- The paper presents a hierarchical Stackelberg game framework that jointly optimizes SINR and AoI in low-altitude wireless networks under channel access attacks.
- It employs a RIS-assisted defense mechanism with closed-form AoI expressions across M/M/1, D/M/1, and M/D/1 models to ensure robustness against interference.
- Simulations and analytical results confirm convergence to a unique equilibrium, outperforming traditional Nash strategies and baseline approaches.
Introduction and Problem Context
The proliferation of low-altitude wireless networks (LAWNs) is driven by the emerging demands of urban air mobility, drone logistics, and environmental monitoring. LAWNs, underpinned by integrated sensing and communication (ISAC) technologies, must jointly support high-reliability communication and real-time sensing for time-sensitive applications. However, the open nature of low-altitude airspace exposes these networks to sophisticated physical-layer threats, notably channel access attacks wherein adversarial UAVs inject noise to degrade both communication and sensing functionalities.
This paper systematically models and mitigates the impact of adaptive, strategic attackers in LAWNs. The authors propose a hierarchical Stackelberg game-theoretic framework to capture the sequential interactions of a malicious drone (attacker), a legitimate UAV equipped with a reconfigurable intelligent surface (RIS), and a ground ISAC base station (BS). The objective is robust joint optimization of communication signal-to-interference-plus-noise ratio (SINR) and the Age of Information (AoI) for sensing data in adversarial environments (2508.15838).
System and Attack Model
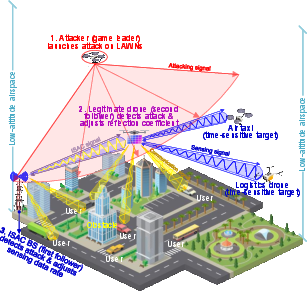
LAWNs are considered as multi-agent networks, comprising a multi-antenna ISAC BS, RIS-aided legitimate UAVs, time-sensitive user nodes, and a malicious UAV executing adaptive channel access attacks. The system topology and roles are illustrated in Figure 1.
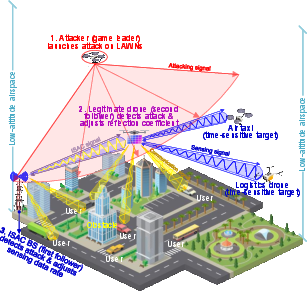
Figure 1: System model of LAWNs under channel access attack, delineating attacker intervention, RIS-assisted mitigation, and adaptive ISAC responses.
The attacker performs protocol spoofing and injects environmental-noise-like interference across multiple channels, strategically evading existing detection mechanisms while degrading system-level ISAC metrics. In response, the legitimate RIS-UAV and BS adapt the RIS gain and sensing data generation rate, respectively, seeking to maintain aggregate network performance under attack. The system incorporates realistic fading channels (Rician for BS-UAV, Rayleigh for other links), stochastic data arrivals, and practical hardware constraints.
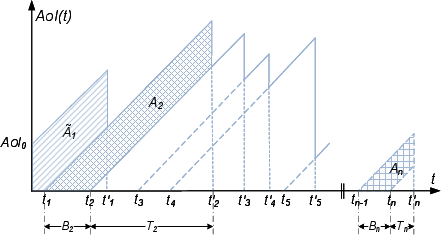
Traditional instantaneous SINR is insufficient for characterizing the freshness and utility of sensing data in dynamic, time-sensitive applications. The authors introduce and rigorously analyze an AoI-based metric to quantify end-to-end information timeliness, deriving closed-form expressions for AoI under M/M/1, D/M/1, and M/D/1 queuing models. The temporal evolution of AoI is depicted in Figure 2.
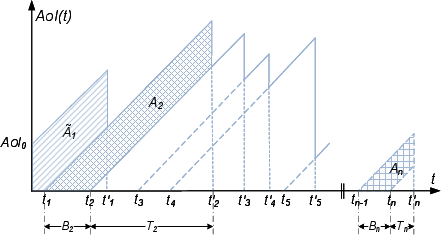
Figure 2: Modeling of AoI metric, capturing the stochastic sawtooth profile induced by data generation, service, and adversarial interference.
