- The paper presents a large-scale analysis using 4.5 million samples over 12 years to reveal trends in crypto-mining malware.
- The study uncovers sophisticated use of obfuscation, third-party cloud services, and botnets to bolster illicit mining campaigns.
- The paper estimates that major campaigns generated multimillion-dollar profits with 4.4% of Monero's supply mined through malware.
Overview of "A First Look at the Crypto-Mining Malware Ecosystem: A Decade of Unrestricted Wealth"
The paper offers a comprehensive analysis of the crypto-mining malware ecosystem, focusing on the mining of cryptocurrencies like Monero by malicious actors. The authors conduct a large-scale measurement of crypto-mining malware, analyzing 4.5 million samples across twelve years from static and dynamic perspectives. This analysis reveals significant findings on malware campaigns, infrastructure, and profits accrued by this illicit activity.
Measurement Methodology
The authors devised an extensive methodology to collect and analyze malware samples. They aggregated data from multiple sources such as Virus Total and Palo Alto Networks, which helped them identify 1.2 million miner samples. Dynamic and static analyses were conducted to extract relevant attributes like wallet identifiers and mining pools, supported by Open Source Intelligence (OSINT) data. This comprehensive approach allowed the authors to categorize malware into identifiable campaigns using a graph-based system.
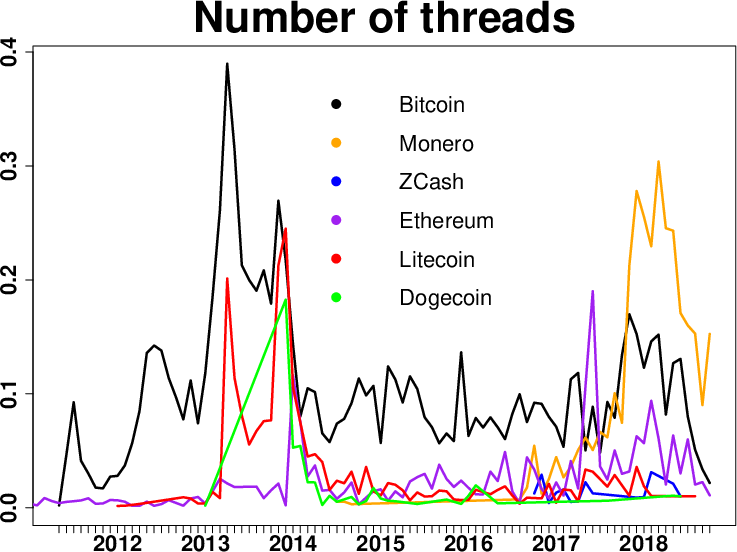
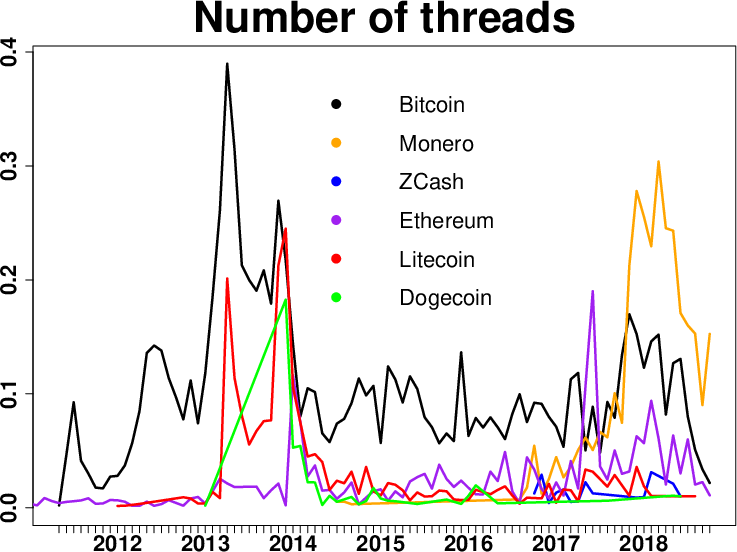
Figure 1: Evolution of the number of threads from underground forums related to mining of different cryptocurrencies.
