, and deBridge—delegate execution of cross-chain transfers to off-chain actors, or solvers, who front their own liquidity and settle later. While this paradigm enhances UX and reduces latency compared to traditional bridging, it creates a new surface for attacks. The attack vector centers on solver liquidity as a bottleneck, with systemic risk arising from liquidity concentration, delayed settlement, and reactive operational management.
Architecture of Intent-Based Cross-Chain Bridges
These protocols allow users to submit high-level intents describing end-states, e.g., atomic swaps between chains. Solvers bid in auctions to fulfill these intents by directly transferring funds to users on the target chain and subsequently recouping liquidity after settlement verification.
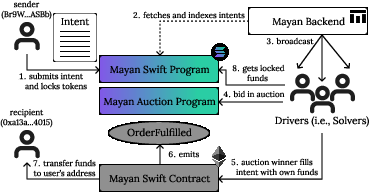
Traditional bridges rely on lock-mint/unlock schemes, and only release assets after cross-chain verification. In contrast, intent-based systems invert the order: solvers first take risk and settle later, largely reducing perceived user latency (Figure 1).
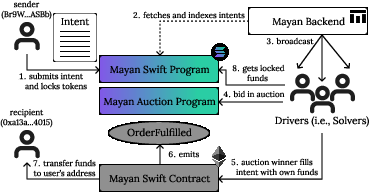
Figure 1: Cross-chain transaction flow from Solana to Ethereum using Mayan Swift's bridge (a Wormhole bridge).
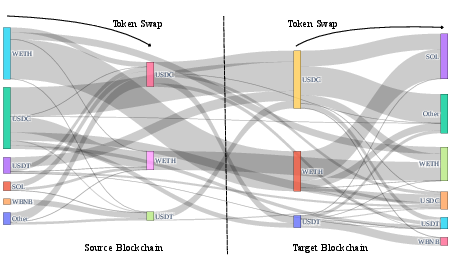
Liquidity management is further streamlined by requiring solvers to predominantly hold a subset of high-liquidity tokens, performing swaps only as needed to handle user-specific asset requests (Figure 2).
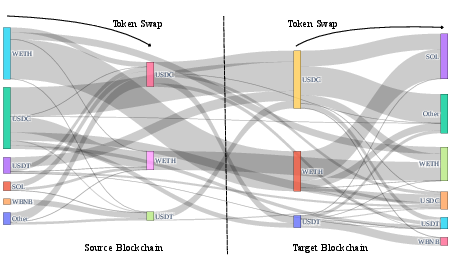
Figure 2: Solvers convert low-liquidity tokens to a high-liquidity set (e.g., ETH, USDC, USDT) for efficient operations; optional user swaps are performed as required.
Liquidity Exhaustion Attack: Model and Mechanism
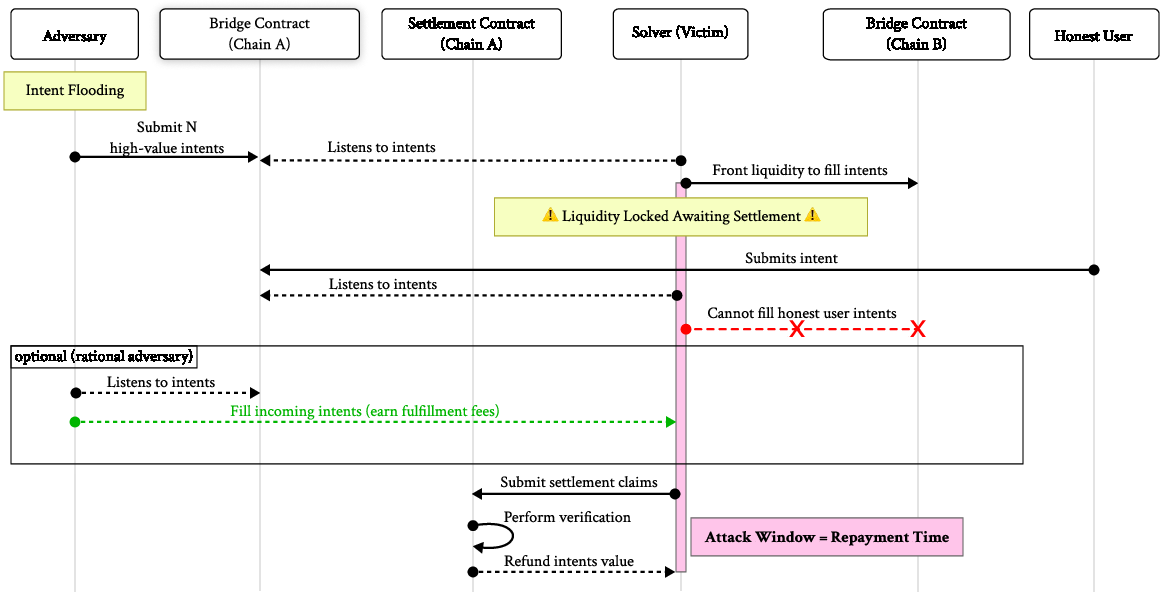
The core attack, termed liquidity exhaustion, leverages the inherent lag between intent fulfillment (solver sends funds to the user) and settlement (solver gets repaid). During this interval, a rational or byzantine adversary generates sequences of intents or probes liquidity dips to temporarily drain solver capital, preventing solvers from participating in subsequent auctions and degrading protocol availability (Figure 3).
