- The paper introduces an automated system that simplifies SCADA firewall configuration using high-level abstractions and formal verification.
- It employs a layered, rigorously tested methodology to transform high-level policies into concise, vendor-specific configurations.
- The approach reduces configuration complexity and eliminates misconfigurations, ensuring compliance with industry best practices in critical networks.
ForestFirewalls: Automated, Correct Firewall Configuration for Critical SCADA Networks
The "ForestFirewalls" technical report (1902.05689) presents a comprehensive system for automating the configuration of firewalls in Supervisory Control and Data Acquisition (SCADA) networks. The work addresses the acute challenges of manual firewall configuration in critical infrastructure, where misconfigurations can have severe safety and financial consequences. The system leverages high-level abstractions, formal verification, and automated testing to ensure correctness, efficiency, and compliance with industry best practices.
Motivation and Problem Statement
SCADA networks underpin critical infrastructure such as power generation and water distribution. These environments are characterized by legacy devices with limited security capabilities, long upgrade cycles, and a high cost of failure. Manual firewall configuration in such settings is error-prone, complex, and often performed by personnel lacking deep networking expertise. Existing vendor tools and abstractions (e.g., Cisco security levels, Firmato) fail to provide topology-independent, high-level policy specification or robust verification mechanisms.
The ForestFirewalls system is designed to:
- Decouple security policy design from low-level implementation details.
- Simplify policy specification using high-level, vendor-neutral abstractions.
- Provide automated, multi-stage verification and validation of firewall configurations, both pre- and post-deployment.