Infrastructure and Campaign Analysis
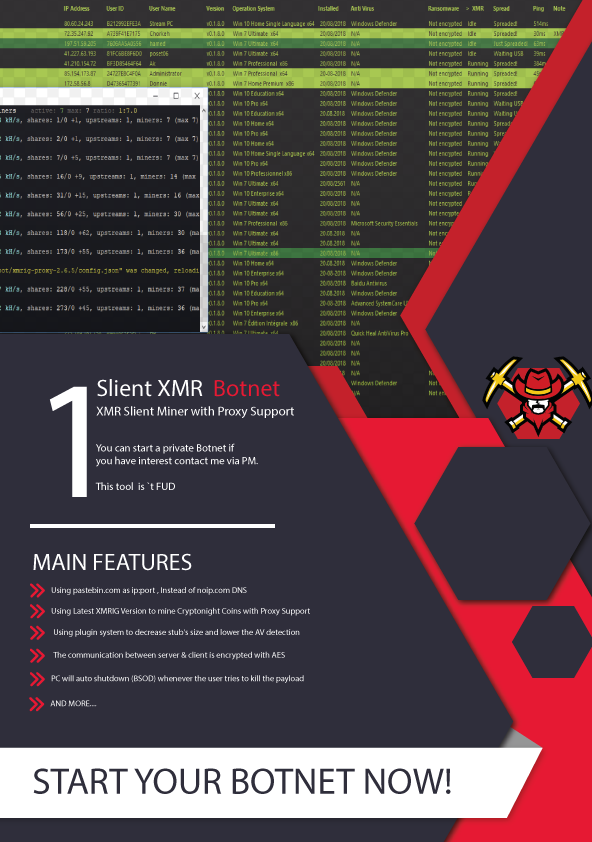
The study excavated the infrastructure underlying these illicit mining campaigns, including the use of third-party cloud services and botnets as Pay-Per-Install (PPI) services. The authors noted significant criminal reliance on these underground services to bolster campaign efficacy. They detailed the use of mining software like xmrig and claymore, revealing its prevalence in malicious mining activities. Additionally, obfuscation techniques were identified, such as the usage of packers to conceal malware.
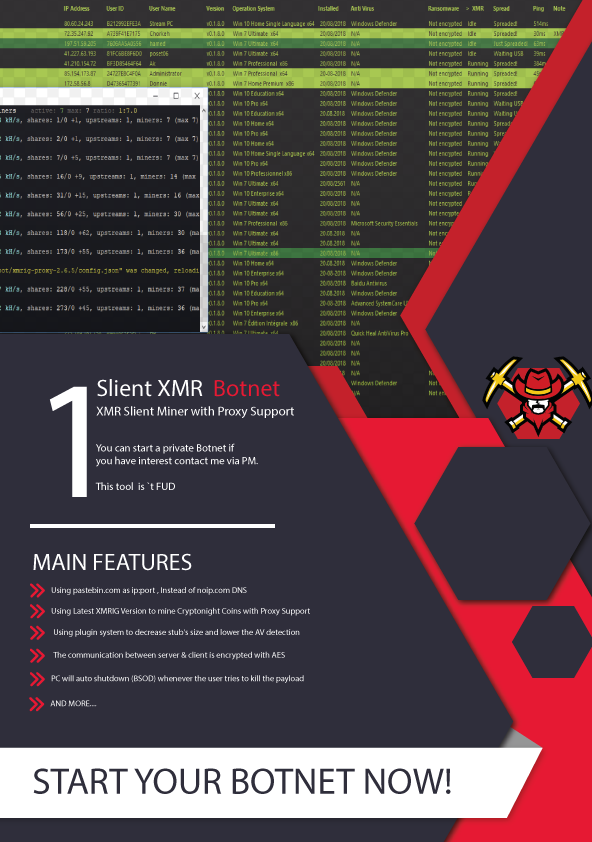
Figure 2: Crypto-mining package offered in an underground forum, including botnet setup, XMR miner and proxy. Permanent link: {https://perma.cc/4FN8-B98M}
Profit Estimation and Pool Usage
By querying mining pool data, the authors estimated profits and found that a small group of campaigns dominates the ecosystem with multimillion-dollar gains. Particularly, Monero emerged as the commonly mined cryptocurrency, with a calculated 4.4% circulating supply attributed to malicious mining. The study identified prevalent mining pools used by these campaigns, highlighting the non-cooperative stance of certain pools, which complicated the tracking and disabling of illicit mining operations.