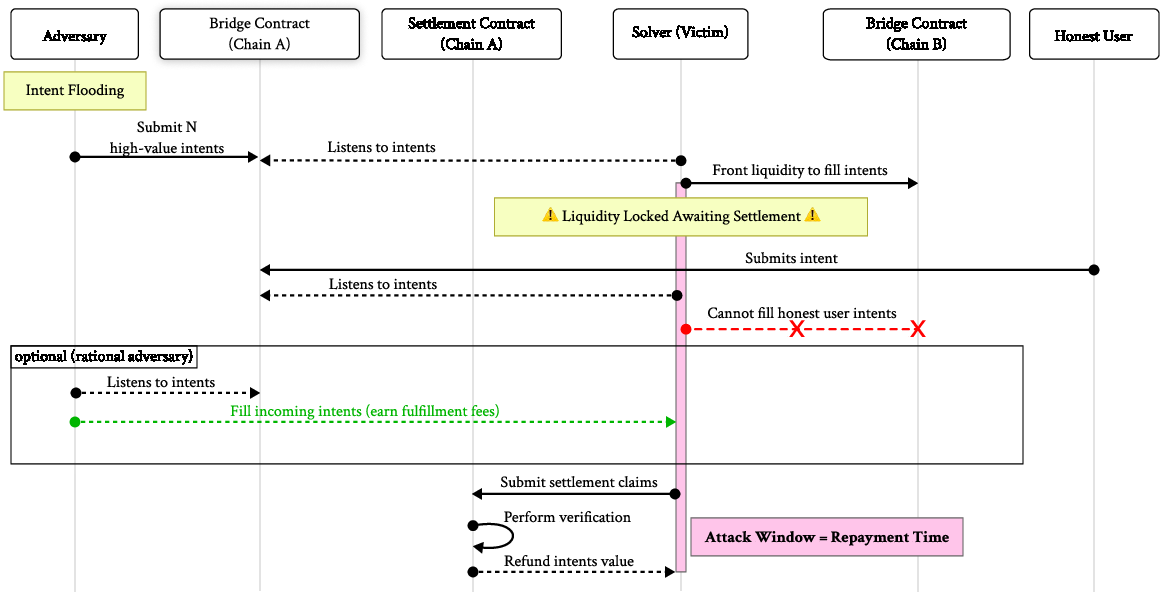
Figure 3: Sequence diagram of a liquidity exhaustion attack, involving an attacker flooding intents to deplete solvers’ available liquidity and induce denial-of-service.
Distinct adversarial models are considered:
- Rational Adversary: Exploits transient low-liquidity states for financial profit, fulfilling high-margin intents where attack costs are exceeded by solver revenue.
- Byzantine Adversary: Induces liveness failures or targeted disruption without regard to economic loss.
Net attacker profit is modeled as total received solver margins, minus the capital cost and transaction/auction fees associated with exhausting solver balances during attack windows.
