Wigner's Friend as a Circuit: Inter-Branch Communication Witness Benchmarks on Superconducting Quantum Hardware
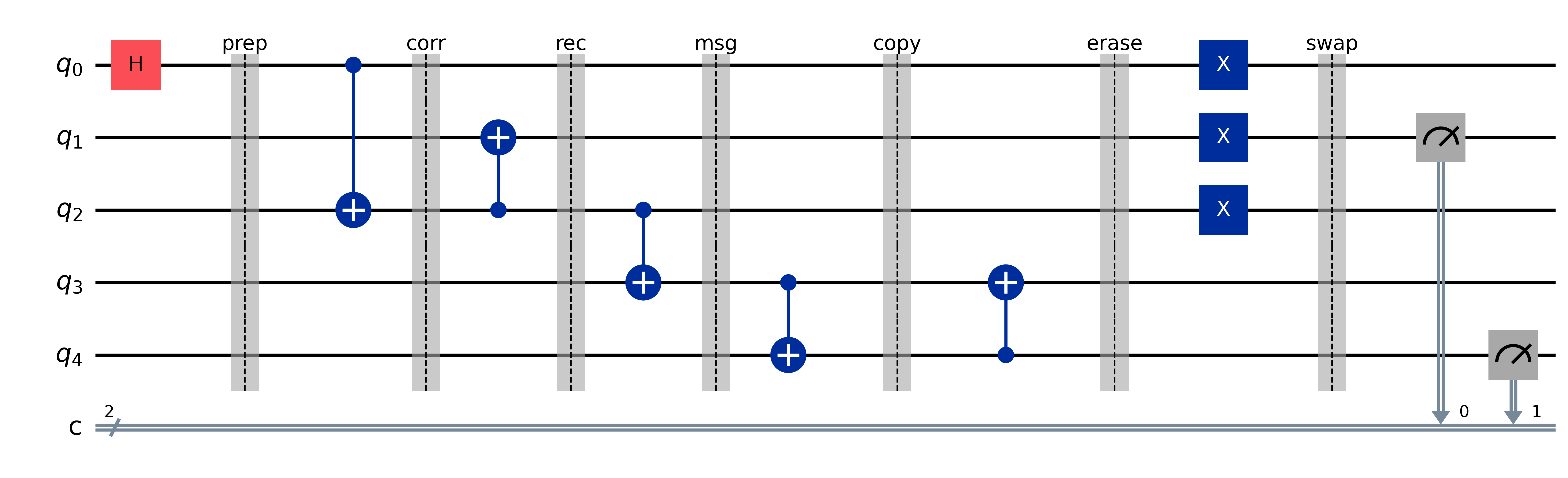
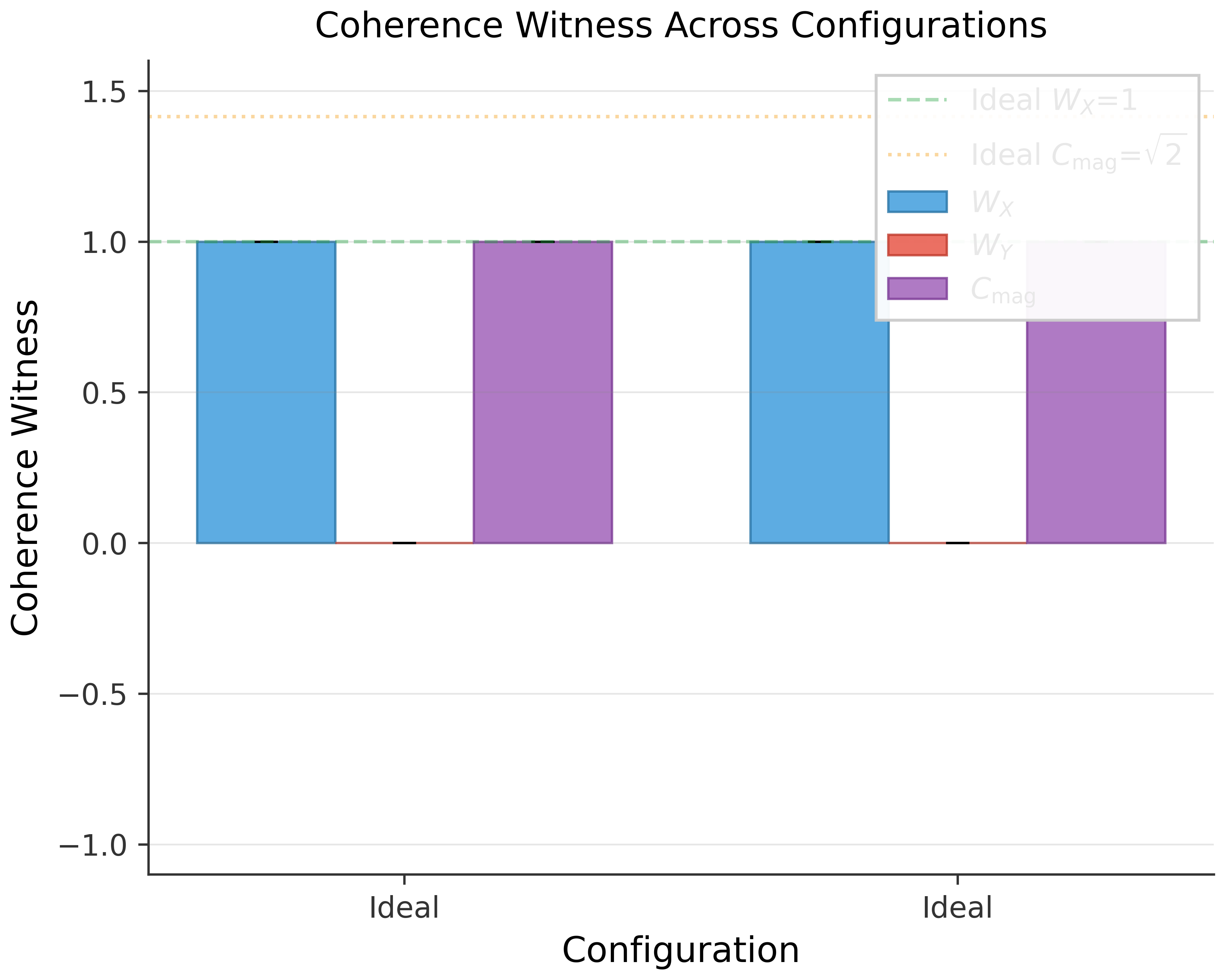
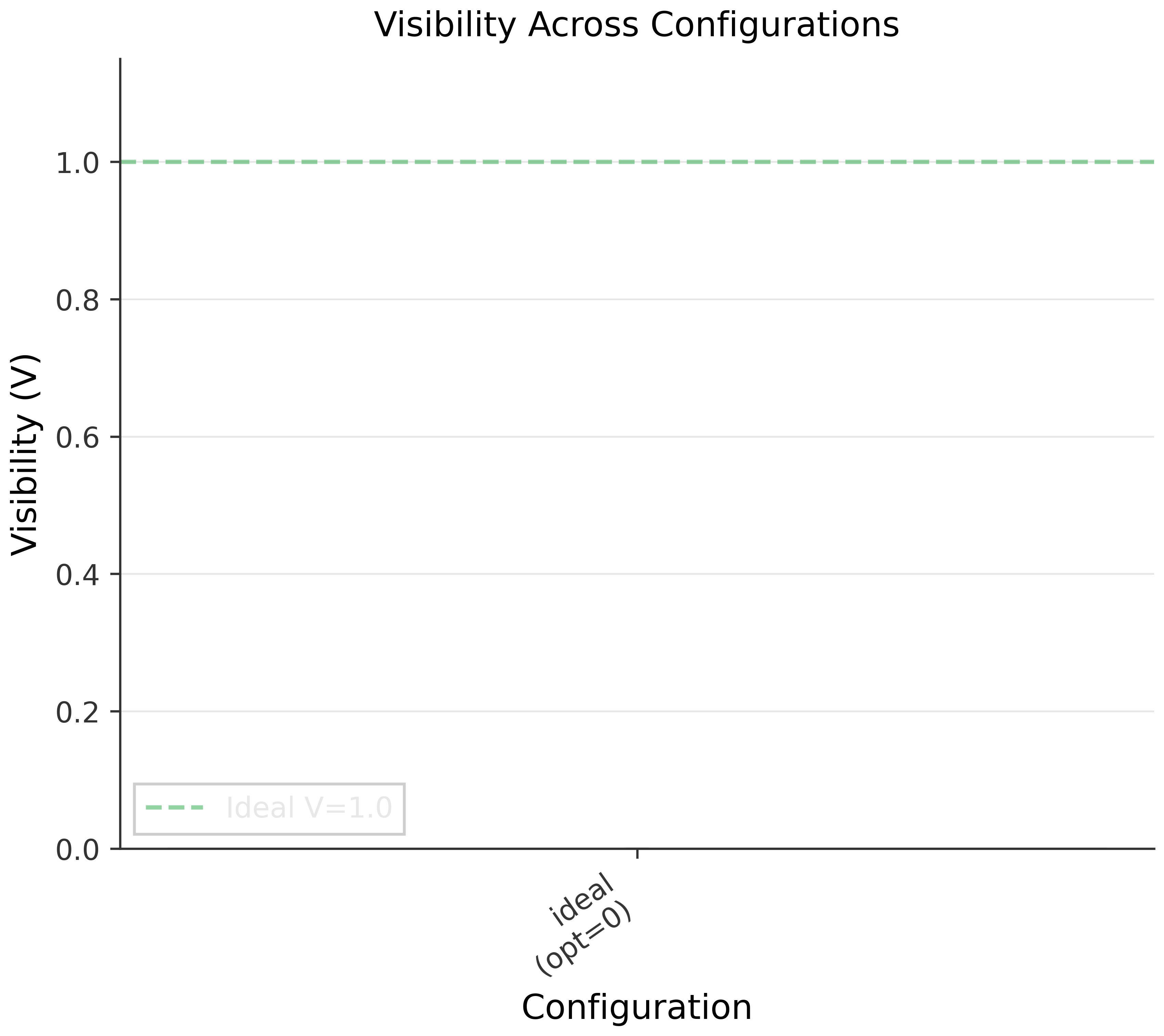
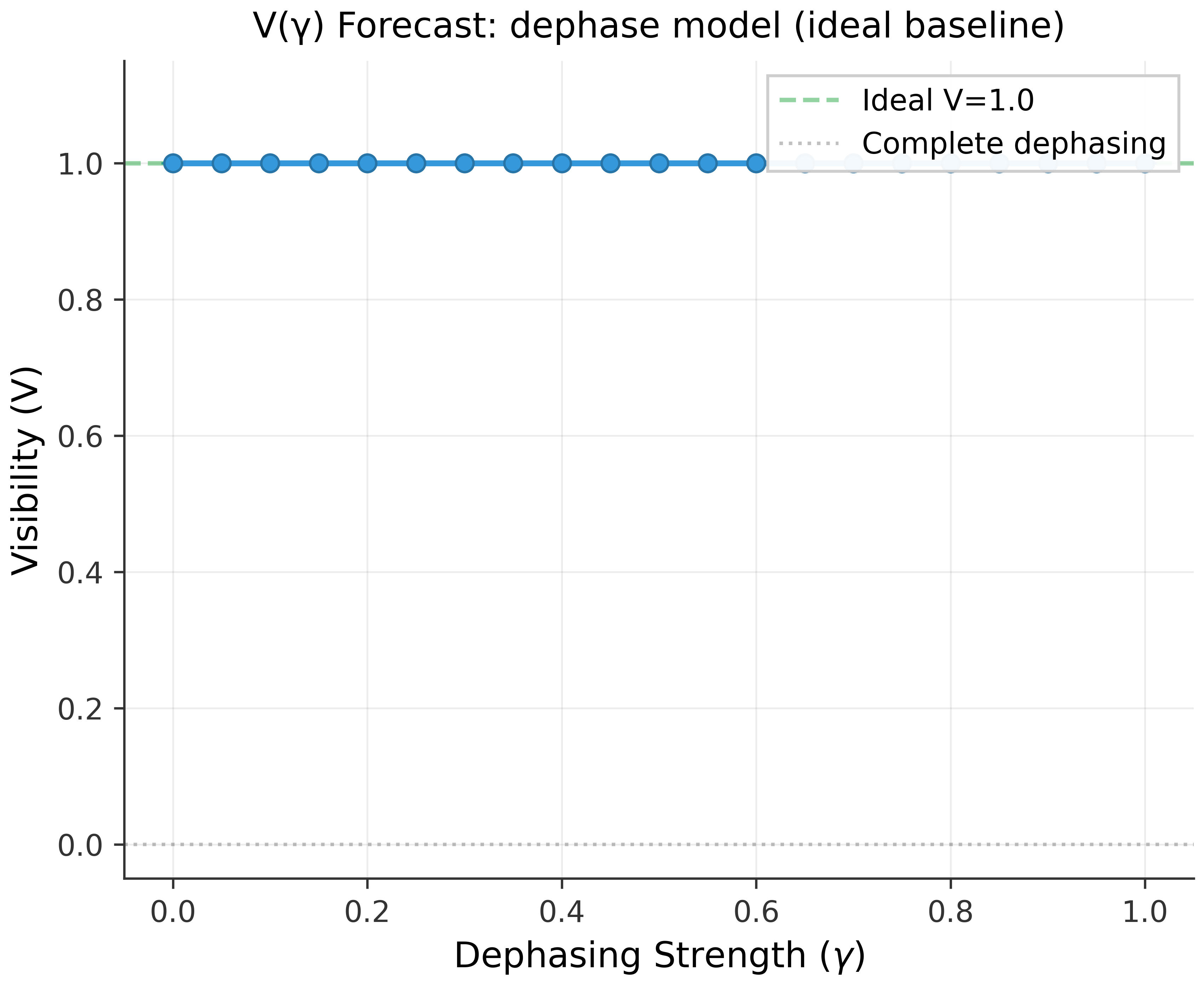
Abstract: We implement and benchmark on IBM Quantum hardware the circuit family proposed by Violaris for estimating operational inter-branch communication witnesses, defined as correlations in classical measurement records produced by compiled Wigner's-friend-style circuits. We realize a five-qubit instance of the protocol as an inter-register message-transfer pattern within a single circuit, rather than physical signaling, and evaluate its behavior under realistic device noise and compilation constraints. The circuit encodes branch-conditioned evolution of an observer subsystem whose dynamics depend on a control qubit, followed by a controlled transfer operation that probes correlations between conditional measurement contexts. Executing on the ibm_fez backend with 20000 shots, we observe population-based visibility of 