System Architecture and Workflow
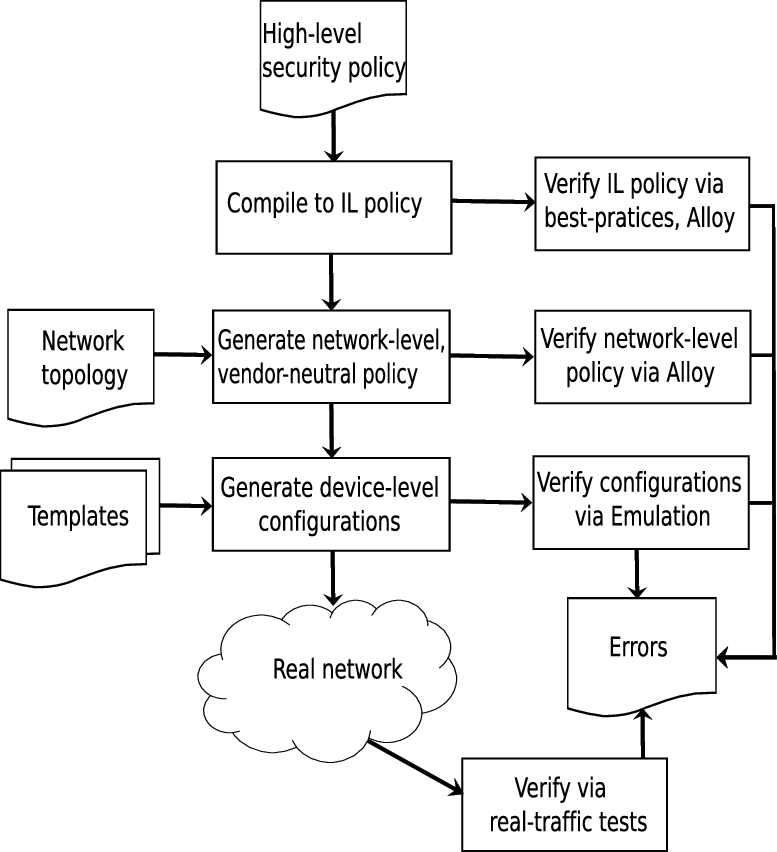
ForestFirewalls introduces a layered, automated pipeline for firewall configuration, depicted in the following process:
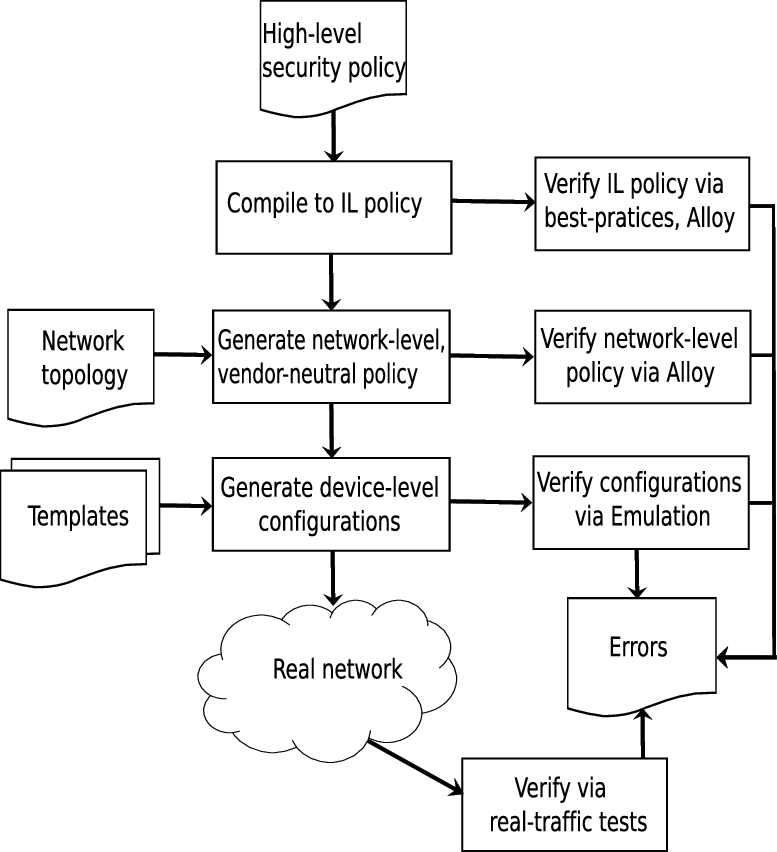
Figure 1: The ForestFirewalls firewall auto-configuration process, from high-level policy to device-specific configuration and verification.
The workflow consists of:
- High-Level Policy Specification: Users define security policies using a domain-specific language, abstracted from network topology and device specifics.
- Intermediate-Level (IL) Policy Generation: The high-level policy is parsed into an intermediate representation for formal analysis.
- Network Topology Coupling: The policy is mapped onto the actual network topology, described in GraphML, to generate a network-level, vendor-neutral policy.
- Formal Verification: Policies are checked for best-practice compliance and internal consistency using canonicalization and the Alloy model checker.
- Device-Level Configuration Generation: Vendor-specific configurations are rendered using templates.
- Automated Testing: Configurations are validated in emulated and real environments using automated test scripts and traffic generation.
Security Abstractions: The Refined Zone-Conduit Model
A central innovation is the use of a refined Zone-Conduit abstraction, based on but extending the ANSI/ISA model. In this model:
- Zones group systems with similar security requirements.
- Conduits represent secure communication paths between zones, abstracting the enforcement mechanism (e.g., firewalls).
ForestFirewalls enforces a strict 1:1 mapping between policies and conduits, introduces Firewall-Zones and Abstract-Zones for management and serial firewall requirements, and prohibits sub-zones to avoid policy ambiguity. This results in a tight, automatable specification suitable for high-assurance environments.