Empirical Analysis: Protocol Properties and Vulnerabilities
The authors process a comprehensive on-chain dataset, reconstructing solver balances, intent auctions, protocol fees, and settlement latencies for Across, Mayan Swift, and deBridge. Key risk indicators emerge:
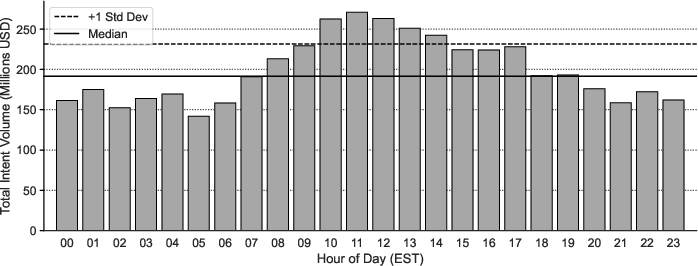
- Temporal Demand Clustering: Most value transacted occurs during predictable EST time windows, creating concentrated periods of liquidity demand (Figure 4).
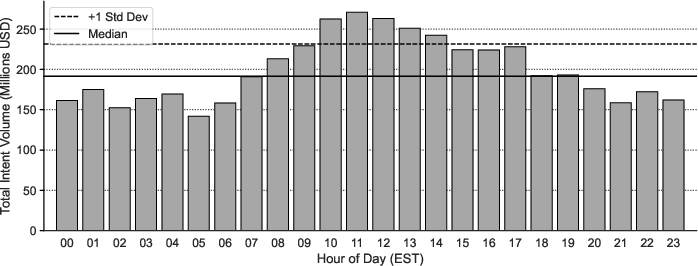
Figure 4: Hourly distribution of intent volume for deBridge, revealing strong temporal clustering of cross-chain activity.
- Centralization of Solver Market: High solver concentration, notably in deBridge, makes protocol availability highly sensitive to single-entity liquidity.
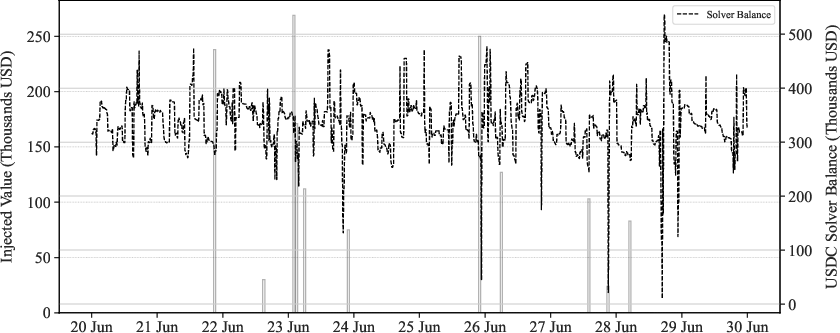
- Non-Automated Rebalancing: Liquidity injections are sporadic, not programmatically nor reliably triggered by low balances (Figure 5).
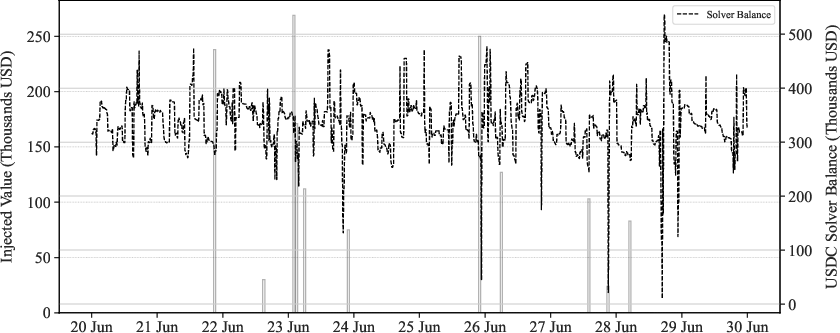
Figure 5: Liquidity injections and balance trends for Mayan Swift’s top solver indicate absence of automated or balance-responsive capital management.
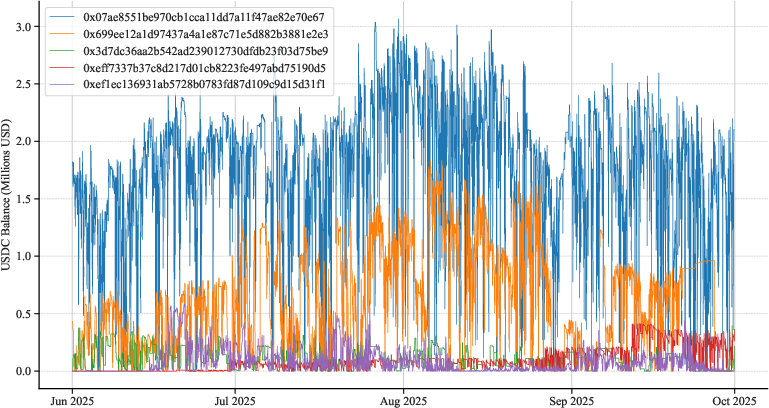
- Liquidity Volatility and Attack Windows: Solver balances are highly volatile, with recurring dips creating frequent, exploitably low-liquidity intervals (Figure 6).
