- The paper introduces PULSAR-Net, which leverages full-waveform and simultaneous sensing to reconstruct LiDAR point clouds under severe jamming.
- It demonstrates significant recovery improvements with point-level rates exceeding 82% and object detection mAP close to benign conditions.
- The work validates its methodology through both synthetic and real-world experiments, setting a new baseline for LiDAR jamming defense.
Introduction and Motivation
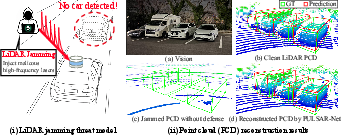
LiDAR remains a linchpin of autonomous vehicle perception, yet its active sensing principle exposes a critical security vulnerability: high-frequency laser jamming attacks can fully randomize or "blind" the derived point cloud, leaving AVs unable to perceive obstacles and resulting in catastrophic failures. The prevailing view in the literature has been that defense is infeasible since post-processing of randomized point clouds cannot recover lost geometric information. This work overturns that assumption by shifting focus from the point cloud output to the often-discarded intermediate full-waveform representation and leveraging simultaneous laser sensing—a common feature in modern multi-channel LiDARs—as an information source for defense.
The authors introduce PULSAR-Net, a neural architecture for reconstructing authentic point clouds from full-waveform data in the presence of severe jamming. Their design leverages distinguishing waveform/temporal signatures of legitimate versus malicious signals, as well as the spatial correlation introduced by simultaneous laser firing. The approach is validated on synthetic attacks (derived from KITTI and nuScenes) and in collaboration with LiDAR manufacturers on real-world hardware, showing robust recovery that exceeds previous baselines both in point-level recovery rate and object detection mAP.
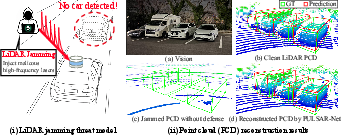
Figure 1: PULSAR-Net reconstructs faithful point clouds from LiDAR data corrupted by jamming, leveraging intermediate full-waveform information and simultaneous sensing measurements.
Threat Model and Foundations
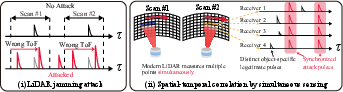
Jamming attacks inject rapid high-power laser pulses at the operating wavelength/frequency of the target LiDAR. Recent HFR (High-Frequency Repeat) attacks achieve total point cloud randomization, as multiple false returns overwhelm legitimate object reflections. Existing countermeasures (e.g., pulse randomization or fingerprinting) are ineffective against this vector since the attack is perfectly synchronized with the victim sensor. Direct point cloud denoising (e.g., spatial filtering, outlier removal) also fails as all spatial context is destroyed.
The key physical insight enabling defense is that while attack-induced randomness dominates the point cloud, the raw waveform (i.e., time-resolved return intensity) contains the superposition of attack and legitimate returns, with temporal and intensity features distinguishing real (weaker, variable, geometry-dependent) from attack (strong, consistent, cross-channel-synchronous) pulses.
Simultaneous laser sensing, implemented in modern mechanical and solid-state LiDARs, means multiple return channels are sampled at the same instant with the same attack pulse, introducing cross-channel waveform similarities for attack signals but not for legitimate object returns. This unique spatial-temporal structure is the basis for robust learning-based attack pulse suppression.
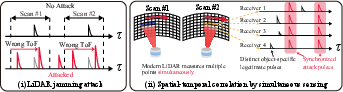
Figure 2: LiDAR jamming attacks inject spatially and temporally correlated signals, while legitimate returns remain geometry-dependent and decorrelated across channels.
Attack Simulation Pipeline
A practical obstacle is the absence of public full-waveform LiDAR datasets with realistic jamming attacks; the authors resolve this by generating synthetic full-waveform attacks from public datasets (KITTI, nuScenes, Waymo). Their simulator converts point cloud data into waveform tensors via a physics-based model, superimposes simulated jamming pulses (with randomization in timing and amplitude), and introduces observation noise. The model incorporates simultaneous laser sensing, where receivers measuring at the same time receive identical attack pulses, faithfully reproducing hardware behavior.
This approach enables generalizable learning, as models are trained on challenging synthetic conditions surpassing state-of-the-art (attack amplitude, 10 MHz pulse interval, randomized jitter). Real-world experiments with production hardware confirm training-transfer capability.
PULSAR-Net Architecture
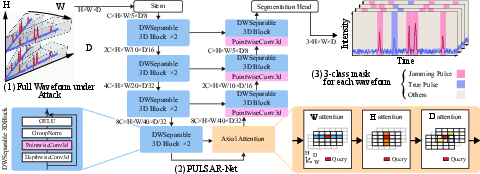
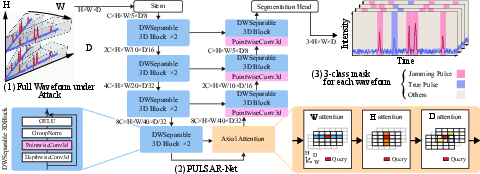
Figure 3: PULSAR-Net employs a U-Net-inspired structure with depthwise-separable 3D convolutions and axial attention, supporting efficient spatial-temporal feature modeling at scale.