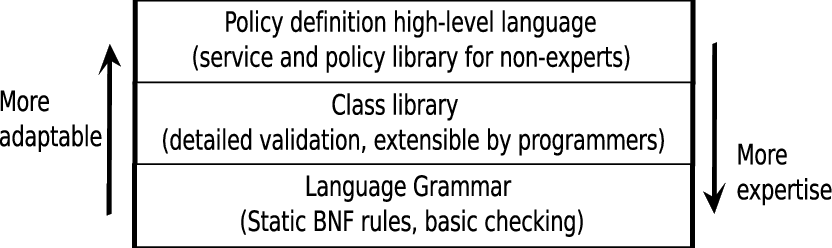
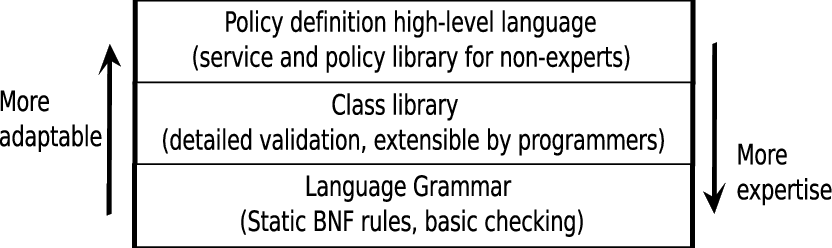
Figure 2: Policy specification in layers, supporting both non-expert and expert users through high-level language, class libraries, and grammar rules.
Policy Specification Framework
The policy specification framework is layered to support both non-expert users (e.g., plant engineers) and expert programmers:
- High-Level Language: Intuitive syntax for defining services, service groups, zones, and policy rules. Only positive, explicit permissions are allowed; implicit or generic rules (e.g., all-TCP) are prohibited.
- Class Library Layer: Object-oriented classes for protocol and service construction, with attribute validation.
- Grammar Layer: BNF rules enforce language semantics and delegate detailed checks to the class library.
This approach enables concise, readable, and maintainable policy definitions. For example, a policy that would require 2720 lines of device-level configuration can be specified in only 80 high-level lines.
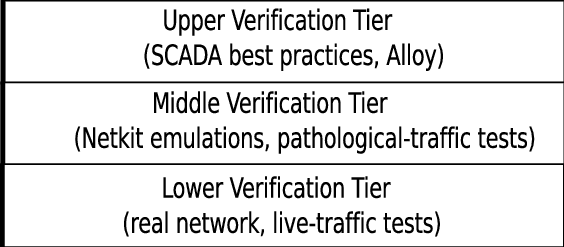
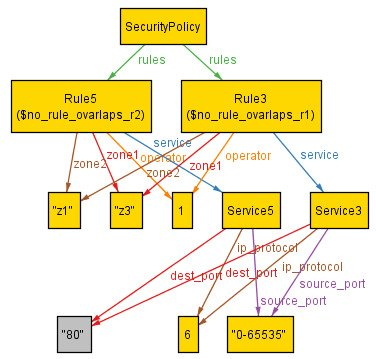
ForestFirewalls employs a multi-tiered verification strategy:
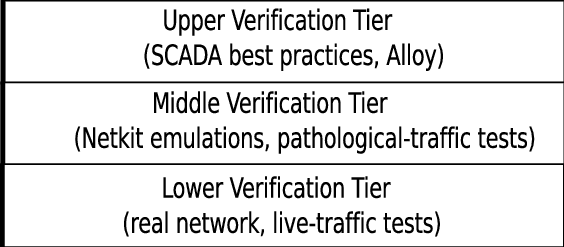
Figure 3: Policy verification tiers, including best-practice compliance, emulation-based testing, and live network validation.