0.877, coherence witnesses of 0.840 and -0.811 along orthogonal axes, and a phase-sensitive magnitude of approximately 1.17. While the visibility metric is insensitive to some classes of dephasing, the coherence witnesses provide complementary sensitivity to off-diagonal noise. This work does not test or discriminate among interpretations of quantum mechanics. Instead, it provides a reproducible operational constraint pipeline for evaluating detectability of non-ideal channels relative to calibrated device noise.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Explain it Like I'm 14
Overview
This paper turns a famous quantum “thought experiment” called Wigner’s friend into a real, small program (a circuit) that runs on an IBM quantum computer. The goal is to see how different “branches” of a quantum process (like two paths of a story that happen at the same time) produce patterns in the measurements. The authors measure special signals, called “witnesses,” that tell how much the branches still behave like a single quantum story instead of splitting into separate, non-communicating stories. They also share everything needed so other people can repeat the experiment.
Key Questions
The paper asks a few simple, practical questions:
- Can we build and run a small Wigner’s-friend-style circuit on today’s quantum hardware?
- Can we measure more than just basic outcomes, and capture “coherence” (the quantum kind of togetherness) between branches?
- How do the real device results compare to computer simulations that include the device’s known noise?
- If we pretend to add extra “blurring” or “collapse-like” effects into the circuit, would our witnesses be able to notice them?
Methods and Approach
Think of the circuit like a short play with five actors (qubits). Each actor has a role:
- Q (the control): like flipping a quantum coin to decide which branch of the story we follow.
- R (the reference): carries a simple message we can check later.
- F (the “friend”): the observer inside the experiment whose state changes based on Q’s branch.
- P (the probe): helps us read out the final correlations.
- An extra helper qubit: used during the branch-transfer step but not measured in the main witness tests.
