- The paper introduces a robust CACC scheme that uses multiple wireless V2V channels and a resilient data fusion algorithm to reconstruct true acceleration commands even under cyberattacks.
- The method guarantees bounded reconstruction error through majority-based selection from redundant channels, ensuring vehicle platoon stability and enhanced control performance.
- Integration of a discrete-time H∞ controller secures input-to-state stability by mitigating noise and disturbances, even during continuous adversarial attacks.
Robust Cooperative Adaptive Cruise Control under Cyber-Attacks via Multiple V2V Networks
Introduction
Cooperative Adaptive Cruise Control (CACC) technology leverages vehicle-to-vehicle (V2V) communication to enable closely-coupled vehicle platoons for increased highway capacity and improved safety, as well as reduced fuel consumption and emissions. However, the integration of V2V communication channels exposes platoons to cyber-attacks—primarily due to the vulnerabilities inherent in wireless networking. The paper "A Robust CACC Scheme Against Cyberattacks Via Multiple Vehicle-to-Vehicle Networks" (2106.10448) addresses the need for resilience in CACC systems by proposing an architecture that utilizes multiple redundant wireless networks and a robust data fusion algorithm to mitigate attacks and transmission faults.
System Model and Attack Threats
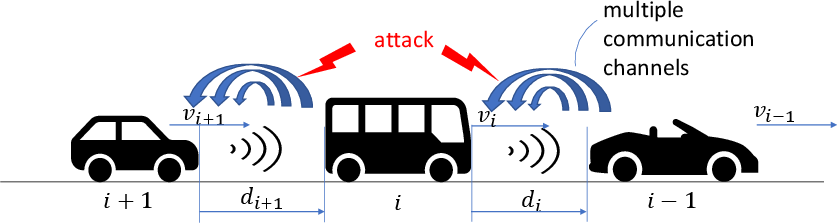
The proposed CACC system is modeled as a platoon of vehicles where each follower receives multiple, independent streams of acceleration command data from its predecessor through different wireless networks (e.g., LTE/5G and DSRC). This redundancy creates the potential for robust estimation and isolation of malicious or faulty channels.
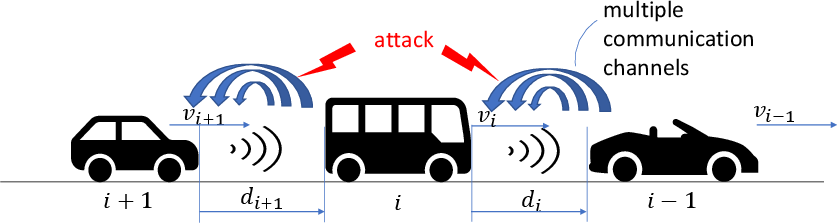
Figure 1: CACC-equipped vehicle platoon under network attacks, where vehicles leverage multiple network channels for V2V communication, with some channels possibly under attack.
Attacks can manifest as arbitrary additive vector corruptions on any subset of the channels, which may be chosen in a time-varying manner. The dominant cyber-physical attack modalities addressed include injection attacks (e.g., false data injection, replay, and jamming) that either disrupt message integrity or introduce spurious signals. The attack model is general: the set of attacked channels at each step is unknown and time-varying, but the attacker is assumed not to control half or more of the communication channels simultaneously.
Secure Data Fusion via Redundant V2V Channels
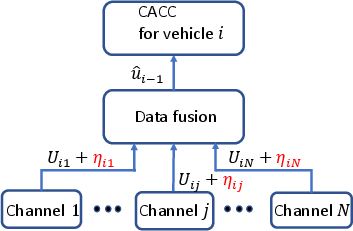
The core enabler of resilience is a data fusion and estimation technique that aggregates possibly compromised channel signals. Let N denote the total number of channels, q the (unknown) upper bound on the number of attacked channels (q<N/2), and ui−1 the true acceleration command sent from vehicle i−1. Each vehicle i receives a vector Ui of measurements from its N inbound channels, each of which may be corrupted by both noise and attack signals.
The critical insight (proved in the paper via contradiction) is that unique reconstruction of ui−1 from Ui is possible if and only if strictly fewer than half of the channels are compromised at each time step (cf. Mo & Sinopoli, 2015; Fawzi et al., 2014). Thus, majority logic can be exploited: attack- and noise-resilient estimation reduces to an appropriate selection over subsets of the received data.