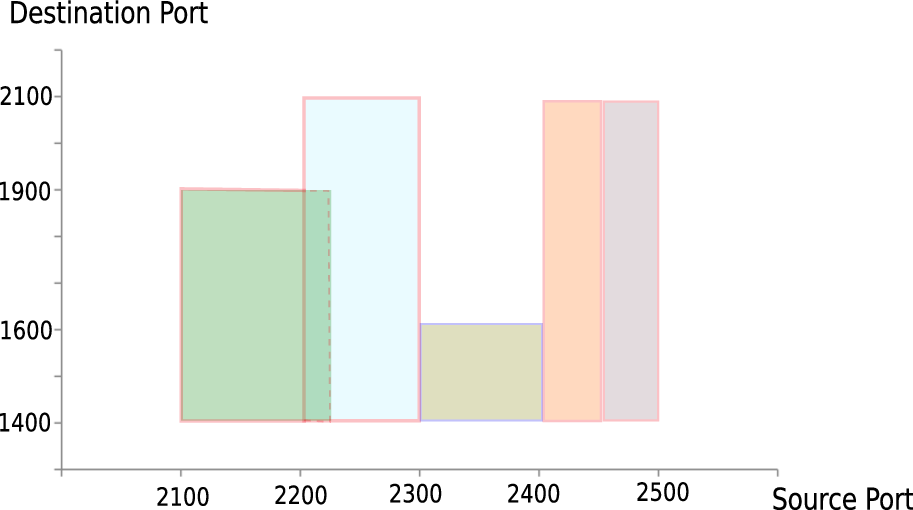
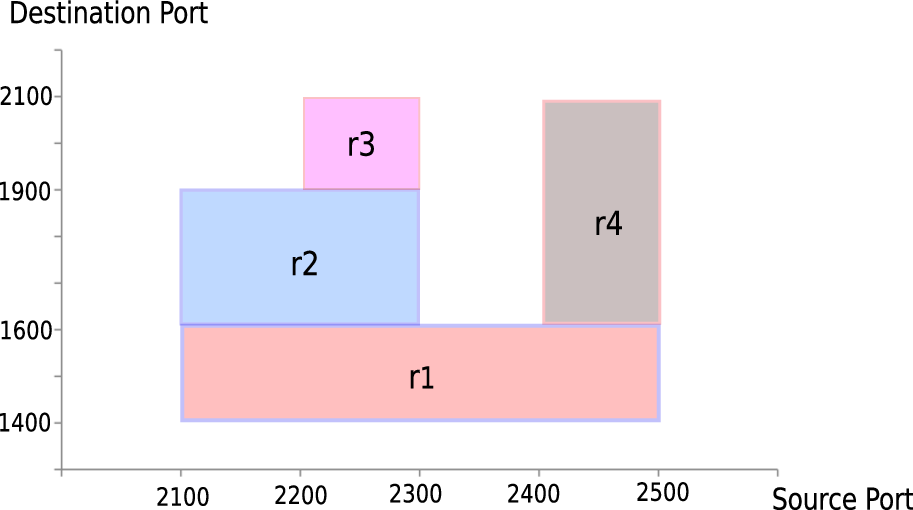
- Best-Practice Compliance: Policies are canonicalized—distinct rule sets with equivalent semantics are mapped to a unique representation—enabling efficient equivalence and inclusion checks against industry standards.