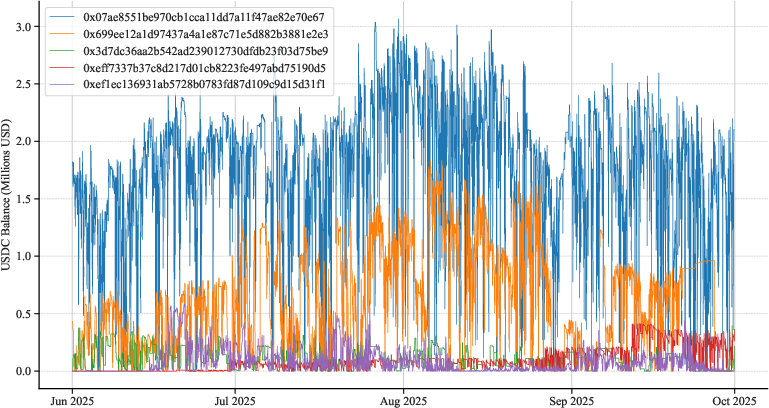
Figure 6: USDC balances for Across solvers demonstrate high volatility and depletion events, aligning with attack windows.
Simulation Framework and Attack Outcomes
A replay-based simulation framework is designed to inject synthetic attacks into historical traces, evaluating attack opportunity, profitability, and protocol impact under real-world timing and liquidity conditions.
Baseline Strategy
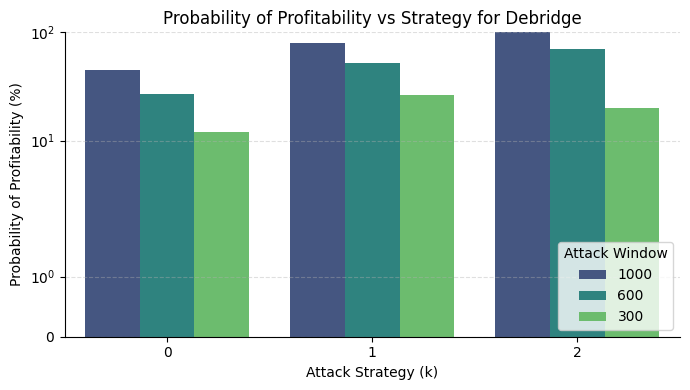
A simple “median-deviation” strategy identifies moments where liquidity falls below historical norms by k standard deviations, triggering attack windows. For each bridge and configuration, the simulation computes the net attacker profit, success probability, and number of failed user intents.
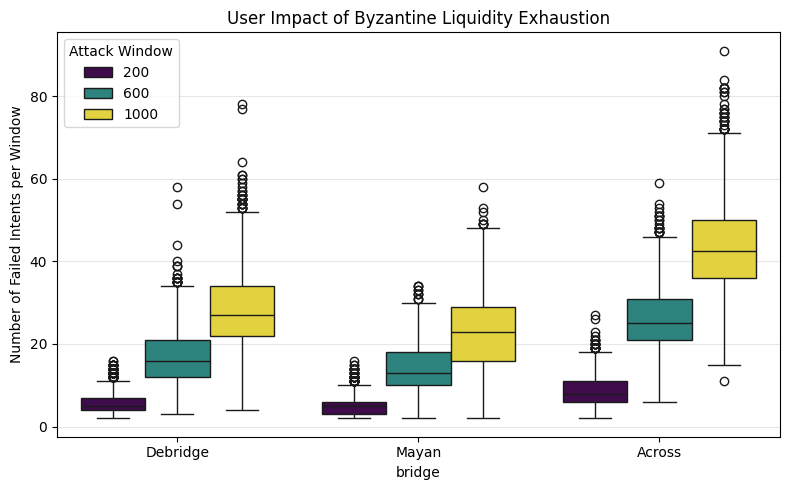
Byzantine Attacks and Availability Impact
Byzantine adversaries willing to incur economic cost can intermittently suppress protocol liveness, causing dozens of failed intents within 16-minute attack windows and opportunity losses for solvers (missed fees, profit) (Figure 8).
