- The paper establishes a secure PAC learning framework using a classical-quantum hybrid sampling protocol rooted in the quantum no-broadcasting theorem.
- It derives explicit lower and upper bounds on sample complexity to ensure that only authorized learners can achieve effective learning amid adversarial threats.
- The protocol leverages minimal quantum resources, making it practical for NISQ devices while offering a robust alternative to fully classical approaches.
Introduction
The confluence of quantum information theory and computational learning theory has generated significant interest in recent years, particularly in the context of sample-efficient learning and security guarantees. The paper "Quantum secure learning with classical samples" (1912.10594) rigorously formulates and analyzes secure learning in the framework of PAC (Probably Approximately Correct) learning, exploiting quantum mechanical principles to establish security conditions unattainable in classical regimes. Central to the paper is a classical-quantum hybrid protocol that enables secure data sampling between two legitimate parties, ensuring that only authorized learners can perform successful learning while excluding adversaries, irrespective of their computational power or the learning algorithm employed.
Classical-Quantum Hybrid Secure Sampling Protocol
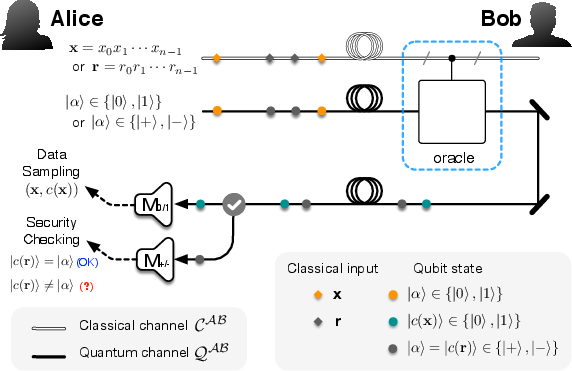
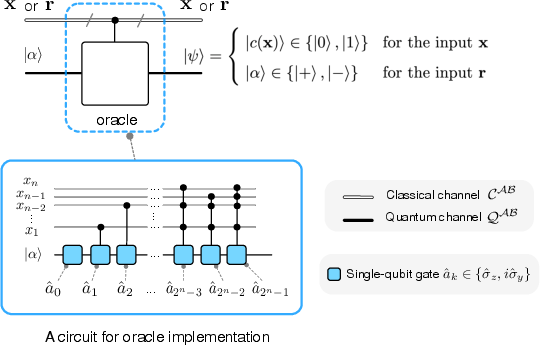
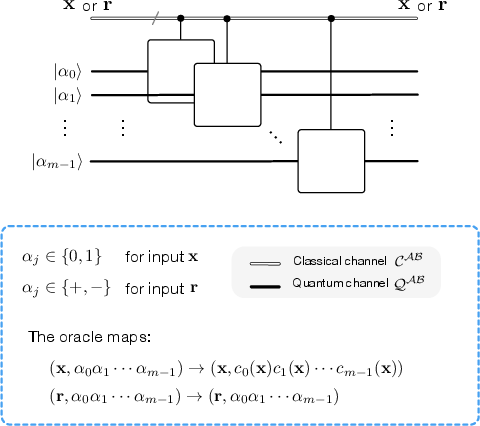
The authors introduce a hybrid protocol that utilizes a classical-quantum oracle for secure sample generation. Legitimate parties—traditionally named Alice (learner) and Bob (oracle holder)—operate over both classical and quantum communication channels. Alice randomly prepares either computational (∣0⟩, %%%%1%%%%) or Hadamard basis (∣+⟩, ∣−⟩) qubit states and pairs them with classical inputs. The oracle acts upon these inputs, and Alice measures the returned qubit to construct a dataset or detect adversarial interference.
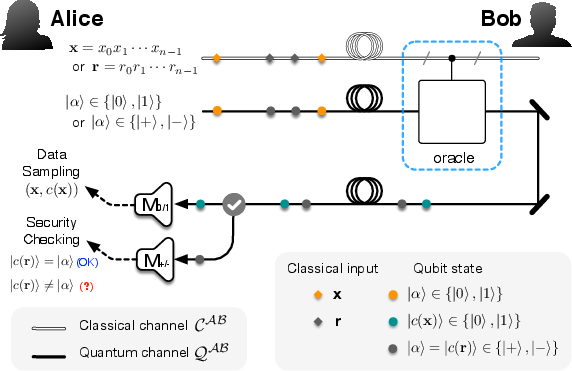
Figure 1: Schematic of the hybrid classical-quantum sampling protocol with distinct classical and quantum communication channels.