The core of the approach is a U-Net-style 3D convolutional network that operates on the (channel × azimuth × temporal) full-waveform tensor. The architecture introduces three critical components:
- Depthwise-Separable 3D Convolutions: For computational efficiency, large 3D convolutions are factorized, greatly reducing parameter count and increasing throughput for high-resolution full-waveform data.
- Axial Spatial-Temporal Attention: Self-attention is decoupled across spatial (azimuth and elevation) and temporal axes, enabling fine-grained modeling of local and cross-channel dependencies at manageable computational cost.
- Segmentation Mask Head: Instead of directly regressing a denoised waveform, the model outputs voxel-wise segmentation masks for background, legitimate reflections, and attack pulses, enabling targeted suppression of attack-induced peaks and robust point recovery.
Weighted cross-entropy and Dice loss are combined to address the class imbalance inherent in segmentation, yielding accurate suppression of adversarial pulses while retaining legitimate geometry.
Numerical Evaluation
Evaluation is performed with rigorous synthetic and real-world scenarios:
- Point-level recovery: On nuScenes-J and KITTI-J with realistic simultaneous sensing (ϕ≥4), PULSAR-Net achieves ≥82% (nuScenes) and ≥89% (KITTI) recovery rate for points in the attacked region, versus <46% for all baselines. At a low ϕ=1, defenses collapse, confirming the necessity of simultaneous sensing.
- Object detector-level mAP: For strong 3D detectors (PointPillars, CenterPoint, PV-RCNN), PULSAR-Net recovers mAP to ≈65% (vs. benign ≈70%) for nuScenes-J and ≈55% for KITTI-J, while the strongest baseline remains below 40%.
- Transferability: Cross-dataset transfer shows that models trained on nuScenes-J maintain high performance on KITTI-J, demonstrating physics-level rather than dataset-level learning.
- Efficiency: Inference runs at 31.7 FPS on RTX5090 (well above 10–20 FPS in-industry), suitable for real-time AV applications.
Real-World Validation
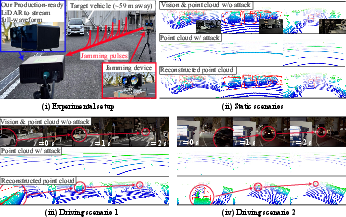
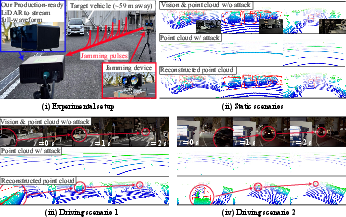
Figure 4: Schematic of the real-world jamming attack setup and qualitative results showing raw, jammed, and PULSAR-Net reconstructed point clouds for both static and driving scenarios.
Deployment with a hardware LiDAR platform (custom firmware, full-waveform access, ϕ=96) and real jamming devices shows:
- Static: Jamming reduces mAP to near zero (0–0.1 mAP); PULSAR-Net restores CenterPoint mAP to 69.4 (benign: 67.1) and achieves 91.7% per-vehicle recovery.
- Dynamic: For moving vehicles (up to 30.5 km/h), mAP consistently recovers to 63.1 (benign not available), with 73.2% vehicle recovery, even though the model was trained only on synthetic attacks.
This generalization from synthetic to hardware is a strong result, showing both the fidelity of the attack simulation and the architecture's inductive bias toward physical signal characteristics.
Implications, Limitations, and Future Directions
Theoretical significance: The demonstration that full-waveform data and multi-channel temporal statistics enable jamming defense contradicts previous assumptions of unfeasibility for post-processing defenses and opens new lines of research into signal-domain (rather than output-domain) robustness for sensor security.
Practical impact: Implementation is feasible on modern hardware with negligible latency cost. The method is applicable to most commercial multi-channel LiDARs if manufacturers expose the required full-waveform data. The critical dependency is simultaneous sensing—sensors with single-shot operation are not defendable with this pipeline.
Limitations and failure modes: The attack model assumes that adversaries cannot inject independently controlled pulses for each receiver channel during simultaneous sensing—a limitation inherent in hardware constraints and current attack technology. False positives (ghost points) may occur, but mAP metrics implicitly penalize over-detection. Attack-detection should be coupled upstream to minimize unnecessary compute.
Future developments: The presented attack simulation and defense mechanism set a new baseline for LiDAR robustness; future work will likely target:
- Adaptive adversarial techniques aiming to break cross-channel assumptions.
- End-to-end AV stack integration assessing downstream control and planning under attack+defense.
- Full open-sourcing of waveform datasets for reproducibility and extensibility to novel threat models.
Conclusion
PULSAR-Net provides a neural signal-processing approach that robustly reconstructs LiDAR point clouds corrupted by otherwise unmitigable jamming attacks, exploiting underutilized physical and hardware properties (full-waveform and simultaneous sensing) of modern sensors. Empirical recovery rates of up to 92% in real-world static and 73% in driving scenarios, matched with scalable deployment, fill a previously unaddressed gap in AV sensor security engineering. The architecture and pipeline delineate best practices for future LiDAR defense and suggest that access to richer sensor data is crucial for robust autonomy.