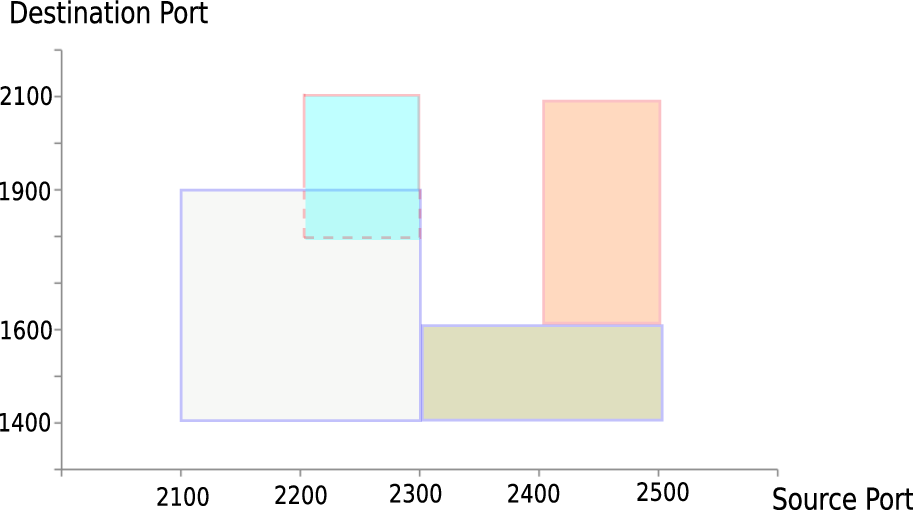
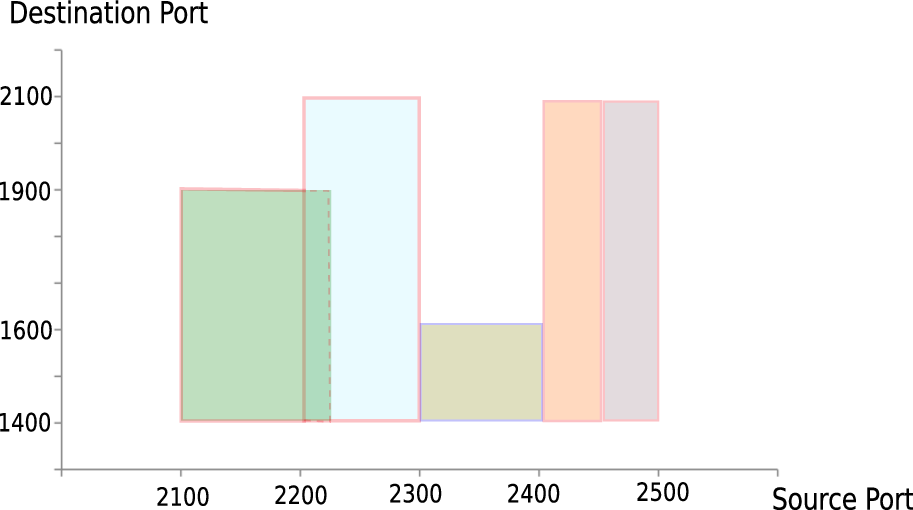
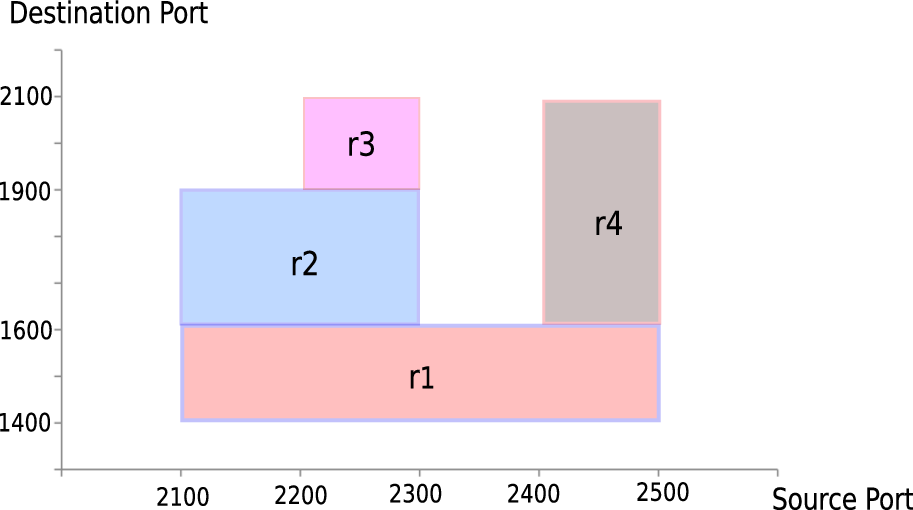
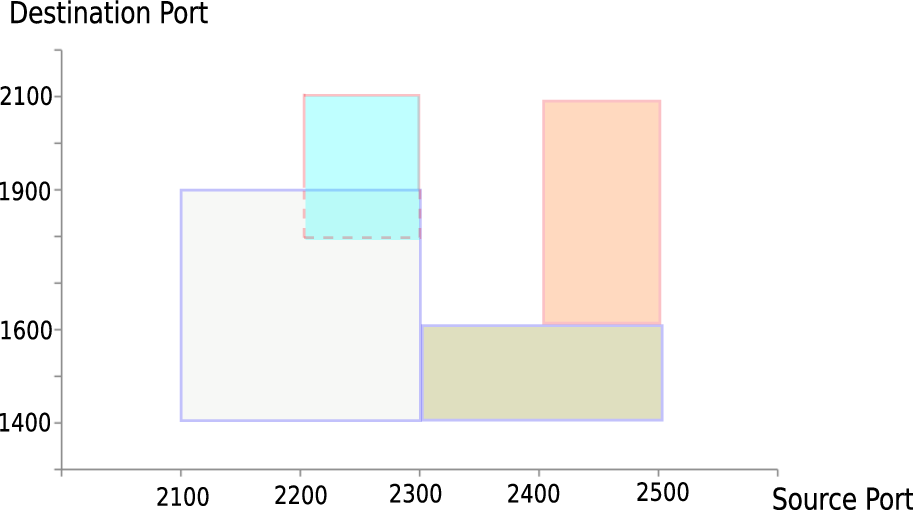
Figure 4: Canonicalisation of distinct rule sets of the same policy, ensuring semantic equivalence despite syntactic differences.