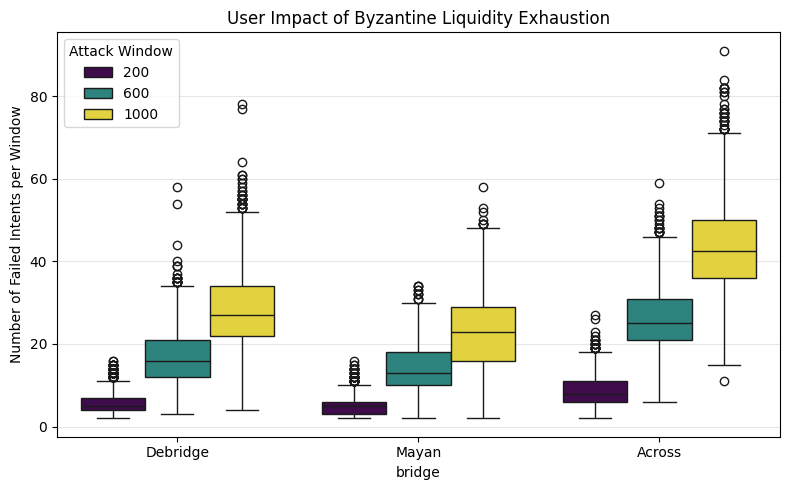
Figure 8: Number of user intents rejected by Across protocol during liquidity exhaustion windows, demonstrating direct service denial.
Optimized Targeted Attack Strategies
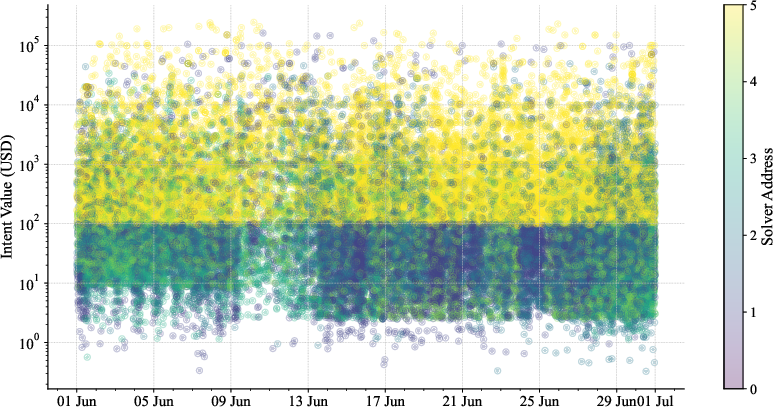
The baseline attack is significantly optimized by exploiting real-world auction dynamics: certain solvers participate only in specific value classes or tokens, so a targeted attacker can reduce the required liquidity drained by focusing on high-value/low-competition classes (Figure 9).
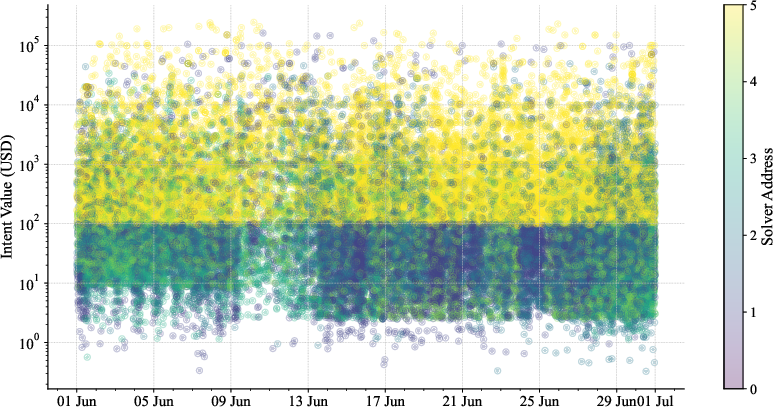
Figure 9: Scatter plot showing discrete auction participation among top Mayan Swift solvers; certain liquidity is only relevant for specific transaction classes.