The circuit has three stages:
- Branch-conditioned evolution: the friend F evolves differently depending on Q’s state, creating two branch histories in superposition (both happen at once, quantum-style).
- Controlled message transfer: operations connect R, F, and P so that their results are correlated depending on the branches.
- Measurement in different “views”:
- Visibility V: measure in the normal computational view (like checking 0s and 1s directly). This mostly looks at populations (how often each outcome appears).
- Coherence witnesses WX and WY: first rotate how we look at the qubits (change the “view” with simple gates), then measure. This reveals off-diagonal coherence—quantum togetherness that visibility can miss.
To make WX and WY understandable: imagine looking at a spinning coin from different angles. Measuring in the X or Y basis is like turning your head to different angles to see patterns you’d miss if you only looked straight down at heads vs tails. The witnesses are computed by checking whether the number of 1-bits across Q, R, F, and P is even or odd—like tallying whether there’s an even or odd count and using that to estimate the quantum correlations.
They ran each circuit many times (“shots,” like repeating an experiment 20,000 times) on an IBM device named ibm_fez. They also built a simulator tuned to that device’s quirks (its known error rates and coherence times) to compare with hardware results. This is called a backend-matched noise model: a best-effort simulation that approximates the device’s behavior, though it can’t capture everything perfectly.
Main Results and Why They Matter
Here are the headline numbers from real hardware (with 20,000 repeats):
- Visibility: V ≈ 0.877 (ideal would be 1.0)
- Coherence witnesses: WX ≈ 0.840 and WY ≈ −0.811 (ideal would be WX = 1 and WY = −1)
- Combined coherence magnitude: C_mag ≈ 1.167 (ideal ≈ 1.414)
What this means:
- The device shows strong coherence, but less than perfect—exactly what you expect when real hardware adds noise.
- The witnesses WX and WY capture coherence that the simple visibility V might not fully reveal. In other words, just counting outcomes can miss certain quantum features, but these witnesses can pick them up.
- The results match the idea that the circuit behaves quantum mechanically, with ordinary device noise. There’s no sign of anything beyond standard quantum theory.
Extra useful piece:
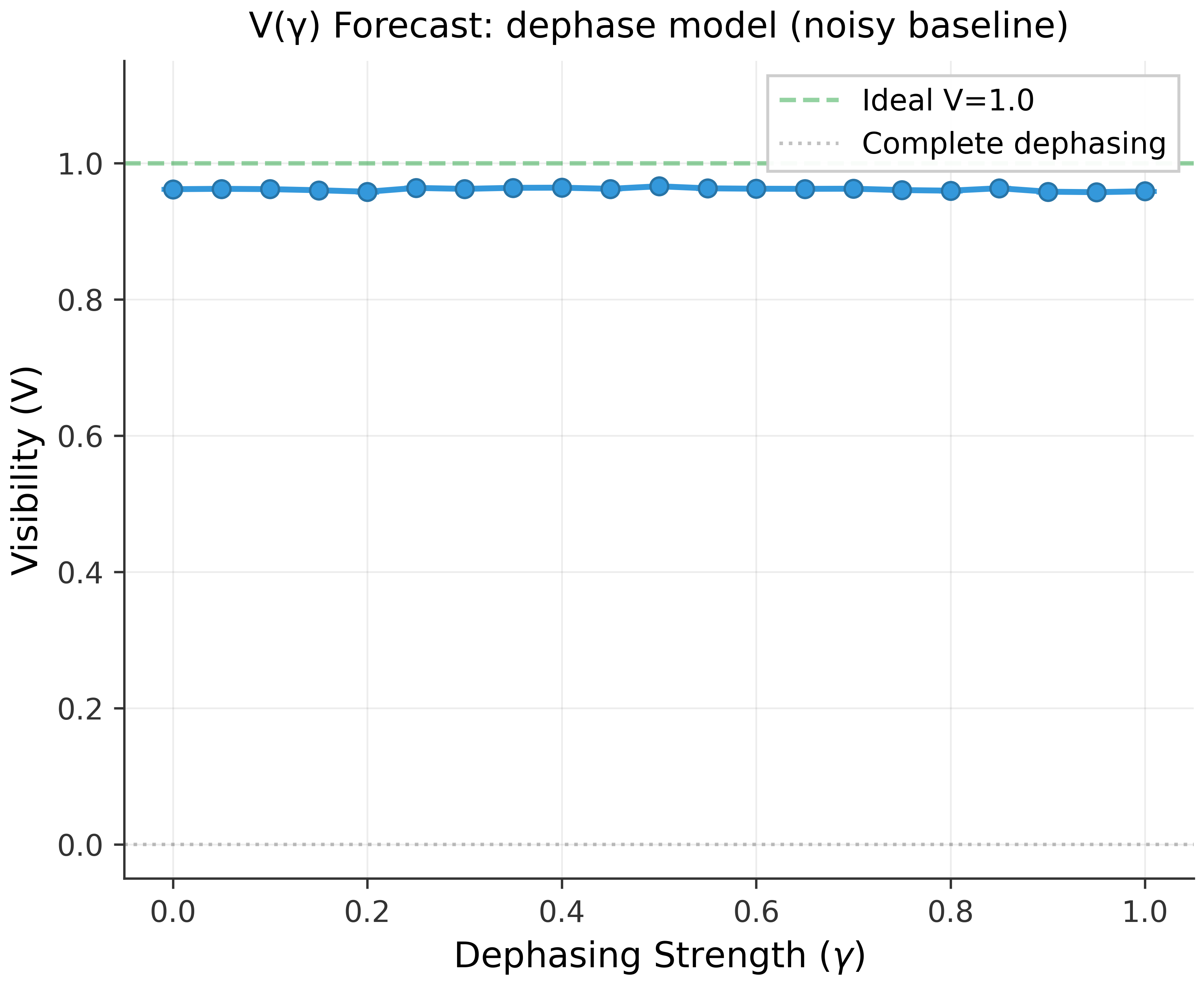
- The authors show a “constraint pipeline.” Imagine you insert a pretend dephasing (like a blur that reduces quantum togetherness) at a specific point in the circuit with strength λ. You simulate how the witnesses change as λ increases. If the real hardware witnesses are stronger than your “blurred” predictions past some λ, then you can say “λ must be smaller than this, otherwise we would have noticed.” This gives a practical way to set bounds on nonunitary (collapse-like) effects.
