- The paper introduces hardware/software obfuscation techniques to mitigate timing side-channel attacks on GPUs by randomizing memory access patterns.
- It employs hardware randomization in the coalescing unit and modifications to MSHRs to disrupt the correlation between execution time and memory transactions.
- The integration of lookup table hashing in software, validated by simulation, demonstrates a significant reduction in vulnerabilities during cryptographic operations.
Overview of Hardware/Software Obfuscation Techniques Against GPU Timing Side-channel Attacks
The paper "Hardware/Software Obfuscation against Timing Side-channel Attack on a GPU" (2007.16175) addresses the inherent vulnerabilities of GPUs to timing side-channel attacks, particularly within the domain of cryptographic computations. The research examines novel hardware and software countermeasures to mitigate the risk posed by these attacks, which exploit the relationship between execution time and memory access patterns to infer encryption keys.
GPU Vulnerabilities and Timing Attacks
GPUs are increasingly utilized for a range of compute-intensive tasks, including cryptographic operations due to their high throughput capabilities. Despite their efficiency, GPUs are vulnerable to side-channel attacks that rely on the timing of memory accesses to extract sensitive information, such as encryption keys. This vulnerability is exacerbated by the fact that attackers can exploit the predictable patterns of memory transactions in GPU architectures.
Proposed Countermeasures
Hardware Randomization Techniques
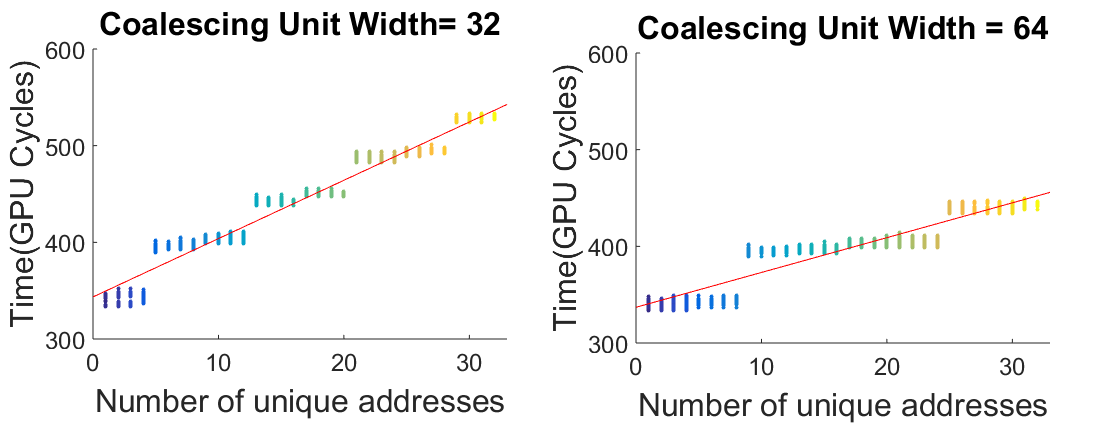
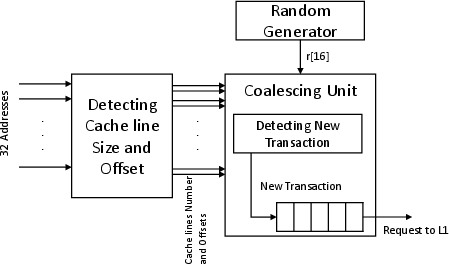
Central to the proposed approach is the introduction of randomness in the GPU's coalescing unit, which aggregates multiple memory requests from threads into single transactions. By randomizing the width of the coalescing unit, the paper aims to decorrelate the execution time from the memory access pattern, thereby increasing noise in the timing signal perceived by potential attackers. The use of varying transaction sizes across different streaming multiprocessors (SMs) further amplifies the noise, complicating any attempt to deduce encryption keys.