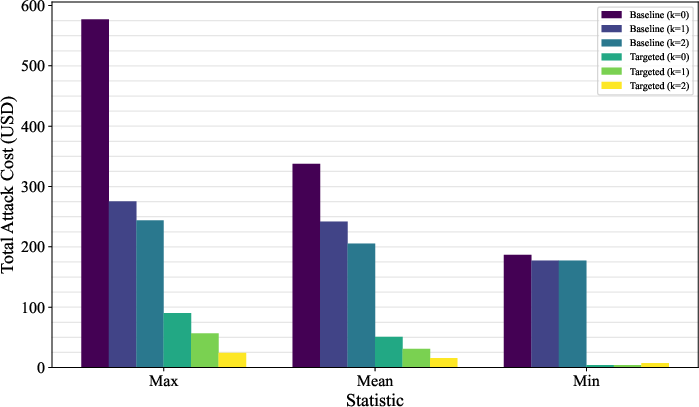
This approach reduces attack costs by up to 90%, shrinking the barrier for both rational and byzantine attackers (Figure 10).
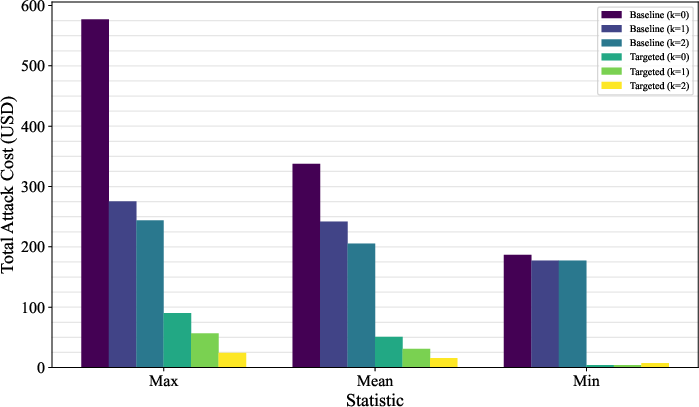
Figure 10: Attack costs for Mayan Swift, comparing baseline and targeted strategies; targeted exploitation yields order-of-magnitude cost reductions.
Nonetheless, practical attack profitability remains linked to value distribution and solver margins, highlighting the pivotal role of external traffic patterns.
Defense Mechanisms and Protocol-Level Implications
Multiple mitigations are discussed:
- Liquidity-Aware Rate Limiting: Throttle fulfillment based on real-time available liquidity.
- Accelerated/Conditional Refunds: Reduce settlement delay to narrow attack windows.
- Automated Solver Rebalancing: Programmatically inject liquidity upon depletion, decreasing mean attack window duration.
- Dynamic Fee Adjustment: Adjust protocol/solver fees dynamically in response to liquidity scarcity.
- Solver Diversity and Scale: Incentivize participation and centralization-resistant design to diffuse exploitation risk.
The trade-off space is nontrivial: reducing solver profits below break-even eliminates attack incentives, but may also make participation uncompetitive versus alternative yield opportunities.
Theoretical and Practical Implications
The research upends the expectation that economic safety in DeFi protocols can be achieved solely via algorithmic or smart contract design. Instead, security for intent-based cross-chain systems is shown to be highly contingent on exogenous factors: demand patterns, liquidity provisioning discipline, and the strategic conduct of both users and solvers. Notably, high solver profitability and market concentration emerge as primary risk drivers; mere technical soundness cannot close this exposure.
Future protocol evolution in the field must explicitly treat liquidity and capital management as first-class security parameters, with comprehensive monitoring, risk accounting, and possibly, adaptive circuit-breaker mechanisms. If these findings generalize, the work strongly motivates integration of liquidity-aware mechanisms into intents standardization efforts and bridging protocol economics.
Conclusion
The paper delivers a data-driven, mechanistic demonstration that liquidity exhaustion is a material and tractable threat to intent-based bridges. Empirical simulations and attack modeling reveal that under plausible parameterizations and market dynamics, sophisticated agents can induce liveness failures or extract profit at the expense of honest solvers and end-users. Critically, the attack surface emerges from operational and economic structure, not smart contract bugs, and can only be addressed through systemic changes in protocol design or incentive calibration. As intent-based models proliferate in cross-chain DeFi, explicit consideration of these liquidity exhaustion risks is necessary to sustain secure, reliable, and decentralized interoperability.