CRPWarner: Warning the Risk of Contract-related Rug Pull in DeFi Smart Contracts
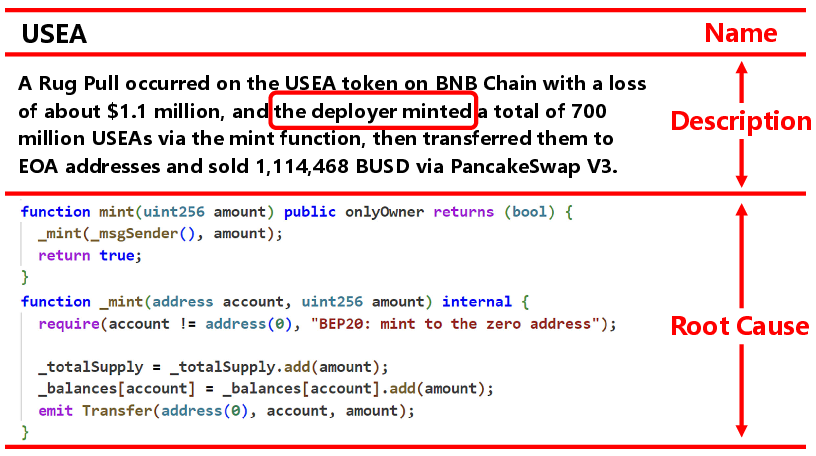
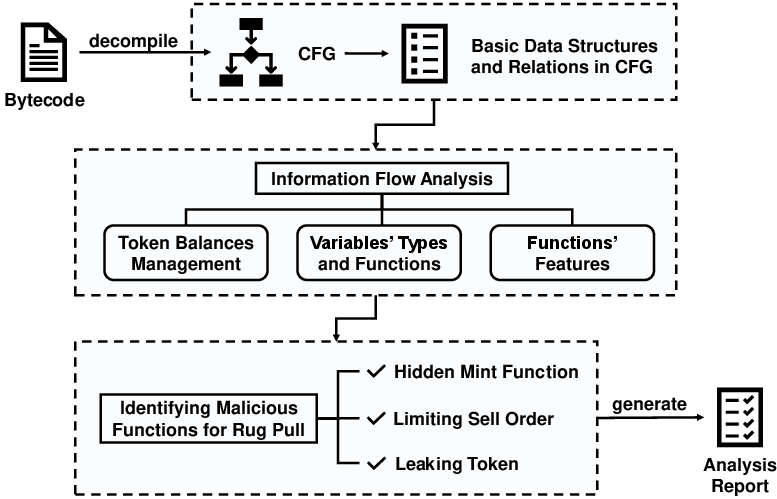
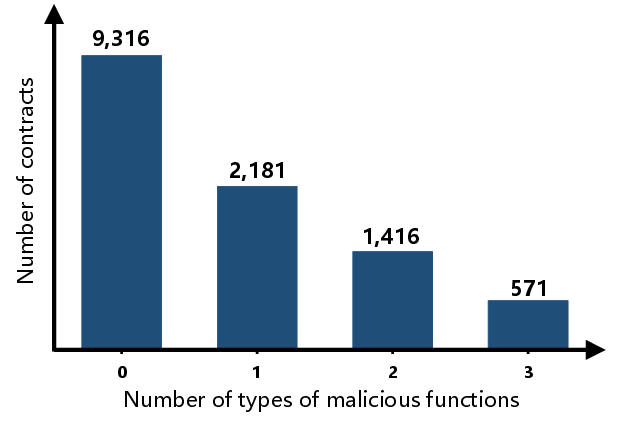
Abstract: In recent years, Decentralized Finance (DeFi) grows rapidly due to the development of blockchain technology and smart contracts. As of March 2023, the estimated global cryptocurrency market cap has reached approximately $949 billion. However, security incidents continue to plague the DeFi ecosystem, and one of the most notorious examples is the ``Rug Pull" scam. This type of cryptocurrency scam occurs when the developer of a particular token project intentionally abandons the project and disappears with investors' funds. Despite it only emerging in recent years, Rug Pull events have already caused significant financial losses. In this work, we manually collected and analyzed 103 real-world rug pull events, categorizing them based on their scam methods. Two primary categories were identified: Contract-related Rug Pull (through malicious functions in smart contracts) and Transaction-related Rug Pull (through cryptocurrency trading without utilizing malicious functions). Based on the analysis of rug pull events, we propose CRPWarner (short for Contract-related Rug Pull Risk Warner) to identify malicious functions in smart contracts and issue warnings regarding potential rug pulls. We evaluated CRPWarner on 69 open-source smart contracts related to rug pull events and achieved a 91.8% precision, 85.9% recall and 88.7% F1-score. Additionally, when evaluating CRPWarner on 13,484 real token contracts on Ethereum, it successfully detected 4168 smart contracts with malicious functions, including zero-day examples. The precision of large-scale experiment reach 84.9%.
- A. Buldas, D. Draheim, M. Gault, and M. Saarepera, “Towards a foundation of web3,” in International Conference on Future Data and Security Engineering. Springer, 2022, pp. 3–18.