Implications and Potential Impact
- The paper does not claim to prove or disprove any big interpretation of quantum mechanics (like Many-Worlds or Copenhagen). Those interpretations make the same predictions for this kind of unitary circuit.
- It does show that:
- Wigner’s-friend-style circuits can be compiled and run on today’s quantum hardware.
- Coherence witnesses are powerful tools for seeing quantum features that basic measurements might miss.
- There is a clear, reproducible method to test for extra “non-quantum” effects by inserting toy models and checking when witnesses would detect them.
- Because everything (code, job IDs, calibration data) is shared, other groups can verify results, extend the tests, and try them on different kinds of quantum machines (superconducting, ion traps, neutral atoms, photonics). This can help map how hardware design and compilation choices affect these foundational circuit primitives, and set better standards for future, more sensitive tests.
Knowledge Gaps
Knowledge gaps, limitations, and open questions
The following list identifies what remains missing, uncertain, or unexplored, focusing on concrete items future researchers can act on:
- Single-backend scope: Results are from a single IBM backend (
ibm_fez) and a single execution window; replicate across multiple backends and dates to quantify device-to-device variability and temporal drift. - Absent gate-level circuit specification: The paper does not report the exact gate sequence, total depth, 1Q/2Q gate counts, and physical qubit mapping used; provide these to enable resource/fidelity auditing and reproducibility independent of the bundle.
- Missing circuit schematic in the paper: The primary circuit figure is a placeholder; include the final transpiled circuit diagram in-text with physical qubit labels.
- No error mitigation applied: Evaluate randomized compiling, Pauli twirling, zero-noise extrapolation, dynamical decoupling, and readout error mitigation, and quantify their impact on the witness metrics and channel constraints.
- Readout calibration and mitigation: Characterize and correct measurement assignment errors (per-qubit and correlated readout) and report their effect on , , , and .
- Crosstalk and leakage characterization: Measure and model coherent crosstalk, spectator effects, and leakage (e.g., via spectroscopy, leakage RB), and incorporate them into simulations and uncertainty budgets.
- Noise-model fidelity: The
NoiseModel.from_backend()proxy omits coherent errors, drift, crosstalk, and leakage; validate and refine with randomized benchmarking, cycle benchmarking, and gate-set tomography to build more predictive noise models. - Statistical treatment: Uncertainties use shot-noise only; develop a full error budget including systematics (drift, calibration uncertainty, model mismatch), bootstrap estimates, and hypothesis tests comparing hardware to unitary predictions.
- Nonunitary channel constraints not quantified: The pipeline is described but no concrete bounds (e.g., with confidence intervals) are reported; compute and publish numeric constraints for multiple insertion points and channel families.
- Insertion-point sensitivity: Systematically vary where channels are inserted (pre/post branch split, transfer operation, measurement rotations) and quantify identifiability and sensitivity of each witness to those locations.
- Channel family coverage: Test beyond single-qubit dephasing (e.g., amplitude damping, depolarizing, stochastic resets, correlated multi-qubit dephasing, collapse-like toy models) and report detectability thresholds for each.
- SPAM robustness: Assess and design SPAM-insensitive estimators or apply gate-set tomography to decouple state-preparation and measurement errors from coherence witnesses.
- Scaling with friend-register size and branch divergence: Extend to -qubit friend states with increasing Hamming distance and empirically derive a complexity–coherence scaling law (depth, 2Q overhead, fidelity loss).
- Cross-modality replication: Execute the same logical primitive on ion-trap, neutral atom, photonic, and annealing-style hardware to benchmark platform-specific compilation tax and noise signatures.
- Transpiler sensitivity: Quantify the effect of optimization level, layout selection, gate decomposition choices (e.g., pulse-efficient CX), and routing on witness values and noise susceptibility.
- Qubit-mapping dependence: Vary physical qubit assignments systematically and correlate witness performance with device characteristics (coupling strengths, , readout fidelity).
- Auxiliary qubit measurement: Investigate measuring the auxiliary qubit and alternative witness definitions to test whether unmeasured degrees of freedom hide or enhance correlations.
- Post-selection bias in visibility: The visibility conditions on ; analyze potential selection bias and compare to unconditional or alternative conditional metrics.
- Phase calibration and basis-rotation integrity: Validate rotations and frame phases, and study the stability and physical significance of the sign of across runs and compilation variants.
- Shot-scaling study: Determine the sample complexity needed to reach specified detectability thresholds and how uncertainties scale with shots for each witness.
- Time-resolved stability: Run calibration-synchronized repeats and time-series experiments to separate drift-induced changes from intrinsic circuit behavior.
- State/process tomography: Perform partial or full tomography (or compressed/twirl-based variants) on the four-qubit subset to directly estimate coherence and entanglement metrics and cross-check parity witnesses.