The interplay between queuing dynamics, channel access delays, service rates, and attacker strategies is explicitly captured in the AoI expressions, enabling robust optimization over time-averaged sensing quality.
The central defense mechanism is cast as a three-level Stackelberg game:
- Leader: Malicious UAV selects noise injection power to maximize attack efficacy while preserving stealth.
- Second Follower: Legitimate RIS-UAV adapts RIS amplification gain to enhance communications and sensing, subject to energy constraints.
- First Follower: ISAC BS adjusts the sensing data generation rate to balance AoI minimization, SINR satisfaction, and cost.
Utility functions are constructed to encode each agent's objectives, integrating AoI, SINR, and operational costs. The resulting tri-level program is solved via backward induction, leveraging a hybrid Golden Section Search-Parabolic Interpolation (GSSPI) algorithm to handle the non-convex, derivative-free nature of sub-problems, with provable convergence and global optimality.
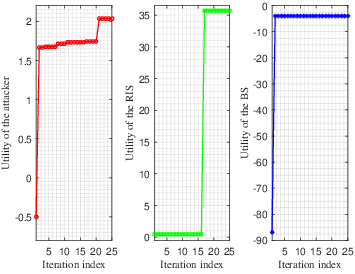
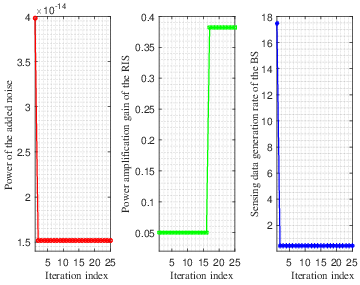
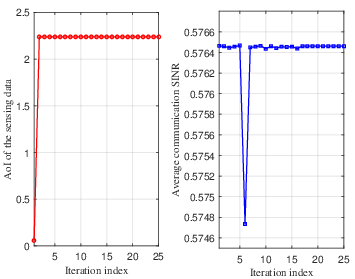
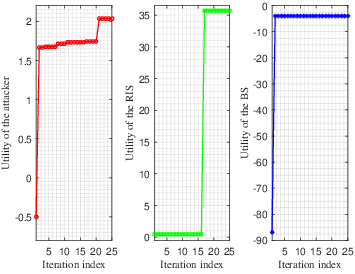
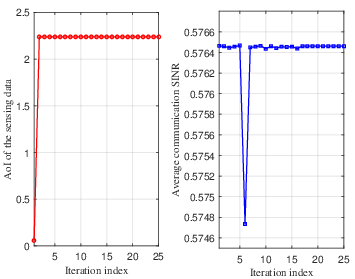
Figure 3: Convergence evaluation of the GSSPI-driven utility optimization, demonstrating rapid and stable approach to equilibrium for all agents.
Analytical results establish the existence and uniqueness of the Stackelberg equilibrium under standard game-theoretic fixed-point conditions.
Evaluation and Numerical Results
Extensive simulation experiments quantify the performance and adaptability of the proposed framework. Key findings include:
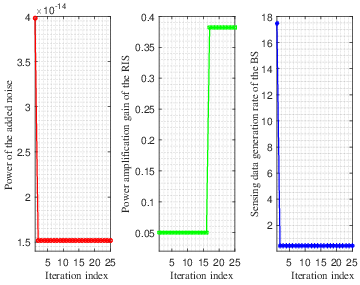
- Convergence and Optimality: Utility functions and all decision variables (sensing rate, RIS gain, attack noise power) converge reliably to equilibrium values within bounded iterations (Figure 3).