- A. Buldas, D. Draheim, M. Gault, R. Laanoja, T. Nagumo, M. Saarepera, S. A. Shah, J. Simm, J. Steiner, T. Tammet et al., “An ultra-scalable blockchain platform for universal asset tokenization: design and implementation,” IEEE Access, vol. 10, pp. 77 284–77 322, 2022.
- (May, 2022) Web3 is our chance to make a better internet. [Online]. Available: https://hbr.org/2022/05/web3-is-our-chance-to-make-a-better-internet
- (May, 2022) What is web3? [Online]. Available: https://hbr.org/2022/05/what-is-web3
- S. M. Werner, D. Perez, L. Gudgeon, A. Klages-Mundt, D. Harz, and W. J. Knottenbelt, “Sok: Decentralized Finance (Defi),” arXiv preprint arXiv:2101.08778, 2021.
- (March, 2023) Coinmarketcap. [Online]. Available: https://coinmarketcap.com/
- P. Daian, S. Goldfeder, T. Kell, Y. Li, X. Zhao, I. Bentov, L. Breidenbach, and A. Juels, “Flash boys 2.0: Frontrunning in Decentralized Exchanges, Miner Extractable Value, and Consensus Instability,” in 2020 IEEE Symposium on Security and Privacy (SP). IEEE, 2020, pp. 910–927.
- K. Qin, L. Zhou, B. Livshits, and A. Gervais, “Attacking the Defi Ecosystem with Flash Loans for Fun and Profit,” in Financial Cryptography and Data Security: 25th International Conference, FC 2021, Virtual Event, March 1–5, 2021, Revised Selected Papers, Part I. Springer, 2021, pp. 3–32.
- B. Mazorra, V. Adan, and V. Daza, “Do not Rug on Me: Leveraging Machine Learning Techniques for Automated Scam Detection,” Mathematics, vol. 10, no. 6, p. 949, 2022.
- Chainalysis, “The 2022 Crypto Crime Report,” Tech. Rep., 2022.
- P. Xia, H. Wang, B. Gao, W. Su, Z. Yu, X. Luo, C. Zhang, X. Xiao, and G. Xu, “Trade or Trick? Detecting and Characterizing Scam Tokens on Uniswap Decentralized Exchange,” Proceedings of the ACM on Measurement and Analysis of Computing Systems, vol. 5, no. 3, pp. 1–26, 2021.
- (March, 2023) Rugdoc. [Online]. Available: https://rugdoc.io/
- (March, 2023) Peckshieldalert. [Online]. Available: https://twitter.com/PeckShieldAlert
- (March, 2023) Showmist. [Online]. Available: https://hacked.slowmist.io/
- P. De Giovanni, “Blockchain and Smart Contracts in Supply Chain Management: A Game Theoretic Model,” International Journal of Production Economics, vol. 228, p. 107855, 2020.
- F. Schär, “Decentralized Finance: On Blockchain-and Smart Contract-based Financial Markets,” FRB of St. Louis Review, 2021.
- (March, 2023) Ethereum virtual machine (evm). [Online]. Available: https://ethereum.org/en/developers/docs/evm/
- (March, 2023) Etherscan. [Online]. Available: https://etherscan.io/
- (May, 2022) Why build in web3. [Online]. Available: https://hbr.org/2022/05/why-build-in-web3
- F. Fang, C. Ventre, M. Basios, L. Kanthan, D. Martinez-Rego, F. Wu, and L. Li, “Cryptocurrency Trading: A Comprehensive Survey,” Financial Innovation, vol. 8, no. 1, pp. 1–59, 2022.
- (December, 2020) Create and deploy a defi app. [Online]. Available: https://ethereum.org/ph/developers/tutorials/create-and-deploy-a-defi-app/
- (January, 2023) Erc-20 token standard. [Online]. Available: https://ethereum.org/en/developers/docs/standards/tokens/erc-20/
- (March, 2023) Rug pull. [Online]. Available: https://academy.binance.com/en/glossary/rug-pull
- (Jan, 2024) Crypto rug pulls: What are they and how to avoid them. [Online]. Available: https://www.coindesk.com/learn/crypto-rug-pulls-what-are-they-how-to-avoid-them/
- (May, 2022) Crypto rug pulls: What is a rug pull in crypto and 6 ways to spot it. [Online]. Available: https://cointelegraph.com/explained/crypto-rug-pulls-what-is-a-rug-pull-in-crypto-and-6-ways-to-spot-it
- (May, 2022) What is a soft rugpull vs a hard rugpull? [Online]. Available: https://www.certik.com/zh-CN/resources/blog/X4EVjXB5HRho9jIKku544-what-is-a-soft-rugpull-vs-a-hard-rugpull
- (March, 2023) Bnb smart chain explorer. [Online]. Available: https://bscscan.com/
- (March, 2023) Fantom blockchain explorer. [Online]. Available: https://ftmscan.com/
- J. Chen, X. Xia, D. Lo, J. Grundy, X. Luo, and T. Chen, “Defining Smart Contract Defects on Ethereum,” IEEE Transactions on Software Engineering, vol. 48, no. 1, pp. 327–345, 2020.