- Classical correlation baselines: Construct classical-noise surrogates that could mimic the observed inter-branch signatures and design discriminators separating coherent interference from classical correlated errors.
- Undefined parameter
--mu: The CLI uses a--muflag without definition in-text; specify its meaning, range, and effect on circuit behavior and witnesses. - Gate-level error attribution: Benchmark the gates composing the controlled transfer (e.g., CX/CZ) to apportion witness degradation to specific operations and inform targeted mitigation.
- Uncertainty propagation in channel estimates: The dephasing example yields a point estimate for but does not propagate combined uncertainties; derive confidence intervals and report conservative bounds.
- Spectator-qubit modeling: Include spectator qubits and realistic coupling in simulations to capture multi-qubit noise that may affect the measured subset.
- Leakage detection in analysis: Add leakage monitors and analysis (e.g., via qutrit-aware readout) to ensure off-computational-state excursions are detected and modeled.
Practical Applications
Immediate Applications
Below is a set of actionable, sector-linked use cases that can be deployed with current tools and hardware, together with key assumptions and dependencies.
- Coherence-aware hardware benchmarking suite (quantum hardware industry; software tooling)
- Use the paper’s coherence witnesses (WX, WY) and visibility (V) to characterize off-diagonal coherence and population-level behavior for each backend, producing a per-device “coherence profile.”
- Potential tools/products/workflows: “Coherence Witness Test Suite” integrated with Qiskit; automated report generation with SHA256-verified artifacts; dashboard visualization of V, WX, WY, Cmag over time.
- Assumptions/dependencies: Access to IBM Quantum or similar platforms; reliable basis rotations and multi-qubit parity measurements; stable calibration data snapshots.
- Noise-model validation and drift monitoring (quantum cloud operations; reliability engineering)
- Compare hardware measurements against backend-matched Qiskit Aer simulations to quantify drift, crosstalk, or miscalibration beyond the snapshot model.
- Potential tools/products/workflows: “Noise Audit Dashboard” highlighting deviations between hardware and backend-matched simulation; alerts when witness values degrade beyond thresholds.
- Assumptions/dependencies: NoiseModel.from_backend() captures the dominant error channels; frequent calibration snapshots; storage of provenance (job IDs, software versions).
- Pre-run job health gate for enterprise workloads (finance, chemistry; workload orchestration)
- Run short witness circuits immediately before large jobs to gate execution if coherence metrics fall below a threshold, avoiding wasted runs and misleading results.
- Potential tools/products/workflows: “Job Health Gate” integrated into enterprise orchestrators (e.g., pre-flight checks in Qiskit Runtime workflows).
- Assumptions/dependencies: Sufficient shot budget and queue priority; policy for acceptable thresholds; rapid turnaround for health checks.
- Error mitigation A/B testing with coherence-sensitive metrics (software; algorithm engineering)
- Evaluate randomized compiling, Pauli twirling, dynamical decoupling, and ZNE directly on WX/WY rather than only on output bitstring fidelity.
- Potential tools/products/workflows: “Mitigation Evaluator” that runs paired circuits with/without mitigation and reports deltas in WX, WY, V.
- Assumptions/dependencies: Access to mitigation passes; consistent transpilation strategies; sufficient shots for statistical power.
- Witness-guided transpiler selection (software; compiler/runtime)
- Select layout, optimization level, and routing strategies that preserve coherence-sensitive observables, not just gate count.
- Potential tools/products/workflows: “Witness-Guided Transpiler” plugin that optimizes for parity correlator robustness; layout scoring by expected WX/WY impact.
- Assumptions/dependencies: Access to transpiler internals; reliable heuristics linking compilation choices to witness degradation.
- Cross-backend procurement scoring and vendor comparison (policy; procurement; industry benchmarking)
- Use standardized witness metrics to compare cloud providers and devices, informing procurement and SLAs.
- Potential tools/products/workflows: “Coherence Benchmark Cards” that summarize V, WX, WY, Cmag with reproducible provenance.
- Assumptions/dependencies: Agreement on benchmark protocols; comparable shot budgets; alignment on measurement settings.
- Reproducibility and audit trail adoption (academia; policy; journals/funders)
- Implement provenance bundles (job IDs, calibration snapshots, software versions, SHA256 manifests) as required submission artifacts for quantum experiments.
- Potential tools/products/workflows: “Quantum Provenance Bundle” templates; CI hooks that auto-generate manifests and store artifacts.
- Assumptions/dependencies: Platform APIs expose sufficient metadata; journals/funders accept and enforce standards.
- Foundational constraint pipeline for nonunitary channel families (academia; quantum foundations)
- Use the paper’s parameterized dephasing/collapse-like toy channels to set detectability bounds relative to observed witness values and device noise bands.
- Potential tools/products/workflows: “Detectability Curve Generator” producing λmax bounds per insertion point; sensitivity reports by observable.
- Assumptions/dependencies: Correct mapping between toy channels and suspected physical processes; insertion-point specificity; adequate shot counts.
- Education and training modules (education; daily life for learners)
- Incorporate the branch-transfer circuit and witness measurements into course labs to teach basis rotations, multi-qubit parity estimation, and reproducibility practices.
- Potential tools/products/workflows: Instructor notebooks; student assignments that replicate bundle commands; grading via manifest verification.
- Assumptions/dependencies: Student access to quantum cloud or local simulators; stable software environments (Qiskit 2.3.0, Aer 0.17.2).
Long-Term Applications
The following applications require further research, scaling, multi-backend replication, or ecosystem development before broad deployment.
- Standardized coherence-witness benchmarks and SLAs (policy; industry standards)
- Establish NIST-like or consortium standards that include WX, WY, Cmag alongside gate/error rates, with minimum acceptable thresholds in cloud SLAs.