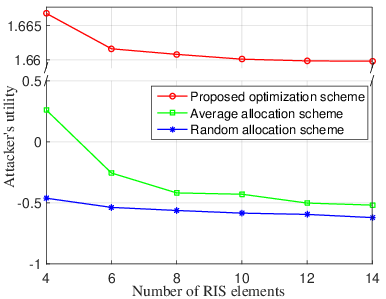
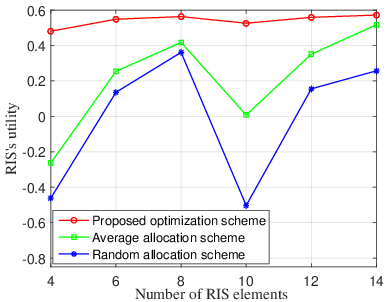
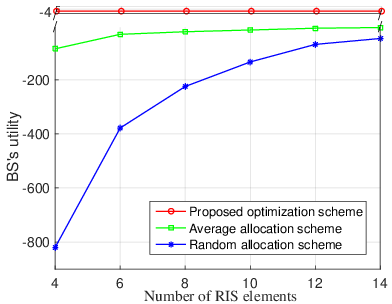
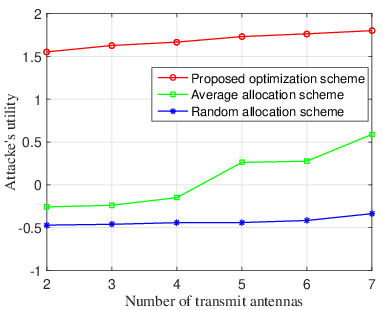
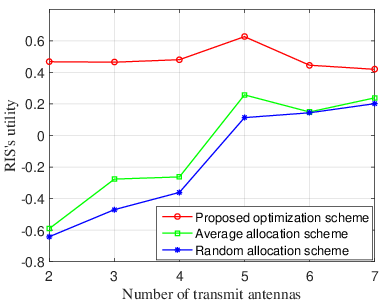
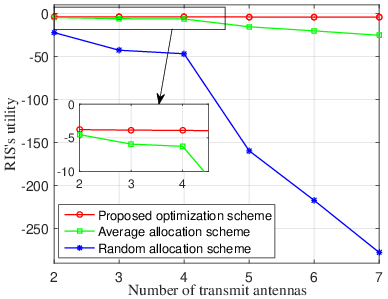
- Variable-Dependent Utility Trends: Increasing the number of RIS reflecting elements improves the BS utility and reduces the attacker's utility, highlighting the efficacy of hardware-based countermeasures (Figure 4). Contrarily, increasing BS transmit antennas can benefit the attacker, reflecting an adversarial exploitation of system-scale effects (Figure 5).
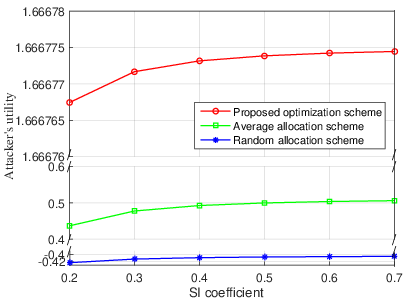
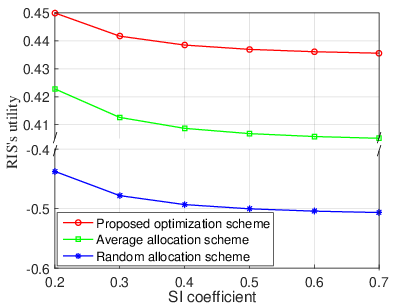
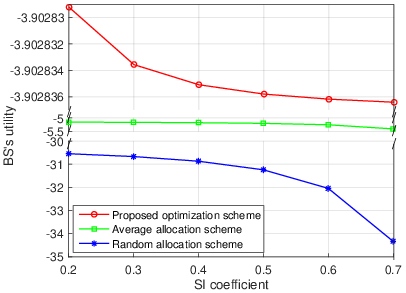
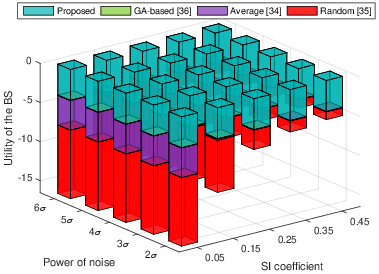
- Self-Interference Impact: Higher self-interference coefficients degrade both legitimate and adversarial utilities, pointing to the necessity of advanced SI cancellation in ISAC receivers (Figure 6).