Application to Real SCADA Networks
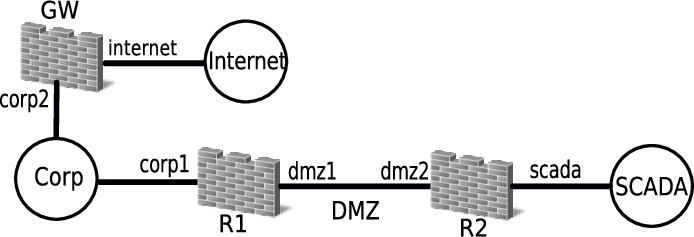
The system was evaluated on a real (anonymized) SCADA network comprising multiple zones and heterogeneous firewalls (Cisco ASA and Linux IPtables). The policy goals included strict inter-zone access controls, defense-in-depth via diverse firewall vendors, and comprehensive reporting.
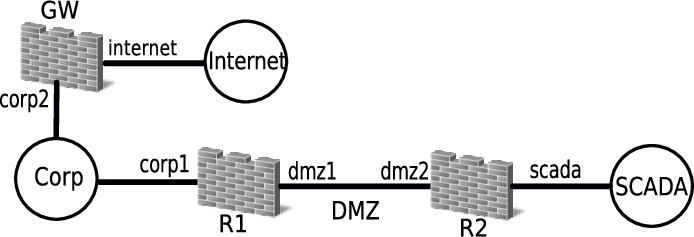
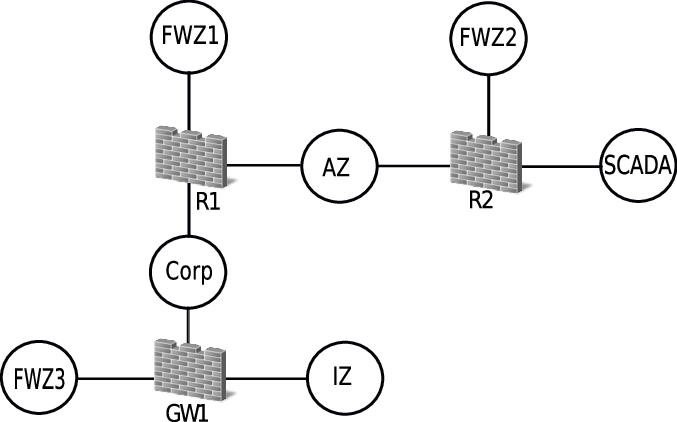
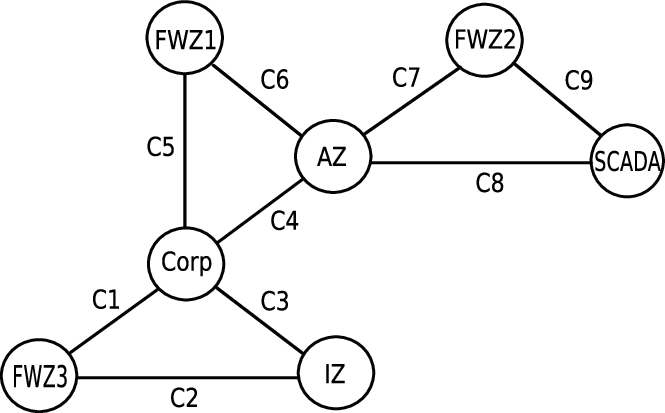
Figure 6: The SCADA network under study, illustrating the segmentation and firewall placement.