- Potential tools/products/workflows: Formal benchmark specifications; compliance testing suites; certification programs.
- Assumptions/dependencies: Community consensus; cross-platform reproducibility; participation by major providers.
- Cross-modality “compilation tax” and connectivity scaling law (hardware R&D; platform selection)
- Develop predictive models linking device topology/connectivity to fidelity loss for inter-branch communication primitives, aiding architecture design and workload placement.
- Potential tools/products/workflows: “Compilation Tax Estimator” that forecasts depth/2Q-gate overhead and expected witness degradation per architecture.
- Assumptions/dependencies: Extensive multi-platform datasets; robust modeling of crosstalk and coherent errors; standardized circuit templates.
- Coherence-aware workload schedulers (enterprise quantum computing; finance/chemistry)
- Integrate real-time witness telemetry into scheduling decisions, dynamically choosing devices, mitigation strategies, or deferring jobs during drift events.
- Potential tools/products/workflows: “Coherence-Aware Orchestrator” integrated with runtime services; adaptive policies for device selection.
- Assumptions/dependencies: Streaming access to device health metrics; provider support for telemetry; enterprise governance buy-in.
- Logical-qubit and QEC-level diagnostics (hardware; fault tolerance)
- Extend witness measurements to logical qubits to probe coherent error modes beyond population leakage, informing code selection and decoder tuning.
- Potential tools/products/workflows: “Logical Witness Suite” for stabilized subspaces; error signature mapping to decoder parameters.
- Assumptions/dependencies: Availability of small logical qubits; repeatable syndrome extraction; stable fault-tolerant stacks.
- Interpretation-relevant campaigns (academia; quantum foundations)
- Multi-backend, mitigation-exhaustive experiments that probe for persistent deviations consistent with specific nonunitary signatures while excluding plausible noise explanations.
- Potential tools/products/workflows: Global replication networks; anomaly triage pipelines; meta-analysis frameworks.
- Assumptions/dependencies: Higher-fidelity hardware; rigorous control of systematic errors; pre-registered analysis protocols.
- Real-time device health telemetry and adaptive compilation (hardware ops; software)
- Continuous measurement of small witness circuits to feed adaptive compilers that re-route, re-time, or re-basis operations to preserve coherence.
- Potential tools/products/workflows: “Device Health Service” APIs; compiler feedback loops based on WX/WY trends.
- Assumptions/dependencies: Non-invasive health checks; predictable latency; model-based control policies.
- Regulatory transparency and audit frameworks for quantum cloud (policy; governance)
- Mandate provenance bundles and coherence health disclosures in regulated sectors using quantum services (e.g., financial risk modeling audits).
- Potential tools/products/workflows: Regulatory reporting schemas; audit toolkits for third-party verification against manifests.
- Assumptions/dependencies: Sector-specific regulations; alignment with privacy and IP constraints; auditor expertise.
- Hardware design optimization using witness-informed gate sets and layouts (hardware engineering)
- Use witness sensitivity analyses to choose gate implementations (e.g., echoed cross-resonance variants) and coupling patterns that minimize off-diagonal decoherence.
- Potential tools/products/workflows: Design-of-experiment platforms; co-optimization with control firmware and calibration routines.
- Assumptions/dependencies: Iterative hardware–software co-design; accurate models of coherent/crosstalk errors; manufacturing feedback cycles.
- Scalable education and outreach (education; public engagement)
- Global, remote labs with standardized witness benchmarks for students and citizen scientists, reinforcing open-science reproducibility norms.
- Potential tools/products/workflows: MOOC-integrated labs; auto-grading via manifests; community leaderboards of cross-backend results.
- Assumptions/dependencies: Sustained cloud access programs; simplified onboarding; long-term maintenance of courseware.
- Exotic-channel detection frameworks (academia; advanced sensing of nonstandard dynamics)
- If hardware quality improves, use generalized constraint pipelines to bound or detect subtle nonunitary channels beyond simple dephasing, mapping signatures across circuit insertion points.
- Potential tools/products/workflows: “Channel Signature Library” and detection toolkits; hypothesis testing suites with power analyses.
- Assumptions/dependencies: Ultra-stable devices; rigorous differential diagnostics; comprehensive noise inventories.
Glossary
- absoluteness of observed events: Foundational assumption that observed outcomes are definite and observer-independent across time. "Mukherjee and Hance~\cite{mukherjee2025timelike} analyze timelike constraints on ``absoluteness of observed events'' assumptions in Wigner's-friend settings."
- Backend-matched noise modeling: Constructing simulator noise models from current hardware calibrations to approximate device behavior. "Backend-matched noise modeling: We compare hardware results against Qiskit Aer simulations using noise models derived from contemporaneous ibm_fez calibration data~\cite{qiskitaer}."
- branch-conditioned evolution: Circuit evolution that depends on which superposition branch a control qubit selects. "The circuit encodes a branch-conditioned evolution in which an observer subsystem (``Wigner's friend'') evolves differently depending on the state of a control qubit ."
- branch divergence: Growth of differences between branch-specific states as a protocol parameter increases. "Branch divergence scaling: Represent friend-0 and friend-1 states as -qubit bitstrings whose Hamming distance grows under branch evolution."
- branch-transfer circuit primitive: Minimal circuit module implementing conditional transfer between branch-specific states. "Headline metrics for the branch-transfer circuit primitive are summarized in Table~\ref{tab:headline}."