Security is grounded in the indistinguishability of basis choices by an eavesdropper (Eve) and the inherent quantum no-cloning/no-broadcasting theorem. Random basis choice facilitates direct detection of adversarial activity, analogous to BB84-type quantum key distribution protocols, but reinterpreted for secure sample generation in learning.
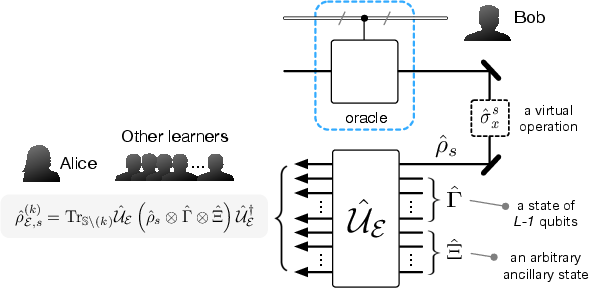
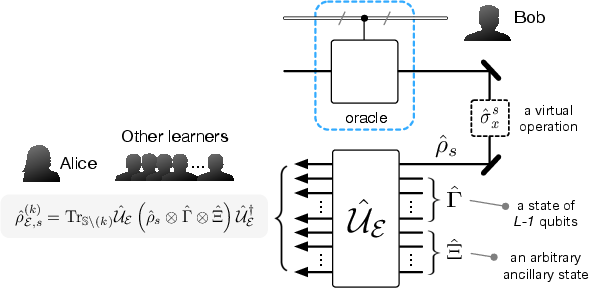
Figure 2: Illustration of general adversarial attack strategies on the classical-quantum sampling protocol.
Quantum No-Broadcasting and its Implications for Learning Security
A significant result is the rigorous demonstration that learning samples satisfying the PAC guarantee cannot be simultaneously shared among multiple learners due to the quantum no-broadcasting principle. Any attempt by an adversary to duplicate (broadcast) the qubit component of the oracle response will inevitably introduce detectable noise, quantifiable via fidelity metrics. The paper proves that, given the structure of the protocol and the no-broadcasting theorem, adversarial learners cannot obtain an uncorrupted sample set sufficient for PAC learning unless the legitimate learner fails.
This result leads to the following: for any function c from concept class C, the equality T=T(k) (where T denotes the legitimate dataset and T(k) the dataset available to the kth learner, including adversaries) can never be achieved in the presence of the quantum protocol. Therefore, successful PAC learning can be guaranteed exclusive to the legitimate learner.
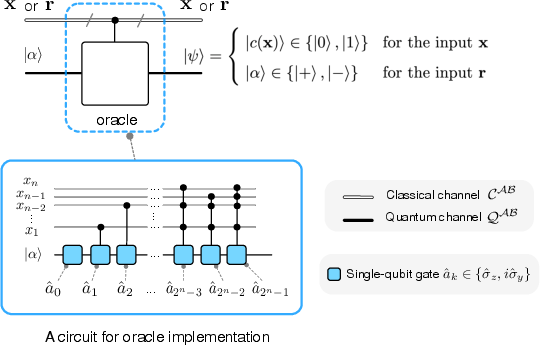
Figure 3: Architecture of the hybrid classical-quantum oracle enabling secure evaluation and sample generation.
Secure PAC Learning: Theory and Boundaries
Building upon the quantum-secured sampling framework, the authors formalize a quantum secure (ϵ,δ)-PAC learning condition. They derive explicit lower and upper bounds on sample complexity. The lower bound Mb(ϵ,δ) ensures the legitimate learner can PAC-learn despite contamination (error rate η), while the upper bound Mc(ϵ,δ) guarantees that adversaries cannot accumulate enough valid samples for successful PAC learning.
The bounds quantitatively depend solely on the sample size and corruption fraction, not the specifics of the learning algorithm or model. The threshold for adversarial effectiveness is determined by the optimal quantum cloning fidelity; for instance, for single-qubit responses, the critical contamination fraction is ηc=1−Fopt, with Fopt derived from the best-possible quantum cloner. Therefore, the resulting secure PAC condition is both necessary and sufficient under the quantum protocol, and fundamentally unachievable by any classical mechanism, where sample duplication cannot be restricted.