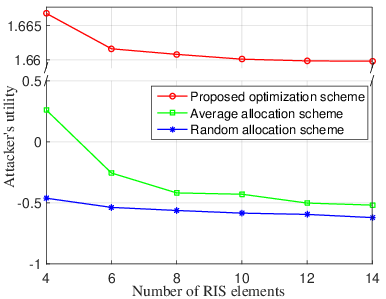
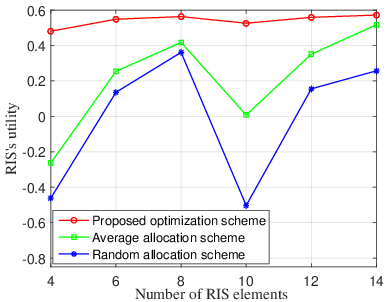
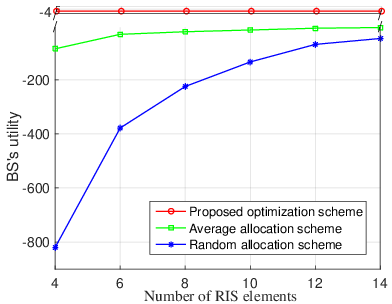
Figure 4: Utility trade-off with varying RIS element numbers—greater RIS capability mitigates attack impact on the BS.
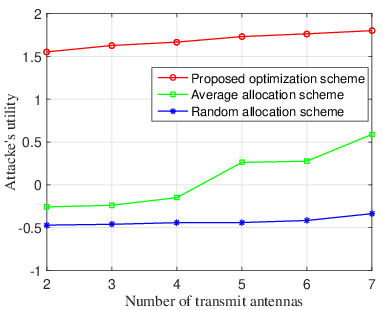
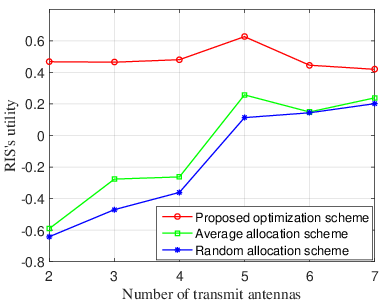
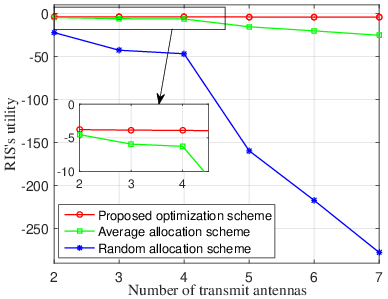
Figure 5: Attack utility growth with increasing transmit antennas—scaling effects must be considered in defense planning.
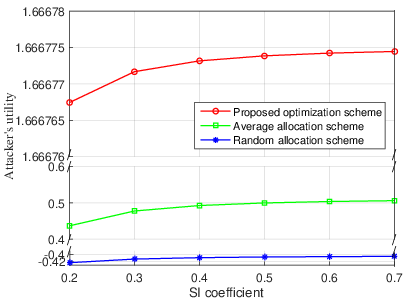
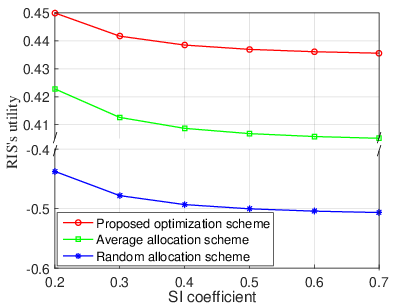
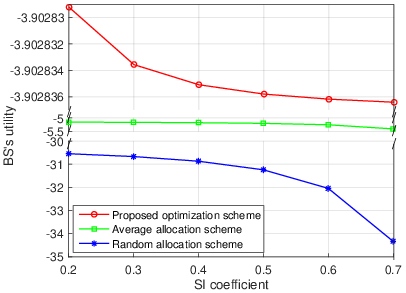
Figure 6: Sensitivity of utilities to self-interference in the ISAC receiver chain.