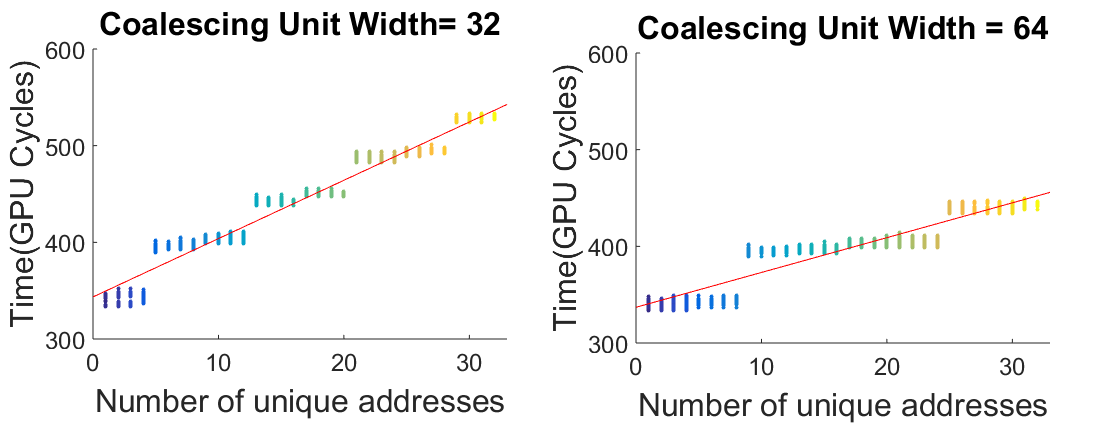
Figure 1: Execution time of accessing 1 to 32 unique address with different width of coalescing unit.
Additionally, modifications to the Miss Status Holding Registers (MSHRs) add both noise and performance improvements by enabling cross-SM miss tracking. This dual-function enhancement not only obfuscates the memory access patterns but may also enhance overall memory management efficiency.
Software-based Obfuscation
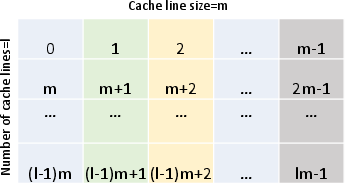
In conjunction with hardware changes, a software-based lookup table hashing methodology is introduced. This strategy aims to obscure the access pattern to lookup tables employed during cryptographic operations, thereby thwarting attempts by attackers to infer transaction numbers from execution timing.
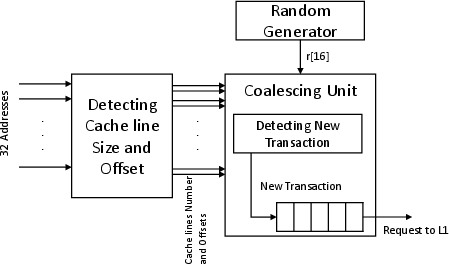
Figure 2: Redesign Coalescing Unit for Dynamic Random Width.
Experimental Validation
The effectiveness of these countermeasures is evaluated using an execution-driven GPU simulator, which allows for testing various configurations under controlled conditions. The results indicate a significant reduction in the effectiveness of timing side-channel attacks, attributable to the increased noise in memory access times.
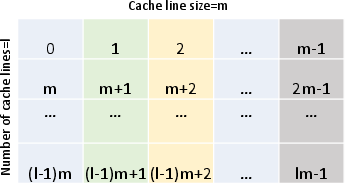
Figure 3: General structure of a lookup table with size n=ml in cache, where the cache line can hold m elements.
Implications and Future Directions
This research offers a comprehensive approach to enhancing the security of GPUs against timing side-channel attacks without severely compromising performance. The implications for practical security are profound, as these methods can be implemented in existing GPU architectures with minimal disruption. Looking forward, further research could investigate the integration of machine learning techniques to dynamically optimize the randomization strategies based on real-time analysis of memory access patterns and attack attempts.
Conclusion
This paper provides a robust framework for safeguarding GPU computations against timing side-channel attacks through an innovative combination of hardware and software obfuscation techniques. By interjecting randomness into critical GPU functionalities, the researchers effectively weaken attackers' ability to extract sensitive information. These developments not only fortify the security of cryptographic computations but also hold potential for broader applications across various domains leveraging GPU capabilities.