ForestFirewalls generated device-level configurations that were:
- Order-of-magnitude more concise: 714 lines vs. 2720 lines in the original manual configuration.
- Free of generic or implicit rules: No all-TCP, all-UDP, or all-IP rules; all permissions are explicit.
- Efficient and non-redundant: No obsolete ACLs or intra-ACL interactions.
- Formally verified: No rule overlaps or best-practice violations after correction of initial errors detected by Alloy.
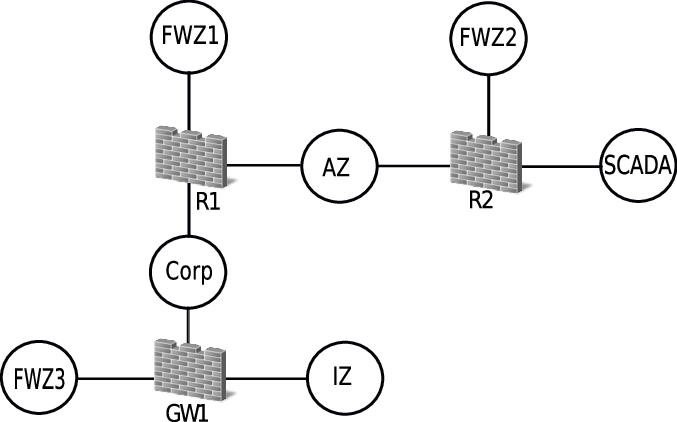
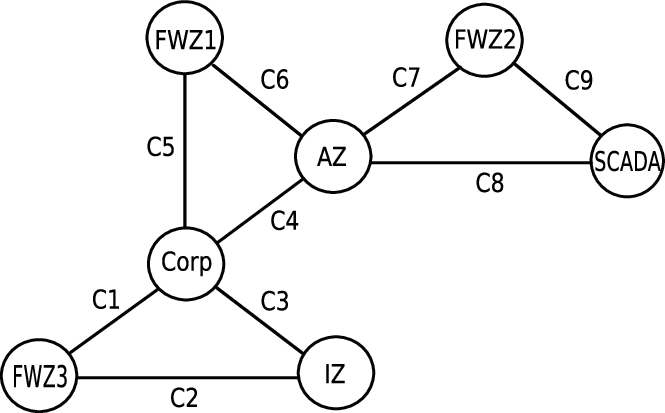
Figure 7: System generated security models of the network, including Zone-Firewall and Zone-Conduit representations.
Implications and Future Directions
ForestFirewalls demonstrates that high-level, formally verified, and automated firewall configuration is feasible and effective for critical infrastructure. The approach yields significant reductions in configuration complexity, eliminates common classes of misconfiguration, and provides strong guarantees of policy correctness and compliance.
Practical implications include:
- Enabling non-expert personnel to manage firewall policies safely.
- Rapid adaptation to network changes without compromising security.
- Scalable configuration and verification for large, heterogeneous environments.
Theoretical implications involve the formalization of policy semantics, the use of canonicalization for efficient policy comparison, and the application of model checking to configuration validation.
Future work may extend the system to:
- Automate deployment to hardware devices.
- Integrate with SDN controllers for dynamic policy enforcement.
- Expand the reporting framework for real-time monitoring and incident response.
- Generalize the approach to other types of security middleboxes.
Conclusion
ForestFirewalls provides a robust, automated solution to the persistent problem of firewall misconfiguration in SCADA and other critical networks. By combining high-level abstractions, formal verification, and automated testing, the system achieves correctness, efficiency, and compliance unattainable with manual or vendor-specific tools. The methodology and architecture presented are broadly applicable to the secure management of complex, heterogeneous networked systems.