Extension to Multi-Class Learning
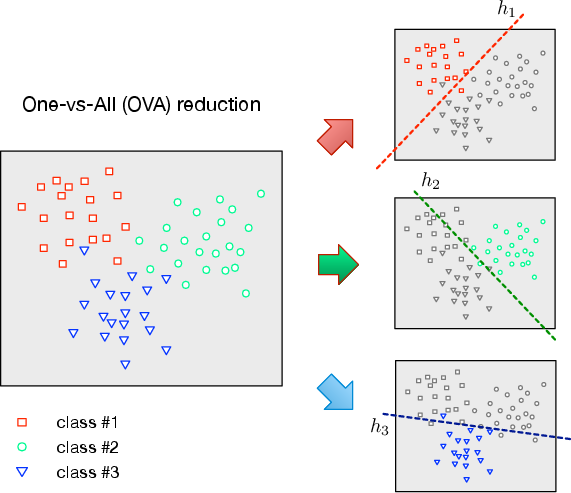
The authors analyze both ensemble and single-machine generalizations to the multi-class setting. Multi-class classification can be constructed by reducing to multiple secure binary classification problems (One-vs-All, OVA), or by extending the oracle to output multi-qubit labels, enabling parallel secure sample generation for all classes.
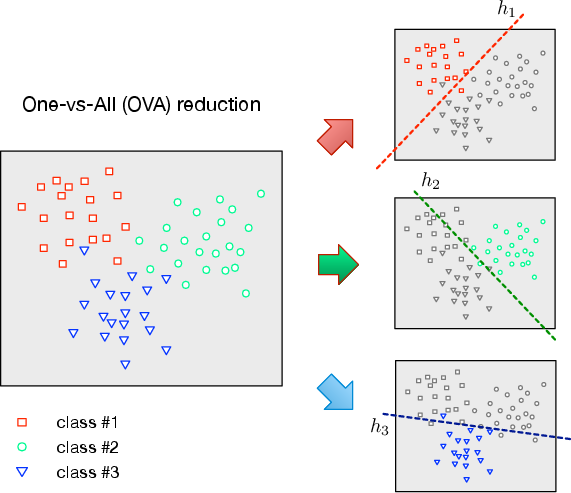
Figure 4: Schematic of the One-vs-All (OVA) reduction for secure multi-class learning using multiple binary classifiers.
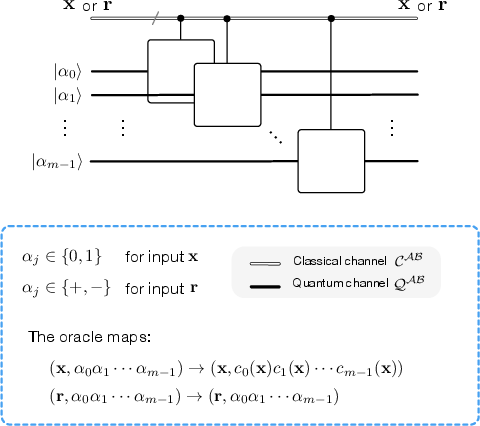
Figure 5: Oracle structure for direct multi-class secure learning employing multiple conditioned qubit channels.
In the single-machine approach, the no-broadcasting restriction becomes more stringent as the number of classes (qubits) increases, shrinking the permissible range Mc(ϵ,δ)−Mb(ϵ,δ) and, hence, the viable region for secure PAC learning. The OVA approach, while less restrictive, results in higher aggregate sample complexity due to the need to train each binary classifier independently under secure sampling.
Practicality and Implementation
A salient property of the protocol is its suitability for implementation on NISQ devices, since it neither requires global quantum superposition over the dataset nor the use of quantum RAM. The architecture features a minimal quantum resource footprint—a single qubit per oracle call—while leveraging quantum security guarantees for classical data. This synergistic classical-quantum approach is markedly distinct from proposals that require fully coherent quantum access to large-scale classical data.
Conclusions
The paper establishes both a theoretical framework and practical protocol for information-theoretically secure learning based on quantum mechanical principles. Security is rooted in the no-broadcasting theorem, which constrains both sample distribution and adversarial PAC learning. The result is a formal, algorithm-independent link between quantum information and learning theory, with implications for the design of secure, sample-efficient machine learning systems in the presence of adversaries. Future work includes refining the tightness of the upper sample complexity bound Mc(ϵ,δ) and extending the analysis to noisy or more general quantum oracles.