- The paper presents a framework that links AI agents to human operators using cryptographic signatures and verifiable delegation credentials.
- It extends OAuth 2.0 and OpenID Connect to integrate AI agent permissions, enabling secure and auditable delegated actions.
- The study highlights the importance of clear legal frameworks and structured access control to maintain accountability in AI task delegation.
Authenticated Delegation and Authorized AI Agents
The paper "Authenticated Delegation and Authorized AI Agents" (2501.09674) introduces a framework addressing the growing necessity for secure, auditable, and authorized interactions between autonomous AI agents and digital services. The primary aim is to facilitate task delegation to AI agents while ensuring trust, security, and accountability.
Introduction to Authenticated Delegation
The emergence and deployment of agentic AI systems—capable of performing complex tasks on behalf of users—pose significant challenges related to authorization, accountability, and access control. AI agents need to perform actions such as booking travel, interacting with online services, and more complex negotiations, often with minimal human intervention. This requires robust systems that not only allow these delegated tasks but also firmly establish the identity and authority of the AI systems involved.
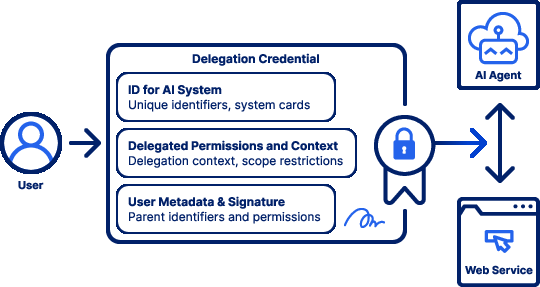
Authenticated delegation seeks to address these challenges by securely linking AI agents to their human operators through digital credentials that cover unique identity, delegated permissions, and contextual scopes. It proposes utilizing cryptographic signatures to create verifiable credentials for AI agents, ensuring they operate only within authorized boundaries.
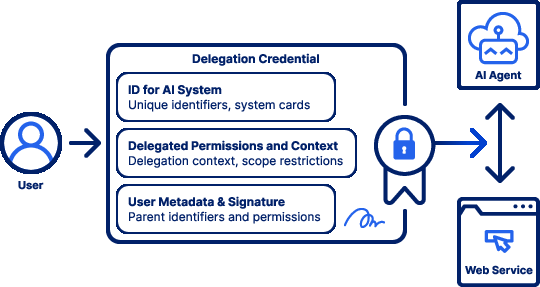
Figure 1: Conceptual overview of a verifiable delegation credential for AI agents.
Extending OAuth 2.0 and OpenID Connect
The paper proposes leveraging existing protocols such as OAuth 2.0 and OpenID Connect to extend functionality specifically for AI agents. By doing so, the proposal integrates seamlessly with the current web infrastructure, facilitating broad adoption with minimal disruption.
Key Components
- User's ID-token: Represents the human user issuing the delegation.
- Agent-ID Token: Details pertaining to the AI agent, such as capabilities and unique identifiers.
- Delegation Token: Explicit authorization for the AI agent, specifying the scope of actions it may perform on the user’s behalf.
These components help maintain accountability and transparency by ensuring all actions performed by AI agents are auditable and securely linked back to their human originators.
Defining Scope and Permissions
Setting boundaries for what AI agents are allowed to do (task scoping) and what resources they can access (resource scoping) are paramount. The paper emphasizes converting flexible, natural language instructions into structured access control configurations. These include machine-readable rules that govern agent actions across different modalities (e.g., web, APIs).
Integration with Existing Systems
By building upon existing systems, authenticated delegation can be implemented without overhauling current infrastructures. As a result, digital service providers can more readily adopt these methods, allowing AI agents to interact without jeopardizing current security protocols.
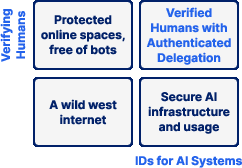
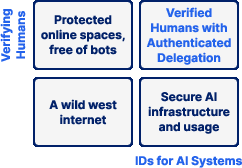
Figure 2: Authenticated delegation can benefit from user identification or verification of personhood.
Legal and Ethical Considerations
The paper also touches on the importance of clear legal frameworks to ensure accountability in AI agent interactions. It suggests that authenticated delegation mechanisms can align with existing legal standards and enhance trust in agent-mediated transactions by providing legally verifiable trails of actions performed by AI agents.
Conclusion
Authenticated delegation, as proposed in the paper, seeks to address several core challenges associated with AI agent deployment in digital ecosystems. By extending existing, well-established protocols, it offers a pragmatic approach to securely manage AI interactions, striking a balance between innovative AI capabilities and the essential need for accountability and security. This framework lays the groundwork for broader adoption and safer integration of AI assistants in various sectors. Implementing these systems facilitates an environment where AI-driven task automation can thrive securely and accountably.