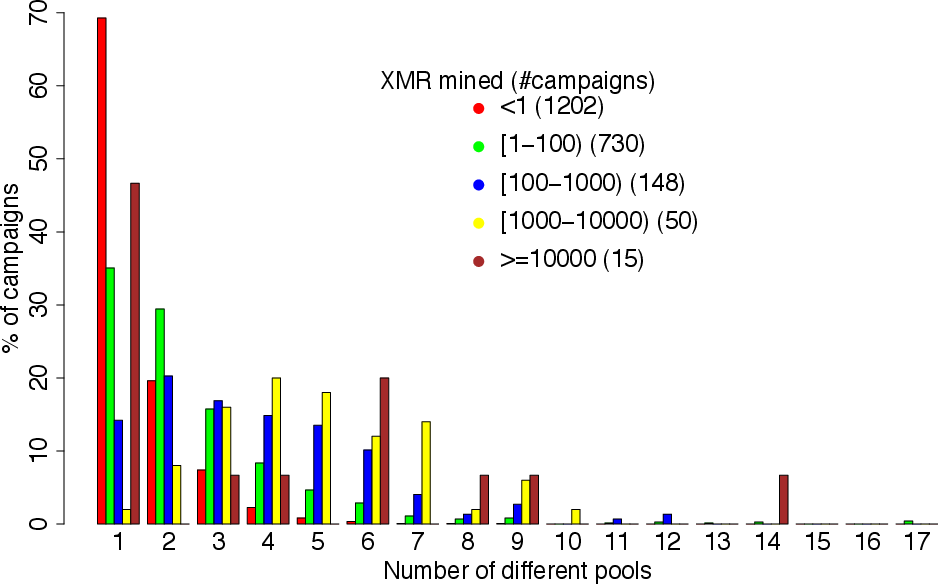
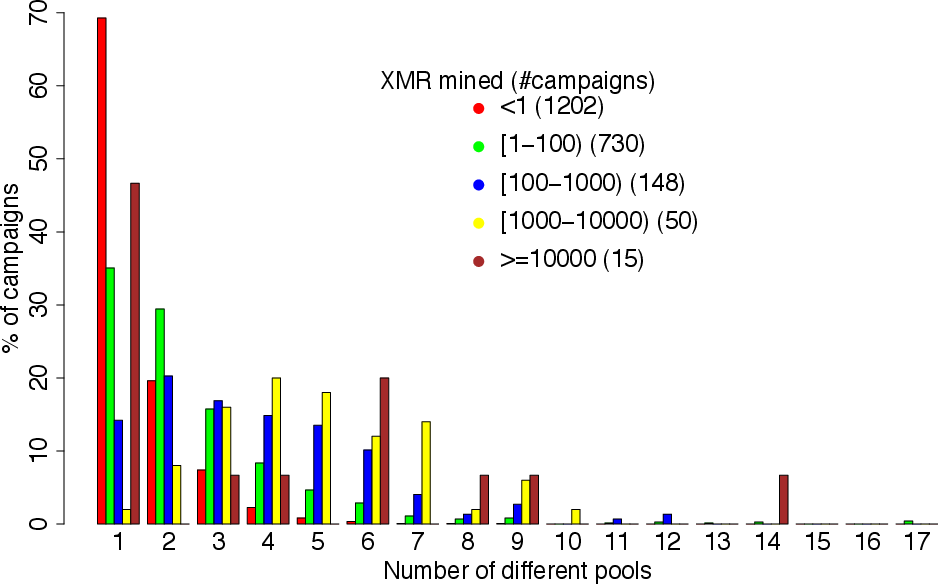
Figure 3: Number of different mining pools used by the campaigns grouped by earnings.
Countermeasures and Challenges
The authors discussed the limited impact of current countermeasures against mining malware due to evasion tactics like proxies and obfuscation. They critiqued the inefficacy of reporting illicit wallets alone and suggested that frequent changes in the cryptocurrency Proof-of-Work (PoW) algorithms could act as a deterrent. Moreover, they postulated that holistic, cooperative approaches encompassing legal frameworks for pool regulation and technical measures enhancing detection accuracy are required.
Conclusion
This paper elucidates the large-scale impact and operational complexity of the crypto-mining malware ecosystem. By uncovering the symbiosis between underground economies and malware campaigns, the authors underscore the pressing need for more effective intervention strategies. Their elucidation of the ecosystem serves as a foundation for future research and development of robust countermeasures against this illicit activity.
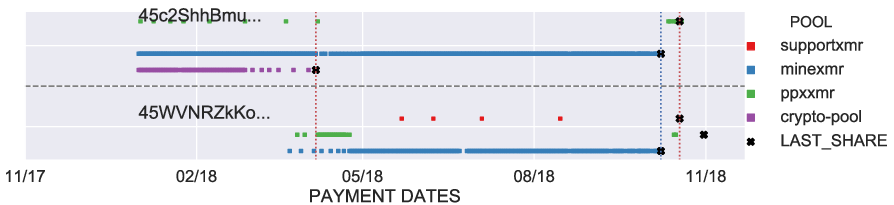
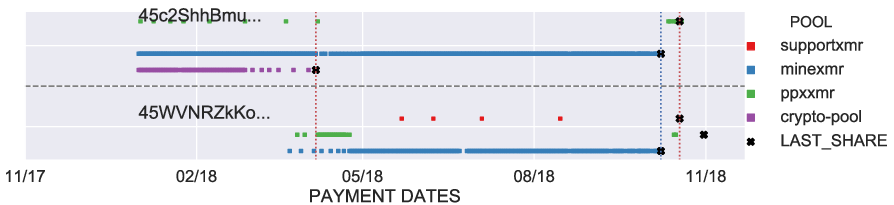
Figure 4: Detailed view of the wallets banned in the Freebuf campaign. Blue vertical line shows when the wallets were banned.