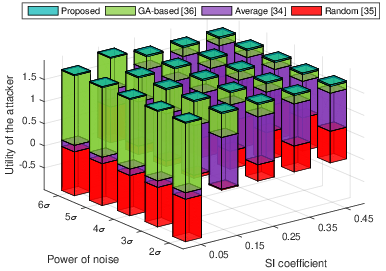
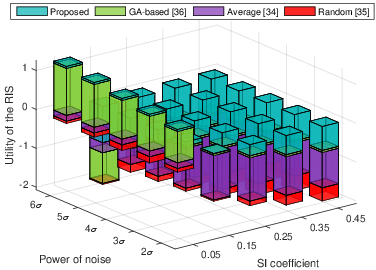
- Algorithmic Benchmarking: The BI-GSSPI approach dominates against average allocation, random, and even genetic algorithm-based baselines, achieving higher utilities, faster convergence, and superior robustness (Figure 7).
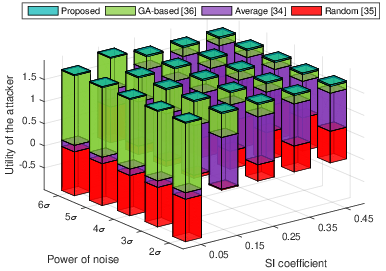
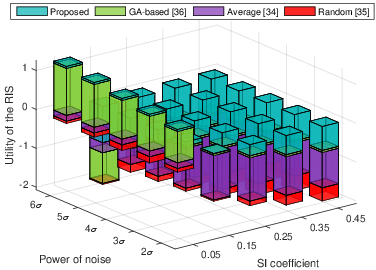
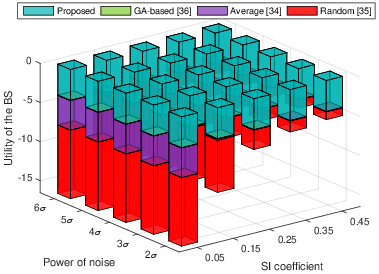
Figure 7: Comparison between the proposed Stackelberg-GSSPI and GA-based optimization, highlighting efficiency and solution quality.
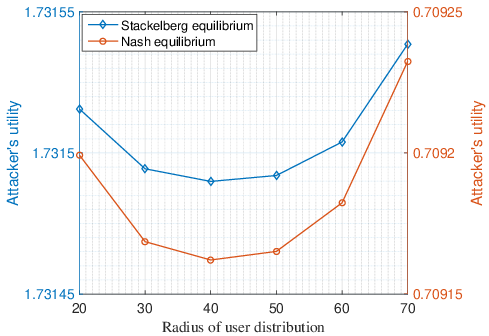
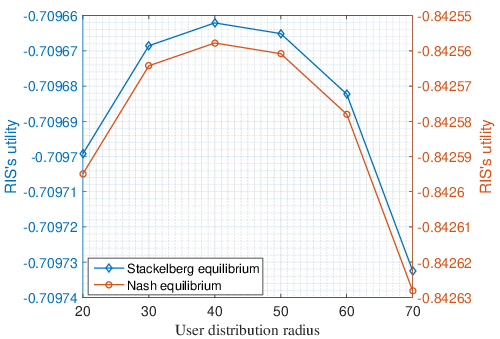
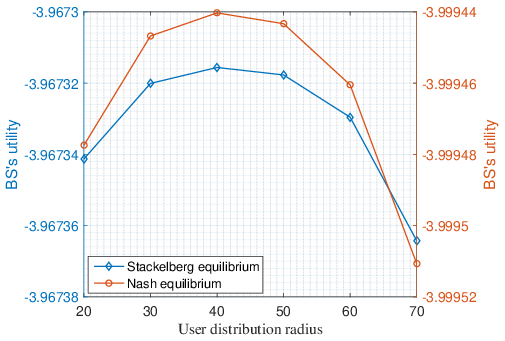
- Equilibrium Comparison: Stackelberg equilibrium consistently outperforms Nash equilibrium, due to its explicit modeling of attacker-leading sequential decision processes (Figure 8).
