- The paper systematically evaluates three major Android messaging apps, highlighting differences in permission requests, attack surfaces, and dependency usage through static analysis.
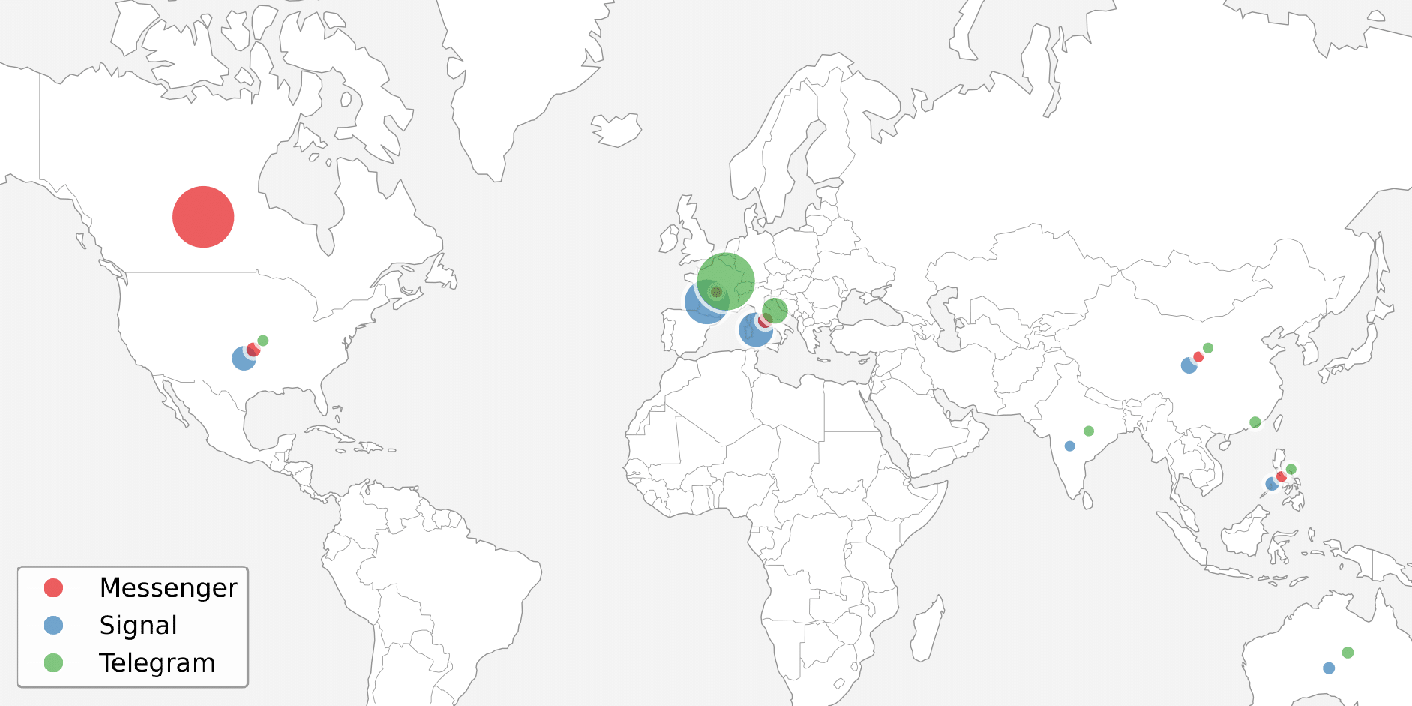
- It employs dynamic analysis with kernel-level tracing to map network behaviors and geographic endpoint distributions, revealing varied data flows among Messenger, Signal, and Telegram.
- The study underscores the need for minimizing permissions and dependencies in app design to reduce security risks, providing actionable insights for practitioners and regulators.
Empirical Evaluation of Security and Privacy in Android Messaging Applications
Methodology Overview
The paper “An Empirical Comparison of Security and Privacy Characteristics of Android Messaging Apps” (2603.29668) systematically evaluates three major Android messaging applications—Meta Messenger, Signal, and Telegram—through static and dynamic analysis. The study employs programmatic dissection of official APKs and low-level kernel tracing (tcpdump, ftrace, SliceDroid), targeting key S&P-relevant facets: permission requests and compliance, attack surface exposure via exported components, application/network complexity, external dependency presence, and real-world network behavior. Network endpoints are further resolved and visualized for geographic analysis.