- coherence witnesses: Observables designed to detect off-diagonal quantum coherences that populations might miss. "Coherence witnesses and provide off-diagonal sensitivity complementary to population-based visibility."
- computational basis: The standard Z-basis for measuring qubits (|0⟩, |1⟩ states). "measurement in either the computational basis (for visibility) or rotated bases (for coherence witnesses)."
- controlled message-transfer primitive: A conditional operation that transfers encoded information contingent on a control state. "application of a controlled message-transfer primitive that creates correlations between , , and "
- crosstalk: Undesired interactions between qubits causing correlated errors. "they may fail to fully capture drift, crosstalk, leakage, and coherent errors not characterized by the calibration data."
- dephasing channel: Noise model that suppresses phase coherence without changing populations. "Nonunitary channel constraint pipeline: We demonstrate how parameterized dephasing channels can be constrained relative to observed witness values and device-noise bands."
- error mitigation: Post-processing or circuit-level techniques to reduce the impact of noise on measured observables. "Error mitigation: Apply randomized compiling, Pauli twirling, or zero-noise extrapolation (ZNE) to witness observables, enabling tighter constraints on nonunitary channels."
- Hadamard gate: A single-qubit gate that rotates between computational and X bases. "To measure , we apply a Hadamard gate to each of immediately before Z-basis measurement."
- Hamming distance: Number of differing bit positions between two bitstrings; used to quantify branch separation. "Branch divergence scaling: Represent friend-0 and friend-1 states as -qubit bitstrings whose Hamming distance grows under branch evolution."
- inter-branch communication: Protocols enabling operations or correlations between different superposition branches within a circuit. "Violaris~\cite{violaris2026interbranch} proposes a family of inter-branch communication protocols in which operations on a superposed ``friend'' register enable conditional message transfer between branch-conditioned internal states."
- leakage: Errors where population escapes the computational subspace into non-computational levels. "they may fail to fully capture drift, crosstalk, leakage, and coherent errors not characterized by the calibration data."
- Many-Worlds interpretation: A unitary interpretation of quantum mechanics where all outcomes occur in branching universes. "The Many-Worlds interpretation, Copenhagen-style collapse models, and other unitary completions all predict identical measurement statistics for these circuits when the evolution is unitary."
- NoiseModel.from_backend(): Qiskit Aer utility to build a simulator noise model from hardware calibration data. "We include baseline simulations using Qiskit Aer~\cite{qiskitaer} with noise models constructed via \ \path|NoiseModel.from_backend()| using contemporaneous calibration snapshots of ibm_fez."
- off-diagonal density matrix elements: Coherence terms representing superposition phases; their suppression reduces quantum interference. "Key limitation: Because depends only on diagonal (computational-basis) populations, it can fail to detect suppression of off-diagonal density matrix elements."
- Pauli operators: The set of single-qubit matrices {X, Y, Z} used to define measurements and errors. "where and are the standard Pauli operators."
- Pauli-parity correlators: Multi-qubit measurements of parity in Pauli bases to reveal coherence. "Beyond the standard population-based visibility , we measure multi-qubit Pauli-parity correlators (, ) that are sensitive to off-diagonal coherences potentially missed by ."
- Pauli twirling: Technique that randomizes coherent errors into stochastic Pauli errors to simplify mitigation. "Error mitigation: Apply randomized compiling, Pauli twirling, or zero-noise extrapolation (ZNE) to witness observables, enabling tighter constraints on nonunitary channels."
- Qiskit IBM Runtime: A service for executing quantum programs with managed resources and scheduling on IBM hardware. "Circuits were executed on backend ibm_fez via the IBM Quantum open-access plan using Qiskit IBM Runtime~\cite{qiskitibmruntime}."
- randomized compiling: Method that inserts random gate sequences to convert coherent errors into stochastic noise. "Error mitigation: Apply randomized compiling, Pauli twirling, or zero-noise extrapolation (ZNE) to witness observables, enabling tighter constraints on nonunitary channels."
- readout errors: Measurement inaccuracies causing incorrect bit values at the end of a circuit. "These snapshots ... capture gate error rates, readout errors, and / times at the time of execution."
- statevector: Full wavefunction representation used for ideal (noise-free) simulations. "For ideal statevector evolution with this circuit, and "
- transpilation: Compilation process that maps logical circuits to device-native gates and topology. "suggesting calibration drift, additional noise sources not captured by the model, or transpilation effects at optimization level 2."
- transpiler optimization level: Compiler setting controlling optimization aggressiveness for circuit mapping. "Transpiler optimization level: 2 for hardware runs; 1 for backend-matched noisy simulations"
- unitary evolution: Quantum dynamics preserving norms and coherences; modeled by unitary operators. "Crucially, all measured values remain consistent with unitary evolution plus device noise---no anomalous deviations suggesting nonunitary physics are observed."
- visibility V: Population-based metric derived from conditional probabilities in the Z basis. "The visibility metric (corresponding to bundle mode rp_z) is extracted from Z-basis measurement populations:"
- Wigner's friend: Thought experiment involving an observer inside a quantum measurement scenario, probing perspective and measurement. "The Wigner's friend thought experiment~\cite{wigner1961remarks} and its extensions~\cite{frauchiger2018quantum,brukner2018no} probe foundational questions about unitary quantum dynamics, measurement, and observer perspectives."
- zero-noise extrapolation (ZNE): Error-mitigation technique that infers zero-noise values by fitting measurements at scaled noise levels. "Error mitigation: Apply randomized compiling, Pauli twirling, or zero-noise extrapolation (ZNE) to witness observables, enabling tighter constraints on nonunitary channels."
Collections
Sign up for free to add this paper to one or more collections.