The estimation strategy proceeds by:
- Exhaustively calculating, for all subsets J of size N−q, the statistic πiJ=maxj∈J∣u^iJ−Uij∣ where u^iJ is the mean of the subset.
- Selecting the subset σi with the minimal πiJ.
- Using u^σi as the robust, attack-resilient estimate of ui−1.
The reconstruction error is guaranteed to be bounded by a constant multiple of the worst-case channel noise, independent of the attacker’s injected signal magnitude. An example with N=3 channels and randomized per-step attacks demonstrates that the fusion algorithm can reliably track the true acceleration, maintaining bounded estimation errors even with high attack variance.
Channel Attack Detection and Isolation
Beyond providing resilient estimation, the architecture includes mechanisms for online attack detection and channel isolation:
- A simple thresholding rule based on known channel noise bounds is used: if any channel’s signal deviates from the consensus mean by more than a conservative threshold, an attack is detected.
- Isolation is performed by comparing each channel’s value to a randomly selected "trusted" channel from the identified benign subset, again using a threshold based on expected noise statistics.
The efficiency of this scheme is characterized by empirical hit-rates in simulations, successfully isolating active attacks in the majority of steps even with nonstationary attack profiles and network-induced perturbations.
H∞ Robust Controller Integration
Using estimated, potentially uncertain acceleration commands for feedback can degrade control performance or stability. To mitigate this, the paper integrates a discrete-time H∞ controller for string stability. The controller synthesizes state feedback gains using standard linear matrix inequality (LMI) techniques (Boyd et al., 1994; He & Wang, 2006), incorporating both estimation errors from the fusion stage and sensor/actuator noise.
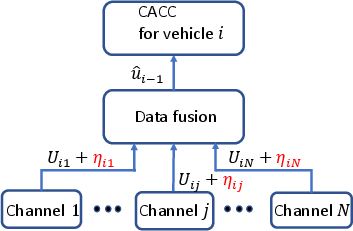
Figure 2: Schematic of the proposed data fusion algorithm as embedded in each vehicle’s controller pipeline.
Key results include:
- The closed-loop platoon dynamics with the H∞ controller and fusion estimator are proven to be Input-to-State Stable (ISS) with respect to aggregate noise and estimation errors, even under continuous adversarial action, provided the q<N/2 assumption holds.
- Simulation with N=3 channels per V2V link and q=1 per time step shows that H∞-optimized gains substantially reduce the attenuation of disturbances and error amplification compared with classical CACC controllers, achieving γ=1.0198 vs. baseline γ=5.1000 in H∞ norm.
Implications, Limitations, and Future Directions
This research provides a concrete framework for enhancing CACC resilience via data-level voting and robust estimation, as opposed to relying solely on cryptographic/secure network protocols or fallback safety logics. The strategy is particularly practical given the heterogeneous multi-channel wireless interfaces available in modern vehicles (DSRC, C-V2X, 4G/5G), and places computational requirements only on local channel subset selection, mean/absolute deviation computation, and LMI-based control law synthesis.
However, the approach assumes a known upper bound q, sufficient channel diversity (N≥3), and that the majority of channels remain uncompromised at each instant—constraints that reflect realistic but not universal attacker models. Further, channel noise bounds must be characterized for thresholds to be robust, and the method assumes that compromised channels are not colluding to mimic valid statistics.
Practical implementation would also require robust channel time-synchronization, rapid attack isolation at the per-packet level, and integration with existing V2V security protocols. Scalability to higher N is feasible but increases computational burden.
Potential future directions include:
- Adaptive estimation of q in real time based on observed channel statistics.
- Integration with cryptographic attestation schemes for multi-level authentication.
- Extension to nonlinear vehicle dynamics and non-homogeneous platoons.
- Exploration of distributed voting among multiple follower vehicles exploiting network topology for redundancy.
Conclusion
The proposed multi-channel fusion and robust control framework demonstrably enhances the resilience of CACC systems to cyber-attacks on V2V channels and outperforms controller designs not accounting for communication channel vulnerabilities. This design paradigm provides a complementary strategy to traditional detection/isolation and protocol-layer defenses, and is applicable to a broad range of networked cyber-physical systems where communication-induced vulnerabilities are present.