The design prioritizes reproducibility, with testbed configurations and behavioral scenarios (foreground/background, full/restricted permissions) thoroughly documented. Statistical approaches (Kruskal-Wallis H, post-hoc Mann-Whitney with Bonferroni correction) underpin all activity data analysis to ensure rigor in the face of observed runtime variability.
Comparative Static Analysis
Divergence is pronounced across metrics characterizing application complexity and potential attack surface:
- Messenger: Exhibits the largest attack surface, integrating 107k Java classes and nearly half a million methods; exports the highest number of services, receivers, and providers. Requests the highest number of total permissions (87), including 24 categorized as “dangerous.” Integrates multiple external SDKs (e.g., Google Analytics, Mapbox), resulting in 118 MobSF static analysis warnings (notably, 101 medium-severity, 9 high-severity).
- Signal: Demonstrates minimalist architecture and strong privacy alignment. With a comparatively minimal codebase (55k classes/361k methods), it exports only a limited set of components and dependencies. It requests just 72 permissions, with 19 dangerous. Static warning count is also lowest (55). Notably, Signal omits phone-call control and overlay permissions, and does not employ third-party analytics or trackers.
- Telegram: Occupies a middle ground, with less code and fewer exports than Messenger, but more than Signal. It requests the fewest permissions overall (71), yet has the highest count of dangerous permissions (25). Telegram uniquely allows global cleartext network traffic, exposing it to traffic interception risks absent in Signal and Messenger.
The static evaluation reveals Telegram and Messenger adopting broader privilege and exposure models, subsequently increasing their potential S&P risk relative to the more constrained, dependency-minimal Signal.
Dynamic Analysis Results
Real-world behavior, as assessed via kernel-level tracing and network flow mapping, unearthed critical discrepancies in network activity, endpoint distribution, and resource access:
All assessed applications adhered to the Android permission model under dynamic tests, with no unauthorized resource accesses observed. Anomalous resource access flagged in Messenger related to benign provider-local maintenance rather than actual privacy violation, as confirmed by comprehensive hook tracing and log inspection.
Implications for Security and Privacy Engineering
These results reinforce the necessity for holistic audit approaches—pure protocol cryptography assurance is insufficient. Application-level complexities, extensive permission requests, and broad component exposure significantly modulate the real-world S&P posture. Concretely:
- Broad attack surface and dependency integration (Messenger): Increases systemic risk and the likelihood of exploitable flaws. Copious permission requests and external SDKs may expose endpoints to third-party data extraction and profiling, counter to user privacy expectations.
- Leaner, dependency-minimal implementations (Signal): Enhance transparency, reduce external risk surfaces, and facilitate accountability. Minimal permission grants align with least-privilege principles.
- Permissive network configurations (Telegram): Allowing global cleartext traffic introduces passive and active threats that are easily mitigated with correct network configuration.
For practitioners, these findings strongly advocate for minimized permission grants, restricted interface exports, excluding unnecessary third-party code, and rigorous static/dynamic code analysis as standard development practices. For users and regulators, detailed app-level behavioral analysis provides an actionable basis for app selection or risk-based policy enforcement.
Theoretical and Practical Impact, and Prospective Work
The hybrid methodology—combining static and dynamic program analysis at kernel granularity—provides a robust template for evaluating a wider class of mobile IM clients, or indeed other high-value app categories. As Android app ecosystems diversify, this approach can inform market-wide audits, regulatory compliance, and automated app assessment. Future development includes:
- Scaling to larger app populations with automated endpoint profiling
- Integrating behavioral anomaly detection (e.g., via application-level DTLS/SRTP fingerprinting)
- Cross-platform analyses encompassing iOS implementations
- Evaluating end-to-end correlation between resource access, cryptographic assurance, and backend data retention
Further, the geographic analysis of network flows highlights the implications of regional data residency and cross-border flows, intersecting both S&P and current legal compliance landscapes (e.g., GDPR, data localization).
Conclusion
The study demonstrates significant implementation-level heterogeneity among widely deployed Android messengers, with direct implications for user security and privacy. Messenger manifests the broadest attack surface, most excessive permission requests, and highest indicator count for static risks. Telegram exposes users via permissive network configuration and elevated dangerous-permission requests. Signal remains distinctive for its restrictive design, achieving a minimized network and code footprint. The hybrid audit methodology is extensible, providing a generalizable framework for security and privacy characterization in mobile ecosystems.