- S. Yang, J. Chen, and Z. Zheng, “Definition and detection of defects in nft smart contracts,” arXiv preprint arXiv:2305.15829, 2023.
- PeckShieldAlert. (May, 2022) Nekogold and pokemoney. [Online]. Available: https://twitter.com/PeckShieldAlert/status/1530122357125181441
- (November, 2021) ‘squid game’-inspired cryptocurrency that soared by 23 million percent now worthless after apparent scam. [Online]. Available: https://ethereum.org/ph/developers/tutorials/create-and-deploy-a-defi-app/
- RugDocIO. (February, 2022) Gold mine finance hard rug. [Online]. Available: https://twitter.com/rugdocio/status/1494737976819163139?s=21
- PeckShieldAlert. (April, 2022) Maxapy finance. [Online]. Available: https://twitter.com/PeckShieldAlert/status/1516676658350428160
- ——. (June, 2022) Elonmvp. [Online]. Available: https://twitter.com/PeckShieldAlert/status/1536223027717111808
- ——. (June, 2022) Babyelon. [Online]. Available: https://twitter.com/PeckShieldAlert/status/1534398198957088775
- ——. (June, 2022) Starman. [Online]. Available: https://twitter.com/PeckShieldAlert/status/1532238908716593153
- (October, 2021) Solana nft “iconics” defrauds people of 130,000 in sol. [Online]. Available: https://cryptoslate.com/solana-nft-iconics-defrauds-people-of-130000-in-sol/
- Openzeppelin. (March, 2023) Proxy upgrade pattern. [Online]. Available: https://docs.openzeppelin.com/upgrades-plugins/1.x/proxies
- (Aug, 2021) Upgradable smart contracts: Doesn’t this mean anyone can add a backdoor / rug pull? seems to go against the whole immutability concept of a blockchain. [Online]. Available: https://www.reddit.com/r/CryptoTechnology/comments/p5rr5t/upgradable_smart_contracts_doesnt_this_mean/
- N. Grech, L. Brent, B. Scholz, and Y. Smaragdakis, “Gigahorse: Thorough, Declarative Decompilation of Smart Contracts,” in 2019 IEEE/ACM 41st International Conference on Software Engineering (ICSE). IEEE, 2019, pp. 1176–1186.
- (May, 2019) [yul] re-introduce sub opcode. [Online]. Available: https://github.com/ethereum/solidity/issues/6765
- F. Ma, M. Ren, L. Ouyang, Y. Chen, J. Zhu, T. Chen, Y. Zheng, X. Dai, Y. Jiang, and J. Sun, “Pied-piper: Revealing the Backdoor Threats in Ethereum ERC Token Contracts,” ACM Transactions on Software Engineering and Methodology, 2022.
- (Jan, 2024) Confidence interval. [Online]. Available: https://en.wikipedia.org/wiki/Confidence_interval
- S. Kalra, S. Goel, M. Dhawan, and S. Sharma, “Zeus: Analyzing Safety of Smart Contracts.” in Ndss, 2018, pp. 1–12.
- L. Luu, D.-H. Chu, H. Olickel, P. Saxena, and A. Hobor, “Making Smart Contracts Smarter,” in Proceedings of the 2016 ACM SIGSAC conference on computer and communications security, 2016, pp. 254–269.
- B. Jiang, Y. Liu, and W. K. Chan, “Contractfuzzer: Fuzzing smart contracts for vulnerability detection,” in Proceedings of the 33rd ACM/IEEE International Conference on Automated Software Engineering, 2018, pp. 259–269.
- P. Praitheeshan, L. Pan, J. Yu, J. Liu, and R. Doss, “Security Analysis Methods on Ethereum Smart Contract Vulnerabilities: A Survey,” arXiv preprint arXiv:1908.08605, 2019.
- T. Chen, X. Li, X. Luo, and X. Zhang, “Under-optimized Smart Contracts Devour Your Money,” in 2017 IEEE 24th international conference on software analysis, evolution and reengineering (SANER). IEEE, 2017, pp. 442–446.
- L. Brent, A. Jurisevic, M. Kong, E. Liu, F. Gauthier, V. Gramoli, R. Holz, and B. Scholz, “Vandal: A Scalable Security Analysis Framework for Smart Contracts,” arXiv preprint arXiv:1809.03981, 2018.
- N. Grech, M. Kong, A. Jurisevic, L. Brent, B. Scholz, and Y. Smaragdakis, “Madmax: Surviving Out-of-gas Conditions in Ethereum Smart Contracts,” Proceedings of the ACM on Programming Languages, vol. 2, no. OOPSLA, pp. 1–27, 2018.
- L. Brent, N. Grech, S. Lagouvardos, B. Scholz, and Y. Smaragdakis, “Ethainter: a Smart Contract Security Analyzer for Composite Vulnerabilities,” in Proceedings of the 41st ACM SIGPLAN Conference on Programming Language Design and Implementation, 2020, pp. 454–469.
Paper Prompts
Sign up for free to create and run prompts on this paper using GPT-5.
Top Community Prompts
Collections
Sign up for free to add this paper to one or more collections.