- The paper's main contribution is a tool that synthesizes adversarial smart contracts using symbolic evaluation to accurately identify vulnerabilities.
- It leverages summary-based execution and SMT solvers to efficiently partition the search space and reduce false positives.
- Experimental results on Etherscan data demonstrated detection of 20 vulnerable contracts previously missed by other analyzers.
Detailed Summary of "Precise Attack Synthesis for Smart Contracts"
The paper "Precise Attack Synthesis for Smart Contracts" (1902.06067) presents a novel approach to detecting vulnerabilities in smart contracts by generating adversarial contracts that exploit these vulnerabilities. This approach is fundamental due to the immutable nature of smart contracts once deployed, which makes identifying potential exploits crucial before they lead to catastrophic financial losses.
Introduction to Smart Contracts and Vulnerabilities
Smart contracts are autonomous programs that operate on blockchain platforms like Ethereum, fulfilling the role of trusted intermediaries in executing transactions. Due to their immutable nature, any vulnerabilities or bugs in the code, such as reentrancy or arithmetic overflow, can be severely damaging. The paper discusses how traditional contract analysis tools either overapproximate the execution leading to false warnings, or fail to scale due to the computational complexity of precise enumeration.
Overview of Attack Synthesis
The core of the paper introduces a tool named that uses program synthesis methods to create attack contracts derived from queries specifying known vulnerabilities. By symbolically evaluating each function within the contract, it generates a summary highlighting the side effects on the storage and global blockchain state. This summary is central to scaling the analysis and narrowing down feasible attack vectors.

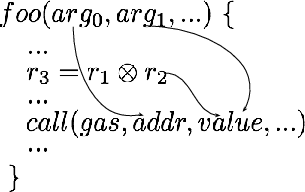
Figure 1: Overview of
The tool partitions the search space of potential attack strategies using symbolic execution and summary-based evaluation. By subdividing paths using SMT solvers, potential candidates are pruned early, amplifying efficiency. This approach, combined with parallel execution, allows the system to systematically evaluate attacks across a vast space with minimal false positives.
Implementation and Key Techniques
The paper describes the system implemented in Rosette, leveraging symbolic evaluation, summary-based execution, and state transition rules tailored for efficient symbolic evaluation. Furthermore, it discusses parallel synthesis through methodical search space partitioning based on query structure and the summary of symbolically evaluated methods.
Evaluation and Results
Evaluation of the system was conducted on a large dataset from Etherscan, with a spectrum of vulnerabilities such as BatchOverflow and Reentrancy analyzed. The system showcased expressiveness across various known vulnerabilities, effectiveness in outperforming existing smart contract analyzers, and efficiency, substantially reducing analysis time.
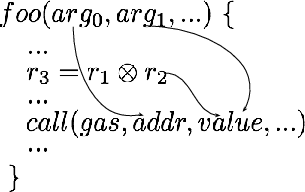
Figure 2: The key pattern of the BatchOverflow Vulnerability
The results demonstrated that discovered vulnerabilities in 20 contracts that existing tools could not detect, proving the robustness of the synthesis method. Furthermore, its efficiency was highlighted with a significant reduction in false positives and negatives compared to other tools, such as Oyente and ContractFuzzer.
Conclusion
The paper presents a compelling advancement in smart contract security analysis, emphasizing precision through attack synthesis rather than typical vulnerability detection strategies. Future work could expand the approach to address denial-of-service vulnerabilities and integrate relational synthesis for complex exploit scenarios requiring multiple interacting contracts.
Implications and Future Directions
The ability to automatically generate adversarial smart contracts has substantial implications for blockchain security. It advances towards proactive vulnerability management, where potential exploits are anticipated and mitigated before deployment. Anticipated future directions could explore more comprehensive vulnerability query languages and adaptive synthesis methodologies tailored for emerging blockchain paradigms.
Overall, this research fosters a vital discussion on balancing expressiveness, efficiency, and scalability in smart contract analysis tools, essential for safeguarding decentralized finance ecosystems.