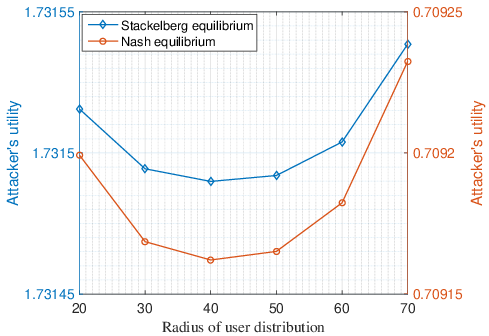
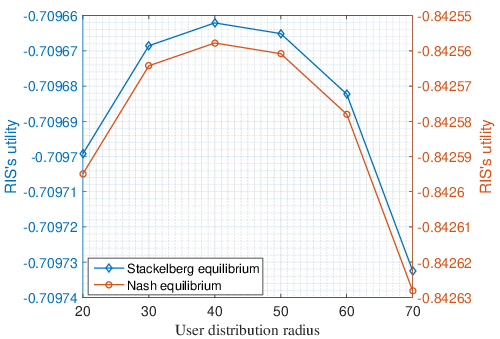
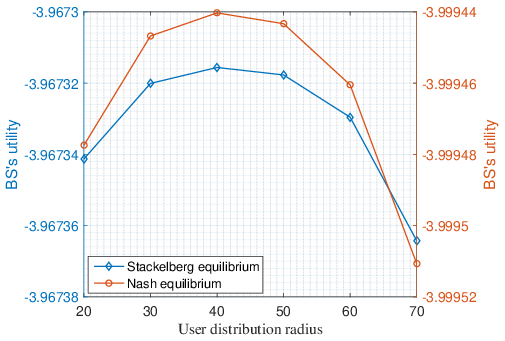
Figure 8: Utility benefit of Stackelberg equilibrium over classical Nash equilibrium, especially in scenarios with adaptive adversaries.
Theoretical and Practical Implications
The analysis confirms that proactive, hierarchical, game-theoretic responses are essential for robust ISAC operation in open, adversarial low-altitude environments. Key implications are:
- RIS design and deployment critically enhance physical layer defense, but must be co-optimized with BS-level strategies.
- AoI provides a rigorous, application-relevant performance metric, especially for time-sensitive control tasks, advocating its use over traditional throughput/SINR metrics in adversarial contexts.
- Stackelberg models outperform static Nash formulations for cyber-physical security as attacker adaptivity and defense causality must be explicitly represented.
- The convergence-guaranteed, derivative-free optimization algorithms enable deployability in resource-constrained, non-differentiable systems.
Future Directions
Potential research extensions involve joint optimization with additional constraints such as energy harvesting, networked control, and cross-layer protocol co-design. Advanced detection and mitigation of adaptive attacks using machine learning techniques (e.g., DRL-augmented Stackelberg games) represent promising directions, as does real-world deployment in urban air mobility scenarios.
Conclusion
The hierarchical Stackelberg defense paradigm demonstrated in this work sets a technical foundation for resilient and reliable ISAC in LAWNs under adaptive channel access attack. The fusion of AoI-driven metrics, game-theoretic optimization, and RIS-based physical layer adaptation advances the state-of-the-art for security-aware low-altitude wireless systems. This approach enables practical, provably robust ISAC service delivery despite dynamic and strategic adversarial interference.