- The paper presents Horus, a three-stage framework that detects Ethereum smart contract attacks and analyzes vulnerabilities.
- It employs dynamic taint analysis, Datalog queries, and Neo4j graph tracing, identifying 1,888 attacked contracts with 99.54% precision.
- The findings reveal persistent reentrancy attacks and exploit clustering, emphasizing the need for continuous blockchain security monitoring.
The Eye of Horus: Spotting and Analyzing Attacks on Ethereum Smart Contracts
Introduction
The paper "The Eye of Horus: Spotting and Analyzing Attacks on Ethereum Smart Contracts" provides a critical analysis of vulnerabilities and exploits within the Ethereum blockchain's smart contract ecosystem. As Ethereum's popularity has surged, so have the associated risks, primarily due to the presence of exploitable vulnerabilities in smart contracts. The authors introduce Horus, a framework designed not only to detect these attacks but also to analyze their impact and trace the flow of illicitly obtained assets.
Framework Overview
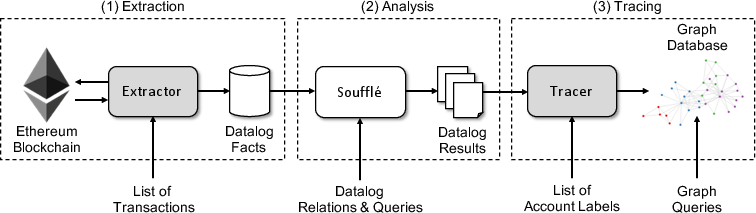
Horus operates as a three-stage pipeline consisting of extraction, analysis, and tracing. This architecture allows for a comprehensive examination of blockchain data to identify and investigate malicious activities.
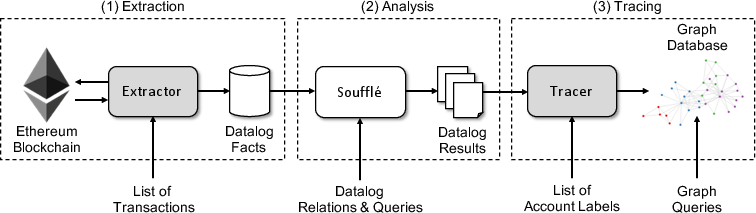
Figure 1: Architecture of Horus. Shaded boxes represent custom components, whereas boxes highlighted in white represent off-the-shelf components.
- Extraction: Utilizes the Ethereum client to replay transactions and capture execution traces, which are then converted into Datalog facts that represent transaction semantics. This stage incorporates dynamic taint analysis to monitor data flow across transactions.
- Analysis: Employs a Datalog engine to apply queries that detect specific vulnerabilities, such as reentrancy and integer overflows. This step provides a robust method to identify adversarial transactions from historical data.
(Tables and Listings omitted for brevity)
- Tracing: Focuses on following the trail of stolen assets using Neo4j graph databases. This stage assesses the movement of funds between accounts, providing insights into the attackers' strategies and financial maneuvers.
Evaluation and Validation
The framework's evaluation demonstrates its scalability and precision through the analysis of Ethereum's complete transaction history up to May 2020. Detection was validated against existing tools and research, revealing 1,888 attacked contracts and 8,095 adversarial transactions, with a precision rate of 99.54%.
Key Findings
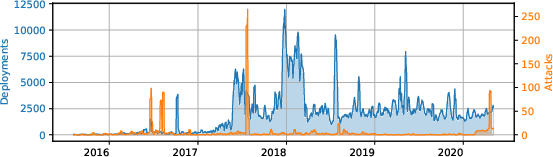
- Vulnerability Trends: The analysis indicated that while certain attack types like integer overflows have decreased, others such as reentrancy attacks persist despite available security tools.
- Attack Clustering: Attacks often occur in clusters, suggesting systematic exploitation following vulnerability discovery.
- Impactful Incidents: Analysis of high-profile incidents, such as the Uniswap and Lendf.me attacks, highlights the framework's capacity for forensic investigation and tracing of attack vectors and stolen asset flow.
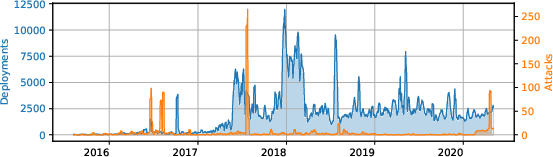
Figure 2: Weekly average of daily contract deployments and attacks over time.
Implications and Future Work
Horus provides an essential tool for conducting retrospective analysis of blockchain security, offering insights into vulnerability trends and attack methodologies. By bridging detection and asset tracing, it supports both academic research and practical security efforts. Future developments may focus on real-time monitoring and integration with proactive security measures, enhancing the framework's utility in ongoing security maintenance.
Conclusion
The paper presents Horus as an effective framework for identifying and analyzing smart contract attacks on Ethereum. Through a detailed exploration of vulnerabilities and transaction behaviors, it provides both quantitative and qualitative insights into the security landscape of smart contracts, affirming the need for continuous monitoring and analysis to mitigate risks in blockchain technologies. The findings offer a foundational platform for further research and development in blockchain security solutions.